AES encryption is one of the most widely used and trusted security standards in the world today. Short for Advanced Encryption Standard, AES protects everything from online banking transactions and government data to VPN connections and encrypted messaging apps.
But while you see “AES-256” mentioned everywhere, few people actually understand what it means or how it keeps information secure. At its core, AES is a symmetric encryption algorithm designed to transform readable data into unreadable code using complex mathematical operations.
This guide explains what AES encryption is, how it works, and why it remains the gold standard for protecting sensitive information against modern cyber threats.
What is AES encryption?
Advanced standard encryption, technically referred to as Advanced Encryption Standard (AES), is a safe and fast cipher that keeps your data away from the prying eyes.
Technically, it is the symmetric form of encryption where only a single key ciphers and deciphers the data. While this sounds simple, what makes AES the gold standard is the application of multiple rounds of encryption, which makes the algorithm impossible to penetrate.
Currently, AES is the only NSA-approved cipher available for public access.
Owing to its usefulness and security, AES presently backs numerous sectors where encryption is needed. These include hardware technologies, social media, VPNs, data protection tools, and even messaging apps like Signal and WhatsApp.
How does AES encryption work?
Understanding encryption algorithms, especially the more complicated ones like AES, isn’t easy. As you would expect from any computing program, AES also involves lots of maths revolving around binary codes (lots of 0’s and 1’s) that would be hard to explain.
Nonetheless, to make things easy, here is a simpler (or maybe rudimentary) explanation of the general processes that constitute the AES functionality. I hope this will surely give you an idea of how the actual encryption takes place on computers.
1. Divide information into blocks
Note that AES is a block cipher and not a stream cipher. Here, the first action point is that plaintexts (information for encryption) are divided into blocks of bits rather than bit-by-bit.
AES has a 128-bit block size. Hence, it divides the information into 4 x 4 columns of 16 bytes (a byte contains eight bits. Hence, 16 multiplied by 8 equals 128).
For example, if you have a message that says, “Get me some water, please.” The initial block will look something like this:
| g | m | 0 | w |
| e | e | m | a |
| t | e | t | |
| s | e |
You can see this block doesn’t include the entire message. That’s because the part until “wate” has filled up the first block. So, the rest of the message (from the “r” of “water”) will constitute the second block. The blocks will continue to add up until your message is complete.
Since this is just an example explaining the basic concept, let’s focus only on the first block. The process explained below will apply to all the subsequent blocks as well. (If you’re curious to know what happens, you can take this as an exercise to encrypt the other blocks. That’ll surely be fun.)
2. Key expansion
Here, the first key is taken and used to derive other keys suitable for all-around encryption. It is a vital step. It derives new 128-bit keys using Rijndael’s key, which is an easy way of producing key ciphers.
For instance, if the initial key is “kids are smarter”, this is how it would look before key expansion:
| k | s | t | |
| i | a | m | e |
| d | r | a | r |
| s | e | r |
After key expansion (using Rijndael’s key schedule), it will likely appear thus:
| 25 | 39 | 2i | t6 |
| i0 | 9g | tu | 9g |
| hs | 3i | ir | 84 |
| kt | ek | eg | ic |
While the above may seem as though they are arbitrary characters, that isn’t the case. Rijndael’s key schedule applies structured processes to encrypt each of the keys. I shall discuss the usefulness of each round key later on.
3. Round key addition
This step marks the beginning of AES encryption. In this stage, the algorithm combines the original key to the phrase, which was previously converted into a 4 x 4 block:
| g | m | o | w |
| e | e | m | a |
| t | e | t | |
| s | e |
+
| k | s | t | |
| i | a | m | e |
| d | r | a | r |
| s | e | r |
We can add both phrases using the XOR cipher, an algorithm used for adding encryption.
Although adding the two blocks of text may seem impossible, note that AES uses binary code. The characters you see are just a substitute to make it easy to understand. Typically, after encryption, what you get after adding the two blocks is a different block of the cipher. Let’s represent the mathematical operation thus:
| i4 | he | zv | 8t |
| t9 | 8e | 37 | 3m |
| eh | 5c | 9e | 9d |
| 85 | fm | 3i | ih |
4. Byte substitution
Here, the AES algorithm replaces each byte with a code gotten from an already pre-determined table. The table called Rijndael S-box looks like the table below:
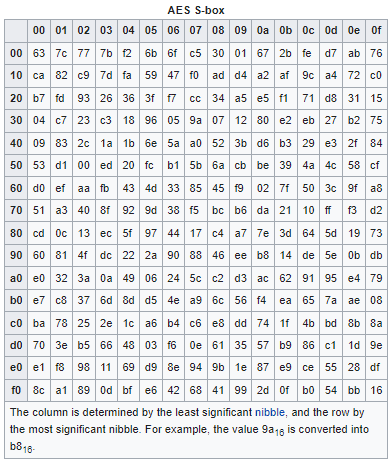
It is a complicated system with no specific logic. The algorithm uses the established table to get the code. For example, dj turns to 62, h3 turns to jb, s8 turns to 9f, etc. Therefore, after the byte substitution, the block of cipher may look like the representation below (note that this is only a hypothetical representation of what the real situation is):
| ic | m4 | lg | m3 |
| 9g | kk | 2i | kt |
| 85 | xi | 0e | 29 |
| it | 28 | e7 | qy |
You will notice I underlined the characters in the last column from the table above, while the second column is in bold letters. This will be useful in the following steps.
5. Shift rows
As the name implies, it simply involves shifting the rows of the block obtained from the byte substitution process.
While the first row remains intact, the next one shifts one step leftwards by a byte, the next row moves two steps leftwards by two bytes, and the one after that also shifts three steps leftwards by three bytes. Thus, giving us:
| ic | m4 | kf | m3 |
| kk | 2i | kt | 9g |
| 0e | 29 | 85 | xi |
| qy | it | 28 | e7 |
6. Column mix
This involves a lot of advanced mathematics and is a bit complicated to explain. However, what happens is that each step multiplies every column using a pre-established matrix. This gives birth to a new block of code.
For simplicity, assume the mathematical calculation gives the result below:
| mt | k5 | 3m | nb |
| 94 | 39 | If | 9g |
| 0x | yn | 4m | n5 |
| 6c | b0 | 4k | qt |
7. Round key addition
Remember the keys achieved at the key expansion segment? It’s time to make use of them. I will add it to the outcome of the mixed column:
| mt | k5 | 3m | nb |
| 94 | 39 | If | 9g |
| 0x | yn | 4m | n5 |
| 6c | b0 | 4k | qt |
+
| 25 | 39 | 2i | t6 |
| i0 | 9g | tu | 9g |
| hs | 3i | ir | 84 |
| kt | ek | eg | ic |
The addition of these two produces another block of binary code, which may be depicted as:
| 0e | 6c | 38 | tg |
| mt | eg | ij | 4c |
| 9u | 39 | iq | 8g |
| 73 | 8e | 26 | bg |
This further goes through another round of modifications to produce yet another result.
8. Process repetition
After the previous step, the process repeats.
That is, after adding the last key, it goes through the byte substitution phase. From there, it goes back to row shift, moving every row leftwards by a space, two spaces, and three spaces, respectively. Once done, it’s back to the column mix stage and round key addition again.
I mentioned earlier that AES features various key sizes, including 128, 192, and 256 bits. Using the 128-bit takes you through nine rounds, while for the 192-bit, it’s eleven rounds. Also, for the 256-bit key, the number of circles is thirteen.
Hence, this means if it’s a 256-bit, then the data will pass through byte substitution, row shift, column mix, and round key addition thirteen times for each of them (with the characters undergoing alteration at each stage).
When these nine, eleven, or thirteen rounds are done, it goes through one more round. But unlike the usual round, the data only goes through byte substitution, shift rows, and round key addition, but not column mix. The reason for skipping the mix column stage is that it doesn’t alter the data. Rather, it only consumes processing power and reduces the encryption efficiency.
For easy assimilation, here is a summary of the whole AES encryption procedure:
- Key expansion
- Round key addition
- Byte substitution
- Row shift
- Column mix
- Round key addition
The last four steps happen nine, eleven, or thirteen times in rounds. (depending on the key size, i.e., 256, 192, or 128-bit)
- Substitution of a byte
- Row shift
- Round key addition
After all these complex processes, your initial text, “get me some water please,” ends up becoming “pl34c8b0j4k 394vjwmg09wt98b”. While it might appear an arbitrary string of characters, the example shows that the result comes from applying mathematical operations repeatedly.
What is AES encryption used for?
After going through all the technicalities, it is worth knowing why encryption in itself is necessary.
The most elementary reason you need encryption is that it enables users to encode data such that just those with the key can decipher the information. The information will look like gibberish to those without access to the key. On the other hand, to those with the key, nothing seems strange as the string of random characters converts into a meaningful message.
Besides, the government and military have been using encryption for decades to prevent delicate information from being possessed by the wrong persons. But more personally, in the last few years, it has penetrated our everyday lives and has now become a massive part of our online world.
Imagine all the information that you input into your device from time to time: bank details, private messages, emails, passwords, and so on. Without any form of encryption in place, this data would have been easily interceptable by anyone—be it the government, stalkers, or cybercriminals.
You have tons of sensitive and valuable information that you do not want to fall into the wrong hands. Hence, it’s clear that you need to protect it such that only you or those you allow can access it.
In short, without encryption, the online world wouldn’t exist. A realm without encryption strips users of security and privacy, clearly making the idea of online existence a mess!
Why the need for AES? Quick retrospective look
Earlier, encryptions weren’t complicated. People used simple tricks and techniques, such as changing the letters to the next alphabet in a sentence, to decipher a message. However, as the old methods became known, people had to encounter complications.
As seen above, the code appears unreadable. But despite its apparent unreadability, someone knowing that it’s a code and not gibberish would likely figure it out.
With people becoming more tech-savvy, encryption has evolved and become more complex to meet consumers’ demands. This eventually led to interesting inventions like Enigma machines (cipher devices) that first appeared in 1918 when Arthur Scherbius (a German inventor) patented its primitive design.
Rise and fall of DES encryption
During the 1970s, the United States National Bureau of Standards (NBS) adopted Data Encryption Standard (DES) as a means to encrypt sensitive government data. DES was a symmetrical key algorithm created by IBM that served well for a few decades. However, given the rise in security risks, the effectiveness of DES began to diminish until the 90s.
One of the limitations of DES was that it featured a 56-bit key. (This is a shortfall to the 256-bit encryption known with AES today). So, with more technological advancement and better ways of cracking systems, it became feasible to attack DES.
The first successful DES encryption hack happened in 1997 by DESCHALL Project during a security competition led by Rocke Verser.
Another successful attempt occurred in 1998 when the EFF developed a DES breaker to carry out a brute force attack in approximately two days. Still, a year after that, the Electronic Frontier Foundation, in collaboration with distributed.net, reduced the cracking time to merely 24 hours.
While the attacks were expensive and not sustainable, it became apparent that the reign of DES as the number one encryption was over. As Moore’s law puts it, the exponential increase in computing prowess exposed the weaknesses of DES encryption.
The arrival of AES encryption
Since DES was no longer reliable, the U.S once again set out in search of new standard encryption they could adopt. This time, the duration of search and evaluation of existing encryptions was put at five years.
In 2001, the good news arrived. TheNational Institute of Standards and Technology (NIST) proclaimed it had made a suitable selection.
The encryption chosen was a tool developed by Belgium cryptographers Joan Daemen and Vincent Rijmen. It was a subset of the Rijndael block cipher, which has key sizes 128-bits, 192-bits, and 256-bits along with 128-bits block size.
Finally, after much testing, the U.S government in May 2002 approved AES as the federal government’s standard encryption, and before long, other countries adopted it as its standard encryption algorithm, too.
Why was Rijndael block Cipher selected for AES?
Encryptions always involve give and take. Although, it’s possible to have encryption that is more secure than AES. However, it would have little practicability given the long duration for it to encrypt and decrypt. The RSA cipher addresses this problem without compromising the effectiveness of encryption.
In essence, the National Institute of Standards and Technology chose this cipher because of its overall ability, including its excellent performance on hardware, software and its increased safety and ease of implementation.
How is each step relevant?
During data encryption, a lot happens. yet every step happens for a reason.
The first step, which is the key expansion step, is crucial. It produces the key used in later circles. Without it, for every round, the same key gets added, making AES easier to break. In the initial step, your plain text begins alteration after the key has been added.
The second stage is the byte substitution, another important stage. Here, a pre-determined table is used to change each data point. Doing this changes the information in an unsystematic way; this is done to confuse the data. Confusion refers to a deliberate process applied to conceal the affiliation between an initial text and the encrypted data.
Another very critical stage is the shift rows stage; this stage performs a task called diffusion. In the world of cryptography, diffusion is the process of transposing data to make it more complicated. The information is changed from its initial position to another position to obscure the information further by row shift.
On the other hand, column mix has similar functionality, but here it alters the information vertically and not horizontally.
Upon concluding one round, another round key (gotten from the original key) is added. This is done to further confuse the data.
Why AES encryption involves so many rounds?

Despite the tons of processes, including byte substitution, round key addition, column mix, and row shift which alter the original information, AES encryption can be broken by expert cryptanalysis (a process of studying algorithms to decrypt it).
There are also shortcut attacks to worry about. This type of attack can break encryption easier than brute force. Upon designing the encryption security strength, the developers found shortcut attacks in at least six stages of the entire process.
Given this threat, four additional rounds were then added, bringing the minimum-security margin to 128-bit. The 10 rounds resulting from this addition gave AES enough fortification to avert shortcut attacks and has remained so even in today’s technology.
Wouldn’t it be better to add extra circles to strengthen security?
Like other security features, a balance between usability, performance, and defensive strength is needed. It’s like placing ten metal doors with bolts at every entry and exit point to your home. While it would make it very secure, it will take a ludicrous amount of time to enter and exit; hence, no one would.
It’s the same with encryption. Yes, it could be made safer by including extra circles, but the process would become slow and inefficient. Thus, developers have settled on ten, twelve, and fourteen AES rounds of encryption because they create a balance in all the key aspects, especially in today’s technological space.
Decrypting AES
Were you able to get all I have explained on AES encryption thus far? If yes, then decryption would be relatively easier to understand. Here, it uses inverse encryption to reverse AES ciphertext back to its original state.
As stated earlier, AES makes use of symmetric cryptography. In simpler terms, it means that it uses the same key for encryption and decryption of data.
This is different from algorithms that utilize asymmetric encryption, which uses both private and public keys.
In this case, moving from the code “pl34c8b0j4k 394vjwmg09wt98b” to the original plaintext “get me some water please,” carry out the entire in reverse, applying the reverse of each encryption process.
Therefore, the decryption process begins with the reverse round key addition, next is the reverse row shift, and then reverse byte substitution. After that, it moves to the reverse of the nine, eleven, and thirteen rounds. Overall, it will look something like this:
- Reverse round key addition
- Reverse row shift
- Inverse byte substitution
- Reverse round key addition (again)
- Inverse column mix
- Reverse row shift (again)
- Inverse byte substitution (again)
the latter four happening nine, eleven, or thirteen times (depending on the size of the keys, i.e., 128, 192, or 256-bit)
- Reverse round key addition
After the key is decrypted, you will have your original message back— “get me some water, please.”
128-bit vs. 192-bit vs. 256-bit advanced encryption standards
As you already know, AES features three encryption lengths. The major difference between all three is the number of circles that information goes through during encryption; it can either be ten, twelve, and fourteen. Thus, 192-bit provides more security edge than 128-bit, while 256-bit have more security margin 192-bit and 128-bit.
In the present technological world, 128-bit is no longer sufficient for use. The more sensitive information like top-secret files, which have advanced threat levels, is safer being processed with 256 or 192-bit AES.
It’s not necessary to use 192-bit or 256-bit to encrypt personal or less critical data as 128-bit will do. But if you would instead go for it, then that’s fine. Note, though, that it comes with its own cost. For instance, 256-bit has four extra circles more than 128-bit, thereby making it 40% less efficient.
Are there any security issues with AES encryption?
Right now, AES remains an exceptionally secure encryption model. But this may not remain the same a few years from now.
While there has been no recorded real-life attack yet, the fast-paced evolution of technology may pose a potential threat in no distant time.
Besides, mistakes do happen. For instance, if there is a wrong implementation of AES encryption, the potential errors from the mistake could serve as a window for a cybercriminal to hack into the system.
Fortunately, the right usage of AES prevents such successful hacks from happening.
To ensure AES remains impenetrable, cryptographers are always checking the encryption method for weaknesses. They are always developing new techniques; they also constantly utilize the technology they have come across. This is an important process, and if it’s not constantly tested by professionals, then cybercriminals or nations could find ways to break it without anyone knowing about it.
Below are some theoretical ways to crack AES encryption.
1. Related-key attacks
These attacks target the encryption key. They require less effort and time and are more likely to be successful (if ever). Related-key attacks aren’t a major concern as they can only occur if the protocol isn’t well implemented.
Even at that, there have been a few of these attacks targeted at AES encryption. The most popular attack was in 2009. To prevent a recurrence of such attacks, cryptographers further increased the complexity of the AES key schedule.
2. Key-recovery attacks
To succeed at a key-recovery attack, the hacker must have at least a pair of decrypted and encrypted texts.
To test AES resistance to cracking, cryptographers carried out a key-recovery attack in 2011. But while it didn’t yield any positive result, it only showed that it was about four times quicker than a brute-force attack (an attack that would take at least a billion years).
3. Side-channel attacks
Although several theoretical attacks have been assumed, they would have to take many years (a billion years at least) to crack. Therefore, AES at this moment is impossible to crack or break.
Regardless, it remains prone to cracking if not properly implemented, most likely, through a side-channel attack.
This type of attack happens when there is a data leak from a system. Here, an attacker collates the timing of the data, listens to sound, power consumption, or electromagnetic information. Doing this helps the attacker collate readings which he can use to crack it.
If there is a proper implementation of AES, then preventing a side-channel unprecedented attack becomes possible either by deleting the cause of the information leak or by making sure there isn’t an obvious relationship between the algorithm process and the leaked information.
| Size of Key | Likely Combination |
|---|---|
| 256-bits AES | 1.1 x 1077 |
| 192-bits AES | 6.2 x 1057 |
| 128-bits AES | 3.4 x 1038 |
| 64-bits | 1.8 x 1019 |
| 56-bits DES | 7.2 x 1016 |
| 32-bits | 4.2 x 109 |
| 16-bits | 65536 |
| 8-bits | 256 |
| 4-bits | 16 |
| 2-bits | 4 |
| 1-bit | 2 |
The table above shows the key sizes and the corresponding likely combinations needed to crack them by a brute-force attack.
Let’s take 128-bit for instance:
The number of years required to break the 128-bit key will be:
=(3.4 x 1038) [(10.51 x 1012) x 31536000] (where 10.51 x 1012 is the number of Flops per second and 31536000 is the number of seconds in a year)
=(0.323 x 1026) 31536000
= 1.02 x 1018
= 1 billion years
If it takes one billion years to decrypt 128-bit, imagine how long it would take to crack 256-bit. This only shows that AES is super-secure.
4. Known-key distinctive attacks
This is more of a general attack than focused on AES alone. However, note that using AES does not guarantee their safety. Known-key distinctive attacks can still occur if the attacker knows the user’s key (this is unlikely though).
But in 2009, hackers tried cracking AES-128 using known distinct-key. This was successful but only against the 8-round version as against the whole ten rounds of encryption. In reality, this was no real threat.
Regardless, users must ensure they keep their data secure, and AES is just a tiny part of it. With other methods such as virus detection, effective firewalls, password management, and enlightenment about social attacks, users’ data will always be kept safe.
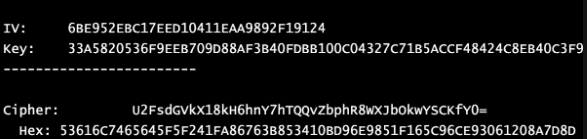
AES encryption example
There are several instances where developers can utilize AES. Here are a few examples:
- Virtual Private Networks (VPNs): A VPN secures your connection, ensures your online privacy and protection. However, it cannot achieve this without the use of an effective encryption program. Most VPNs use AES 256-bit keys to ensure there are no data leaks. Examples of such VPNs include ExpressVPN, NordVPN, and Surfshark.
- Mobile application: Many well-known apps such as Facebook Messenger and Snapchat use this encryption to safeguard their users’ sensitive information such as messages and pictures.
- Wireless networks: WiFi also makes use of this along with WPA2. But while AES is not the only type of encryption available for use, other types of encryptions are not as safe as AES.
- Operating system components: Some OS components, such as file systems, use AES to provide an extra layer of safety and security.
- Password managers: Some programs feature a lot of delicate data, and to protect this information, password managers such as NordPass and LastPass take AES implementation seriously.
- Compression and archive tools: Compression tools such as RAR, WinZip, and 7z use AES to prevent data leaks.
All the examples mentioned above do seem impressive, but they do not represent all AES are used for. AES encryption includes disk encryption systems, file systems, and web browsers.
Besides, you used AES in opening this article because your web browser is mandated to encrypt your connection with this article via SSL (HTTPS).
Is AES encryption enough?
In today’s world, a lot of sensitive information is transmitted via online means, thereby making AES a vital part of people’s security detail. While it’s existed for two decades (since 2001 precisely), the recurring process of key addition, byte substitution, row shift, and column mix has thrived for a long time.
Regardless of all the hypothetical attacks and attempted side-channel attacks, Advanced Encryption Standard remains a secure encryption method. AES encryption standard has proven to be an excellent means of securing online communication and is applicable in many cases where sensitive data requires protection.
Given its high level of cipher technologies and sophisticated techniques, rest assured that AES will serve your security needs.
FAQs
None is better than the other. While both AES and RSA encryption work differently, they often compliment each other to provide better security.
Yes, for most purposes. A brute-force attack on AES-128 would take billions of years with current technology. However, for data requiring long-term protection (decades) against future quantum or advanced attacks, AES-256 is recommended. Most systems today use AES-256 by default for this “future-proofing” margin.
