Torrenting refers to the distribution and downloading of files through the BitTorrent protocol. Because of its nature, the process is well-suited for exchanging otherwise large files. However, it is essential to note that torrent clients expose your IP address to many privacy risks. Torrenting reveals your IP address to every other user involved in exchanging files.
This guide will explore possible torrent privacy flaws, their consequences, and how to be safe while torrenting with a VPN.
Torrent privacy risks that pose a threat to most users

We must look deeper into the torrenting world and what that means for you and your device. Below, you will find the major risks that come with torrenting at all times:
1. Malware risks
Malicious individuals roam the internet, and with places like the torrent protocol, you can’t tell who is lurking in disguise in the torrent swarm. These ill-meaning users can plant malicious software in a torrent file that, after downloading, can severely damage your computer or silently eat it from the inside out.
We recommend installing an antivirus to scan and keep out any hidden malware. You will find a built-in antivirus feature for most torrent clients to prevent infection.
2. Personal data security
To be clear, when you use the P2P network, you only grant access to the files you sorted and saved in the destination folder you wish to interact with. The remaining users in the torrent swarm cannot access your entire computer. The only way to risk your data leaking would be to save personal information in the designated folder.
3. Breaking the law
With torrenting, we recommend downloading non-copyrighted content so that it is not on the opposite side of the law. Torrenting and even downloading copyrighted content is considered illegal, regardless of your location. We don’t recommend torrents to download or share copyrighted content, as it can attract jail time or hefty fines.
4. Exposing yourself to cyber criminals
Lastly, another risk of using torrents is exposing your online identity to others in the torrent swarm and, unfortunately, hackers. Because by the torrent protocol, your IP address is exposed to strangers, and you cannot trust these strangers to have your best interests at heart.
In light of this, we recommend using a VPN and a compatible antivirus whenever you wish to use the torrent network. Hackers, snoopers, and data thieves are lurking and looking for a way in; your duty is to keep them out with some help.
What is an IP leak?
An IP leak occurs when your real IP address is visible to whoever cares enough to look. However, IP leaks are not the only types you can encounter; there are also WebRTC and DNS leaks. These leaks can reveal your personal information, which can expose you to many risks.
For this reason, we recommend using a VPN, which is secure and offers a much more stable connection. It is important to mention that the best option for VPNs is a paid premium one, such as NordVPN.
What is a DNS leak?
Accessing any website, such as Facebook, is not as straightforward as just entering a URL to connect; your computer sends information packets to a DNS server, which will then ask for the website’s IP address. This result manifests as access to the desired website.
When you embark on this process without a VPN, you do so with your ISP’s DNS servers. By this, your online activity gets logged in plain, observable text. Per regulations, the ISP can keep records of these online activities, and some can even share them with the authorities in the event of an investigation by law enforcement.
Fortunately, with a VPN, the DNS requests are encrypted and routed through private servers. Unlike a non-VPN connection, your ISP gets barred from observing your online activities. But if these requests get routed to your ISP even when connected to a VPN, this is called a DNS leak.
A DNS leak does not expose you to too much trouble but can help streaming platforms block you from accessing them outside the geo-restrictions. At the same time, a VPN can keep you safe from leaks, whether it’s DNS, WebRTC, or IP. VPN services like NordVPN and ExtremeVPN utilize dedicated DNS servers and actively check for leaks.
What’s an IP address?

Your IP address is a unique number that acts as an online ID, often assigned by your ISP. Every website you visit has an IP address, but to you, it is represented as a website name on your browser.
Let’s walk through a scenario to give this more context. When you run a search query, you would, of course, use Google.com. To you, you are accessing it via its URL, but your computer searches for Google.com through its IP address (74.125.141.104). It is also important to point out that IP addresses can be public or private.
Who can see your IP address when torrenting?
During torrenting, you access the protocol using a torrent client. When you do this, your IP address is visible to every user. Torrenting involves joining a P2P (peer-to-peer) network or what gets referred to as a “torrent swarm.”
Within this swarm are other users such as yourself. When any one of you opens a torrent file, their torrent client will seek out everyone else’s IP address there. This happens so that every computer involved in the exchange can work together and create what is referred to as a “peer-to-peer” chain. In this setup, each computer acts as a server, helping to “seed” the files.
Thus, every user in the torrent swarm can see your IP address, and with that information, anyone in the swarm can access your actual location, especially your ISP. Hackers can do unthinkable damage to you with just that information; you would do well to keep it private and hidden.
Why hide your torrent IP?
As mentioned earlier, your IP address is your device’s ID, with which your ISP can find your real identity and where you live. However, this should not be an issue if you only use legal torrenting apps or clients unless there are laws against torrenting where you reside.
And, of course, these laws would exist to curb the torrent of copyrighted content. If you go against those laws, you could expose yourself to legal risks. To be clear, torrenting copyrighted content is illegal, no matter where you are. So when you torrent, you risk both legal and personal consequences.
But we cannot fail to mention the biggest risk of all: the potential for hackers to access your computer using your IP address and cause irreparable damage. So, next time you wish to use the torrent protocol, be aware of the risks you agree to encounter when you do so without a VPN.
How to torrent anonymously

As discussed earlier, you can torrent safely and privately; first, you need a VPN and a legal and trusted torrent client.
The VPN has servers to which it routes your internet traffic. It is from these dedicated servers that the VPN offers you a new IP address to replace your real IP address. If your ISP were to look into your internet activities or the destination website you wish to access, they would not see your real IP address.
How to torrent safely

Torrenting can be risky, but it does not have to be that way; we can show you how to minimize the risks. Before we do that, we would like to reiterate that this article aims to help you torrent safely; it does not encourage the torrent of copyrighted content.
Anyway, if you want to torrent safely, then do the following things:
- Use a trusted torrent client software that comes with a built-in antivirus
- Do not torrent copyrighted content
- Use a premium VPN like NordVPN or ExtremeVPN to protect your IP address
Also, choosing a reliable and safe option for torrenting safely and anonymously is important. We have listed the best websites for torrenting without a worry in this article. However, taking extra precautions or safety measures while doing any task online is always recommended.
What is the best VPN for torrenting?

We picked the best VPNs for torrenting: NordVPN and ExtremeVPN. These two options are excellent for torrenting because they have dedicated servers for P2P and also offer healthy privacy protocols. You don’t need to worry about leaks; both VPNs cover IP, DNS, and WebRTC leaks.
1. NordVPN

One of the most trusted VPNs for safe torrenting. It masks your real IP address and replaces it with another, making it difficult for hackers and government agencies to find you.
Pros
- Allows Peer-to-Peer trafficking
- Most advanced security protocols
- Doesn’t throttle bandwidth
Cons
- The OpenVPN configuration isn’t easy to navigate
NordVPN presents a world of benefits when it comes to torrenting. Firstly, it can block your ISP from discovering if you downloaded copyrighted content accidentally, and it can also prevent throttling imposed by your internet service provider.
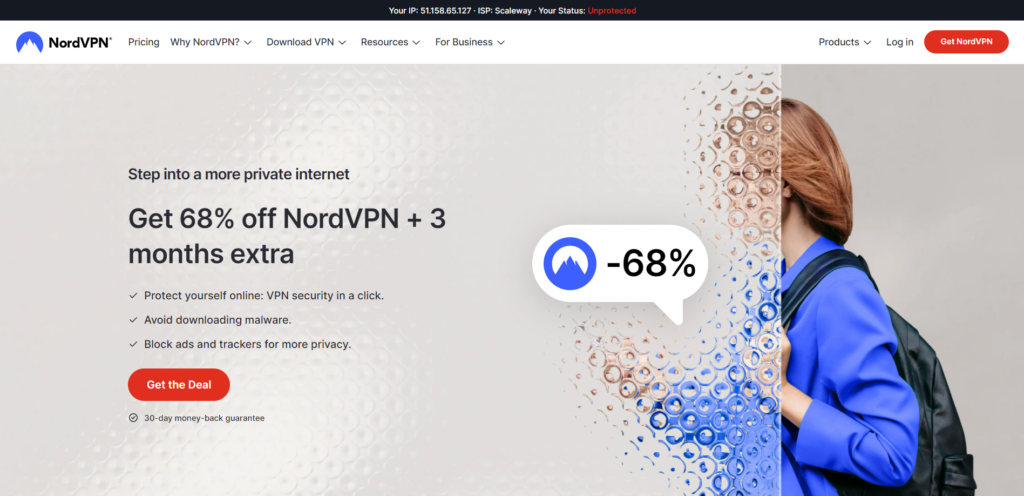
It will encrypt your data, preventing your ISP from detecting your P2P connections and allowing for much higher speeds. Regarding privacy, this VPN utilizes AES-256 encryption to encrypt your online traffic, making it impossible to track. Also, you can download torrents with this VPN without hassle.
You can also rely on VPN’s improved version of the WireGuard tunneling protocol, NordLynx. And, of course, there is a handy kill switch on hand to shut down the internet connection as soon as there is any hint of the VPN disconnecting.
There is also split tunneling to pick and choose which apps you want to be protected and which you wish to stay the same. Lastly, the privacy policy states that it will not collect or store any private user data.
2. ExtremeVPN

An easy-to-use VPN provider that ensures maximum security and anonymity while torrenting from unreliable sources.
Pros
- Makes users’ data private and hard to crack
- Doesn’t limit bandwidth
- An extensive server network
Cons
- Lacks special dedicated IP addresses
ExtremeVPN is another perfect choice for torrenting, and it makes its case for many reasons, too. First, users can say goodbye to bandwidth limitations; VPN has unlimited bandwidth.
As said earlier, VPNs have dedicated servers for torrenting, but with a twist. There are no restrictions on how many you can use, so wherever you are, you can access any available servers for torrenting.
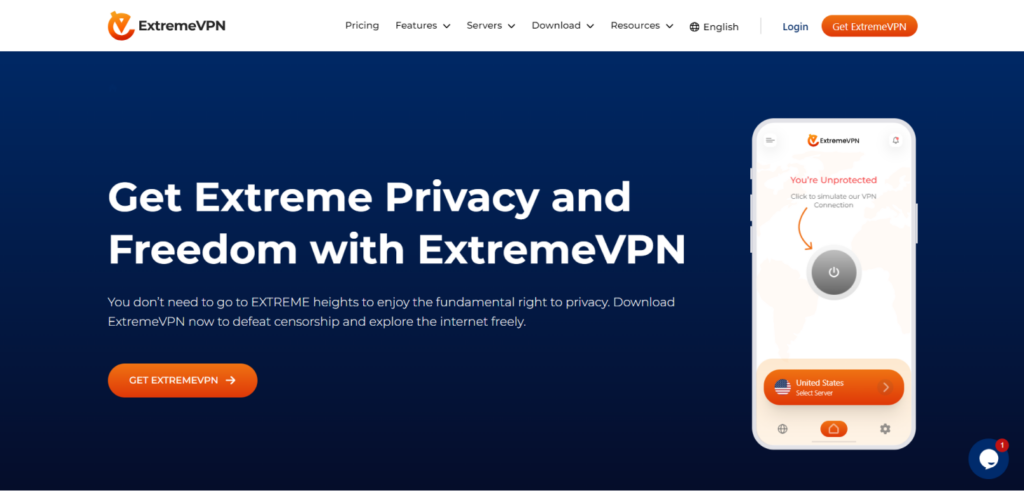
It is fast; it is literally in the name. This is awesome for torrenting; whenever you connect to any of the servers, you should experience a negligible dip in speed and a smooth torrenting and streaming process.
This VPN has a strict no-logs policy for privacy and sticks to it. They have also had external audits done. The service uses military-grade AES-256 encryption, which is practically impossible to crack. All these features ensure that your torrenting is always smooth, safe, and fast.
How to check for IP leaks

You can check your IP address online to ensure you do not have any leaks. Many websites allow you to ascertain if you have any IP leaks, including DNS leaks. If you use one to check and you can see your actual location, you are experiencing an IP leak.
Checking for IP leaks can feel tedious, but protecting our privacy is important.
Let’s start with the DNS test since that’s one of the trickiest issues. DNS is like the internet phonebook, translating domain names into IP addresses. We want to check that our VPN’s phonebook is being used rather than our provider’s. A simple DNS leak test will reveal any coverage gaps.
While we’re at it, we should also have a peek to see if WebRTC is tattling on us without permission. Browserleaks.com can check that. If it is, a quick browser setting tweak stops gossip!
And, of course, we’ll want to double-check that our IP address matches our VPN server’s location, not our actual location. Our IP address tool makes that an easy check.
FAQs
If your IP leaks and a hacker is aware, then yes. They could then use phishing attacks to pose as government officials to ask for more personal details. Once they get enough data, they can sell your identity on the dark web.
Yes, a VPN switches out your real IP address for another. The new IP address is elsewhere, so whoever is looking will see you in this new place instead of your real location.
All you need to do is check if there are any unsanctioned changes to your settings, any unauthorized connections, or unexplained chunks of data used. You can check all this automatically using security software.
You can do this in a few ways, but we recommend the surefire way: a VPN. When you get a VPN, your security worries are over, thanks to excellent encryption and formidable security protocols.