With over 100 million downloads worldwide, uTorrent has become one of the most prevalent peer-to-peer clients for file transfers. Its widespread appeal is attributed to its fast download speeds and user-friendly interface, making it a top choice among users seeking efficient torrenting powers.
However, a pressing question lies: Is uTorrent safe? In this article, we will discuss the potential risks of using it.
What is uTorrent?
It is a free software for downloading large files within a file-sharing setting. It debuted in September 2005, thanks to its creator, Luvis Strigeus. As part of the BitTorrent portfolio, the software has 100 million global users and has become popular as it works on leading mobile and desktop operating systems.
Despite its widespread popularity, uTorrent faced controversy in 2015 when many users unknowingly installed a crypto miner alongside the software. However, despite this setback, it remains one of the most used torrent clients.
How does uTorrent work?

Learning how the tool operates is crucial to understanding the potential risks associated with uTorrent and ensuring you remain safe when torrenting. Let’s delve into the key components of the process:
- Peer-to-peer (P2P): P2P enables direct file sharing between two or more people without intermediaries or third-party involvement. Through P2P sharing, data is distributed efficiently.
- Torrenting: Torrenting is a form of P2P sharing offering a different file download approach. Torrenting operates in a decentralized manner by making your data accessible to every device on the network. This decentralized nature enables faster and more efficient file sharing among peers.
- BitTorrent: This is a P2P transfer protocol designed mainly for file uploading and downloading.
- uTorrent: It is a BitTorrent client company that works on the same principle. It offers a light software solution, making it one of the most widely used BitTorrent clients.
Notably, using uTorrent to share content means becoming integral to the collective process.
Potential risks and vulnerabilities of using uTorrent

Is the torrent client putting your safety at risk? Let’s explore a detailed overview of what makes using it unsafe.
1. Unwanted software installation (Bloatware)
Since 2009, the torrent app has faced criticism for bundling various applications, causing user dissatisfaction and concerns over unwanted software. In 2010, it introduced the Conduit Engine adware, a controversial move as users reported its installation without consent and difficulty in its removal.
In 2015, another bundled software, SearchProtect, presented a similar issue regarding removal and the opt-out process. Despite several changes in the bundled software over the years, uTorrent’s policy has remained consistent, emphasizing the importance of careful installation to avoid bloatware.
Some encountered offers to install Adware Web Companion and McAfee WebAdvisor throughout the installation process. However, legitimate web security applications and their bundling with torrents raise concerns, with some antivirus programs even flagging them as Potentially Unwanted Programs (PUPs).
Complicating matters further, approval forms are cleverly masked as routine installation processes, intentionally misleading users. Additionally, it silently installs the DLive and TronTv streaming components, leaving users with unavoidable bloatware.
These extra programs have privacy policies, potentially monitoring and recording users’ downloads and behavior within the application.
2. Advertisements and data sharing concerns
Its classic software has free versions that include integrated ads. Users can either subscribe or manually disable ads from a desktop client through the settings to eliminate ads. However, if you use uTorrent Web, the ad-blocking feature is unavailable.
You should note that ads can increase security risks by potentially installing malware. A notable incident in 2017 involved a compromised advertisement within a torrent, which was utilized to circulate malware known as Meadgive, which aimed to exploit a Flash vulnerability to put ransomware on systems.
The inclusion of ads in uTorrent raises concerns regarding user behavior tracking. According to uTorrent’s privacy policy, Rainberry, Inc. shares data with advertising partners to promote personalized advertising.
For a comprehensive overview of uTorrent’s four subscription levels and their advertising policies, refer to the table below:
| Subscription tier | Price per year (USD) | uTorrent classic | uTorrent web |
|---|---|---|---|
| Free | $0 | Includes adverts | Includes adverts |
| Ad-Free | $4.95 | No adverts | Shows adverts Uses less bandwidth |
| Pro | $19.95 | Includes no adverts | Includes adverts |
| Pro + VPN | $69.95 | No adverts Includes CyberGhost VPN Offers Antivirus Software Includes File Conversion | Shows adverts Includes CyberGhost VPN Offers Antivirus Software |
The uTorrent Android app offers various useful features, including bulk downloads, music, video playback, and a WiFi-only mode to conserve mobile data. Additionally, it provides the convenience of remotely adding torrents to uTorrent Classic on Windows. Although the app is free, users can pay $2.99 to remove ads and access power-saving features.
Previous uTorrent security vulnerabilities

It is crucial to recognize the previous vulnerabilities that uTorrent has faced. In 2018, Google security researcher Tavis Ormandy discovered a vulnerability that allowed possible malware planting on users’ computers. Although uTorrent released a fix, it failed to rectify the security issue. Instead, their response stopped Ormandy’s exploit.
Vulnerabilities and subsequent patches are common in software development because of their complexity and the possibility of errors slipping through. Sadly, uTorrent’s handling of these vulnerabilities has raised questions about user security and prompt response to such issues.
Let’s delve into more details to gain an in-depth understanding of uTorrent’s nature and its implications for users’ security and privacy:
1. Is uTorrent infected with a virus?
Generally, uTorrent is not considered a virus but is often flagged by third-party security software. This could be due to criticism about uTorrent using tricks to persuade users to install unwanted software.
In a test, it was subjected to various common antivirus programs, and 28 out of 66 identified it as potentially malicious. Furthermore, the installer for the web client raised suspicion, as 11 out of 58 virus scanners marked it malicious.
While uTorrent is not a virus, it is necessary to exercise caution against illegal copies containing viruses. To ensure safety, it is suggested that you always download uTorrent from the official website.
2. Is there a connection between uTorrent and crypto miners?
As you may know, a crypto miner uses your computer’s processing power to mine cryptocurrency, resulting in a significant slowdown of your device. In 2015, uTorrent included the Epic Scale crypto-miner in version 3.4.2. This crypto-miner focused on mining Litecoin, and the mined currency was sent to an anonymous owner.
Many users raised concerns, with some claiming that Epic Scale was secretly installed without their consent in the background. Others mentioned encountering a prompt during the uTorrent setup process. The overall lack of transparency led to considerable criticism. In response to the feedback, uTorrent canceled ties with the crypto miner and ceased bundling it with its software.
3. Is uTorrent open-source?
It is not open-source, meaning its source code is inaccessible for inspection by external security researchers.
Due to this, there’s limited ability to scrutinize the code quality or verify how the torrent client handles personal data unless access is granted. As a result of this closed nature, the qBittorrent scheme started, offering an alternative that addressed these concerns.
4. Is uTorrent considered legal?
uTorrent is considered legal for download and use in various countries, including Australia, Canada, the United States, the United Kingdom, New Zealand, and many European countries.
Regardless, it is crucial to note that downloading copyrighted movies, software, and music without proper authorization is not allowed. During the leeching process (when you download torrents), your seeds also share content for others to download.
Furthermore, distributing copyrighted materials, which is unlawful in most countries, can result in legal consequences.
Best practices for safe torrenting

Irrespective of the torrenting client you opt for, engaging in torrenting comes with intrinsic risks. In addition to the vulnerabilities we’ve discussed earlier, there are additional risks to be aware of.
- Disclosing your IP address: Copyright trolls can monitor your torrenting actions and use your IP address to scare you with legal action via your ISP.
- Downloading unwanted software: Malicious actors often distribute malware by disguising it as legitimate files and letting users install it voluntarily when torrenting.
- Bandwidth throttling: Depending on their policies, ISPs may implement bandwidth throttling or even ban users who torrent on their network.
If safeguarding your anonymity and prioritizing security during torrenting is essential to you, we have comprehensively discussed how to use uTorrent safely and securely below:
1. Download it from the official website
It is essential to prioritize your safety when downloading uTorrent. To avoid potential risks of viruses, malware, and other undesirable software, download uTorrent from an authorized website. This guarantees that you get a legitimate and secure version of the software.
2. Turn off advertisements in uTorrent
- Purchase a subscription: Buying a subscription allows you to turn off ads on desktop and Android clients. Prices range from $4.95 annually on the desktop to $2.99 on Android.
- Download version 2.2.1: If you prefer a version without ads, you can download version 2.2.1. This was the last version not to include ads and is still widely used in the torrenting community.
Remember to consider the risks associated with using older software versions and make a well-informed decision depending on your unique needs and preferences.
In any case, there are three risks involved in doing this:
- Unavailability of the initial version: The original version (2.2.1) of uTorrent is inaccessible on the official uTorrent website. To download it, consider trustworthy sources like oldversion.com.
- Security vulnerabilities: Version 2.2.1 was launched in 2011, making it susceptible to security risks that have since been fixed in newer versions.
- Compatibility issues: Using the initial version might cause compatibility challenges. Keep in mind that uTorrent does not support the old version.
While uTorrent version 2.2.1 doesn’t have ads, its age of 10 years raises concerns about unaddressed issues. The safest option is the latest version, with ads removed through a subscription.
Thankfully, you can personalize settings to disable ads in the free version of uTorrent Classic, providing a better user experience.
To turn off the ads in uTorrent:
- In the menu bar, click “Options” and choose “Preferences.”
- Navigate to “Advanced” in the left-side window.
- Use the filter box to check out the following options, then select them and set them to “False” at the bottom if they aren’t already:
- GUI.show_plus_upsell
- offers.sponsored_torrent_offer_enabled
- offers.left_rail_offer_enabled
- offers.sponsored_torrent_offer_enabled
- GUI.show_notorrents_node
- offers.content_offer_autoexec
- Bt.enable_pulse
- Click “Apply” to save the changes.
- Restart uTorrent for the changes to take effect.
Note: This process will only eliminate the ads from the free version of uTorrent Classic and not the links to TronTv and DLive.
3. Pair uTorrent with a reliable VPN
A Virtual Private Network (VPN) serves two critical purposes regarding torrenting. First, it hides your shared IP addresses to prevent copyright trolls and other users in the torrenting community from identifying you.
Secondly, VPNs encrypt your internet connection, preventing your ISP from monitoring your downloads. This ensures your online activities remain private and safe while using any torrenting client, such as uTorrent.
How to pair a VPN with uTorrent
To ensure safe and anonymous torrenting, follow these steps:
- Subscribe to a reliable torrenting VPN application. We advise using ExpressVPN for this purpose.
- Choose a nearby VPN server for fast internet speeds.
- Leverage a VPN kill switch and activate manual leak security settings for advanced protection.
- Check for data leaks using a VPN testing tool to protect your information.
- Launch uTorrent and begin downloading your files.
- Keep the VPN active until you entirely turn off your torrenting client. Note that the client may continue to share files after you finish downloading.
In cases where uTorrent doesn’t work with your VPN server, try reconnecting to a different one. Few VPN services, including Avast SecureLine, have modified peer-2-peer optimized servers for torrenting.
However, if the issue persists, consider using a VPN that fully supports P2P activity for a seamless torrenting experience.
Best VPNs for using uTorrent safely
1. NordVPN

NordVPN is a top VPN service that offers top-tier security through military-grade encryption across its broad network of over 6,800 servers in 110+ countries. This ensures users enjoy a high level of privacy and protection.
With NordVPN, users can experience consistently high speeds regardless of location, making it ideal for downloading torrents and accessing various torrenting websites. This service is also known for its stability and reliable connection speeds.
NordVPN includes essential features like split tunneling, AES-256 encryption, and a kill switch that ensures your online presence remains secure when using the web. The added Threat Protection feature protects you from malware and intrusive website ads.
2. Private Internet Access (PIA)

Private Internet Access is a highly regarded VPN service known for its military-grade 256-bit AES encryption and robust security features. With its extensive network of 35,000+ servers, the VPN supports the OpenVPN protocol, providing users with a reliable and safe experience with uTorrent.
Adding MACE malware and ad blocker further facilitates user protection while browsing. The unlimited device connection feature is another plus, allowing users to protect multiple devices simultaneously.
Despite lacking advanced customization options, its performance, security, and responsive customer support position it as a top contender in the VPN market. Additionally, their 30-day money-back policy offers additional peace of mind for users.
3. ExpressVPN

ExpressVPN is among our list of the best VPNs for uTorrent, thanks to its strong security, fast connection, and exceptional customer support. With the ability to connect up to eight devices simultaneously, this service ensures added convenience and security by not storing personal data.
Using AES-256 encryption with OpenVPN and Lightway protocols, ExpressVPN maintains a high level of security, making it an excellent option for torrenting. Plus, its TrustedServer technology guarantees that no user data is stored on the RAM-only servers.
Is the uTorrent app safe to use? (Full tests & results)

While torrenting always presents inherent risks to your online safety, being cautious can help eliminate these dangers. uTorrent is inarguably popular and generally considered safe to use. The application does not contain malware and efficiently downloads and distributes torrent files.
However, users must note that uTorrent isn’t the most secure torrenting client available. We suggest that you consider using other torrenting clients that prioritize robust security features and offer better protection against risks.
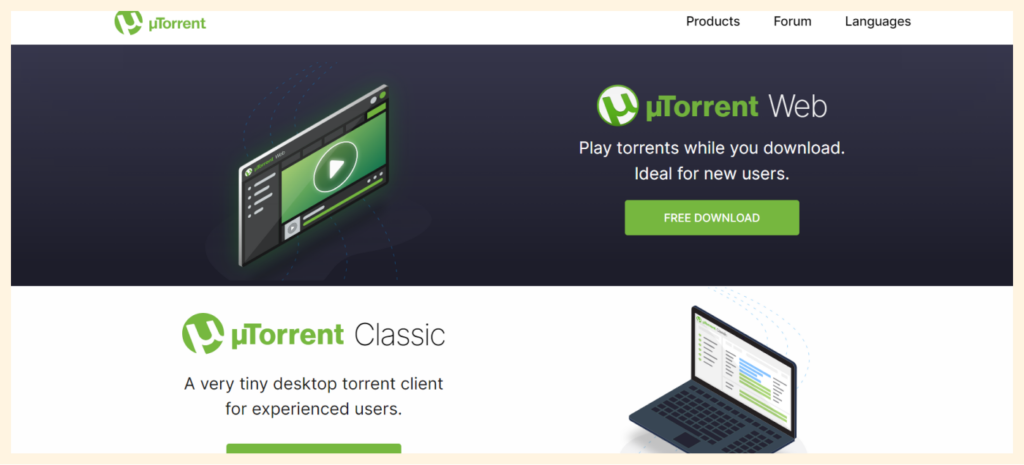
There are two versions of uTorrent available for your computer:
- uTorrent Classic: This is the desktop client, compatible with Windows, Mac, and Linux. It is designed for bulk downloads, offering features like the ability to turn off the app or your PC after downloads and a scheduler for managing downloads. It also supports simultaneous torrent downloads.
- uTorrent Web: This version allows you to download torrents and stream files in your browser while the files are still downloading. It includes a safe torrent scanner to help you find secure torrents when browsing the web. If you’re using macOS with Catalina 10.5 or later, uTorrent Web is available, and there’s no desktop application for this version.
Both uTorrent versions have undergone safety tests and are considered safe to download. However, compared to qBittorrent, uTorrent poses a higher risk to your privacy and security.
Additionally, uTorrent is not an open-source client, meaning it cannot be independently inspected for security, leaving vulnerabilities unaddressed.
Although uTorrent has its strengths, it also comes with certain weaknesses when choosing a torrent client. The table below shows both its strengths and weaknesses:
| Strengths | Weaknesses |
|---|---|
| The premium subscription of CyberGhost includes valuable features like antivirus protection, malware blocking, and access to their VPN service | The installation process may include unwanted software |
| To safeguard user privacy, the service supports IP binding to prevent your public IP address from leaking | The free version displays advertisements |
| It has integrated support for the SOCKS5 proxy | In 2018, there was an incident where an advert was used to distribute malware |
Privacy risks
When using uTorrent and examining the seeders and leechers sharing a file, you will notice a list of IP addresses. Each IP address corresponds to a uTorrent user sharing the same content. While you can view their IP addresses, they can also see yours.
Your IP address is crucial in revealing your real-life location, making it an integral part of your online identity. As such, it is crucial to be cautious when determining whom to trust with this sensitive information.
Hackers could potentially manipulate your exposed IP address to launch attacks on you. Consequently, protecting your IP address should be an essential precaution to ensure online security and privacy.
Disadvantages of using uTorrent
1. Seeding is essential
Seeding is an essential part of the uTorrent process. When a file download is complete, it needs to seed before you can fully access, install, or use it. Moreover, seeding is time-consuming, particularly when downloading multiple files simultaneously.
2. uTorrent can slow down your device
Using uTorrent or any other BitTorrent client can potentially slow down your device. Since downloading and uploading files occur simultaneously, it consumes huge bandwidth. This, in turn, leads to a reduction in internet connection speed.
Sometimes, the internet may become so slow that it hinders you from opening other tabs or accessing different online services.
3. Downloading completion is required before viewing
Compared to regular streaming and downloading websites, uTorrent requires you to wait for the download to complete before viewing or previewing your file. This limitation presents two major disadvantages.
First, you can’t ascertain the file’s quality before the download is complete, and second, you cannot be entirely sure about downloading the correct file until the download process is complete.
4. Enhanced privacy requires a VPN
Using a VPN is crucial to safeguard your online activities from your Internet Service Provider’s (ISP) tracking. Generally, VPN services require subscriptions to access their premium features.
With a VPN, you can ensure your IP address remains secure and does not leak to third parties. However, this added layer of privacy comes with associated costs.
FAQs
Yes, uTorrent is considered safe to use on Mac. However, knowing its history with malware from third-party tools is crucial. We suggest installing an antivirus program on your Mac device when using uTorrent for additional security.
Using uTorrent with a free VPN can be risky due to the limitations of such services, including reduced download speeds and restricted features. If you opt for a free VPN, ensure that it offers robust encryption, follows a no-log policy, offers leak protection, and includes a kill switch.
Seeding in uTorrent involves peer-to-peer connections where leechers download torrents from your device. This process uses your data, and if your upload bandwidth becomes overloaded, it can slow down your internet connection speed.