Malvertising is a growing trend in the cyber world, and it deploys ads to end-user systems for carrying out cyber attacks. As a result, it can infiltrate your device and cause harm.
This detailed guide will teach you to defend against malvertising attacks. But, to better prevent malvertising, you must understand the basic principles first. So, let’s start with them.
Malvertising explained
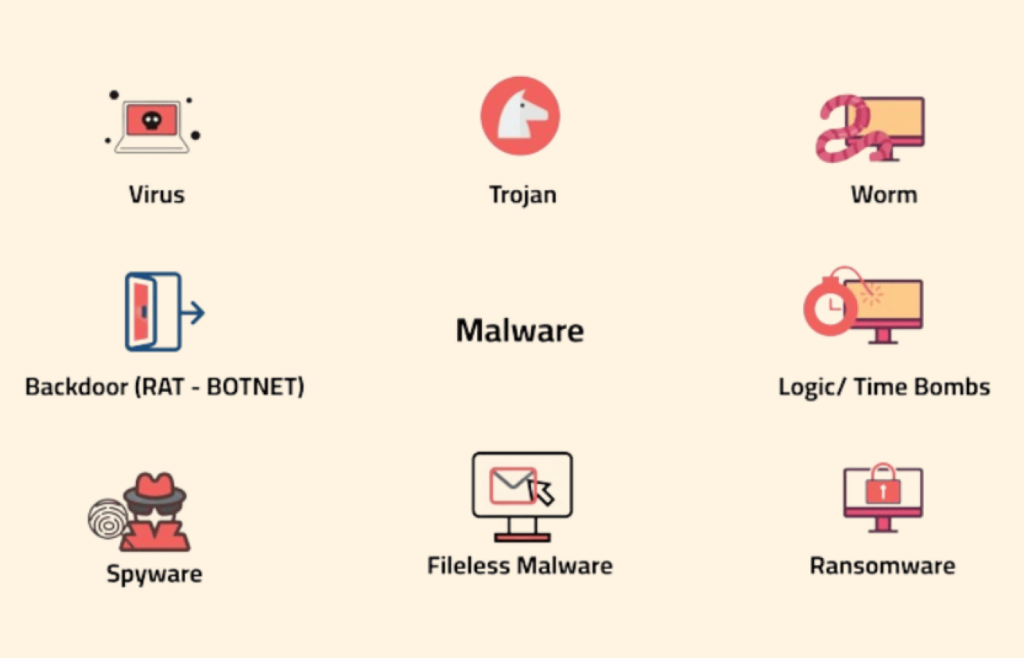
Malvertising or malicious advertising is a growing technique that cybercriminals use to carry out malicious internet campaigns. The name comes from the combination of two words, which are malware and advertising.

Offenders would often take over an entire advertising network, and sometimes they pay for display ads. They deploy various kinds of ads to carry out cyberattacks and infect users with malware and spyware.
Some malware ads are so robust that it becomes troublesome to avoid them. Talking about the complexity of malvertising technology today, a user may not even click on the ads for the malware to attack in some instances. You can become a victim by visiting a site with a malicious ad.
Cybercriminals often develop these malicious ads and place them on legitimate and illegitimate popular websites to gain optimum results. Some of the sites where malicious advertising appears are popular and trusted. Unfortunately, unsuspecting users often load the pages and get infected through the poisoned ads.
Types of malvertising
Now that you know the essentials of malvertising, let us look at the types.
There are two major malvertising types, and both deploy ads to host malware on your device. However, the method of execution differs. They are Click-to-Download and Drive-by-Download malvertising.
1. Click to download

In this malvertising type, the user must click on the ad before it can infect the user’s device. These types of ads masquerade as real ads, and they deceive users into clicking on them.
2. Drive-by download
A drive-by download does not require users to interact with or click on the ad. It automatically infects your system once you visit a website it has been deployed on. Sometimes, you can also get infected when it forcefully redirects you to an infected website.
Sub-types of malvertising
Tech support scams
Tech support scammers have targeted Windows users for a long time. Also, Mac users are becoming victims of social engineering tricks as scammers exploit their assumed sense of safety. In both cases, phony sites deceptively pose as Apple or Microsoft and use JavaScript to prevent pages from closing naturally. As a result, frustrated users dial the toll-free number provided by malvertising for assistance. Then, the fraudsters intimidate the victims into purchasing useless tech support.
Get-rich-quick schemes and other surveys
Unscrupulous ad networks aggressively disrupt your browsing with screen hijacks. This can include bogus surveys, work-from-home scams, lottery offers, and other free services that seem too good to be true. In the past, iPhone users have also been affected by these schemes.
Scareware
Like tech support scams, scareware tells you that your Windows or Mac devices are extremely infected or damaged and asks you to download software to fix it. This is mainly done by greedy, malvertising affiliates attempting to increase leads to generate bigger commissions off several potentially unwanted programs (PUPs).
Fake Flash Player/ other software updates
This is a common technique to insert malware and adware on macOS devices. Hackers design sleek pages that pose as updates for the Flash Player or video codecs. Sometimes, the installer downloads itself automatically onto your device. These campaigns are particularly available on video and adult streaming websites because users can be tricked into downloading the program to watch the content they want.
We recommend avoiding these applications at all costs. However, if you decide to download them, use the vendor’s official website to prevent copycats. These copycats can contain malware, spyware, and junk that slows down your macOS device.
How does malvertising work?
Web advertising is a complex ecosystem comprising content delivery networks (CDNs), retargeting networks, ad servers, ad exchanges, and publisher sites. When a user clicks on an ad, various redirects occur between distinct servers. Unfortunately, cybercriminals exploit this interconnection to secretly deploy dangerous content in the least expected places for networks and publishers.

When you click on an ad when visiting a website, you may accidentally trigger malware installation on your device. It can corrupt files, exfiltrate data, establish unauthorized access points, and monitor your activities. In addition, malware can block, manipulate, leak, delete, or copy data, which can be sold to third parties or extorted for ransom.
Even worse, malvertising attacks can install an exploit kit on your device. It is a type of malware that explores a system and exploits security gaps and vulnerabilities.
What are malvertising attacks used for?

Cybercriminals develop various forms of malware and use them for many nefarious activities. For example, advertisers may carry out espionage, sabotage, ransom, and fraudulently profit from advertising and e-commerce agencies.
Did you know that malvertisers can buy advertising space on some of the world’s most popular websites? In the past, these unscrupulous ads have found their way into websites such as Spotify, the New York Times, the London Stock Exchange, and so on.
As hinted earlier, you can still be a victim whether or not you click on these ads. This strategy is what we know as “Drive-by-Download.” All it takes to be a victim is a mere visit to a website with malicious ads.
Here are the various uses of malvertising in brief detail:
1. Ransomware attacks
Ransomware is a malicious application that encrypts a target device and renders the information unreadable/unusable. Then, the cybercriminal would demand a price or ransom from the victim to restore data.

They will show you how to make payments, and you’ll get a decryption key to your device.
Some cybercriminals will not send you a decryption key sometimes, and your information becomes permanently unreadable even after you’ve paid their demanded money.
Ransomware gets deployed through many ways to gain access to users’ devices today, and Malvertising is among the most efficient methods that get the job done for hackers.
2. Spyware attacks
Spyware can infect your device and monitor your activities for an extended period without your notice. They take note of your screenshots, emails, chats, messages, keystrokes, and ultimately every bit of your data.

After gathering targeted information, the spyware sends it back to the cybercriminal server through the internet. Cybercriminals can use the information to blackmail you, carry out espionage, identity theft, unauthorized fund transfer, etc.
Sometimes, they can use spyware to monitor you and deploy more intrusive ads onto your device. Spyware monitors your activities and helps people with malicious intent to deploy intrusive ads on your browser through malvertising. That is why spyware removal should be among your regular system check-up practices.
Have you ever wondered why you started receiving ads for similar products you bought online? Sometimes, you would receive endless and annoying ads after searching for a specific product or information online.
Other times, you may even receive direct emails and phone calls about products and services you bought or searched for online. Spyware facilitates this whole annoying process.
3. Trojan infections

The name “Trojan” came from the Trojan War. Greek soldiers invaded the city of Troy despite high resistance to winning the war. Eventually, the computing world adopted this word for a powerful malicious program that can invade your device and infiltrate you.
Trojans are one of the most potent and lethal malware today. Malvertisers can deploy Trojans to your system just by making you visit a poisoned link.
Another way hackers and cybercriminals use trojans to gain access to your device is through social engineering. They can use it to spy on your cell phone and other devices once they access your system.
4. Cryptojacking
It is a hacking form where hackers illegally hijack someone’s computer to mine cryptocurrency. Cybercriminals use malicious advertising to deploy these tools. Cryptojacking uses automated JavaScript codes to carry out its ruthless functions.

In the past, malware was the only way to get infected by clicking on an infected link, downloading a file, or opening an attachment. However, hackers have dramatically improved their codes and techniques over the years.
Today, you do not necessarily have to click on a link or open an attachment to be a victim. Instead, all it takes is a malicious ad to appear on your browser, and your computer starts mining cryptocurrency without your knowledge.
5. Hacking by bots

Hackers use automated bots to recruit secondary devices and carry out DDoS attacks. DDoS is an acronym for distributed denial of service, and it is a rising problem worldwide.
Cybercriminals deploy botnets to send heavy traffic to servers, networks, and popular websites to overwhelm them and ultimately take them offline or do malfunctioning. One way they achieve that is through malvertising.
6. Adware campaigns
Adware generates revenue for a cybercriminal by developing unauthorized traffic and online advertisement. It mainly earns through advertising agencies and eCommerce stores.
They direct ads to an advertising agency or eCommerce store and make money. In some cases, they redirect the user’s traffic and make it seem like it is coming from the cyber-criminal. Like many other computer viruses, adware disguises itself in the form of ads and gets into your system when you visit an infected website.
Can you get malware from ads?
Yes! You can get malware from ads. The research carried out in 2019 found that hackers imbed malicious codes with disruptive intent in one out of every 100 ads.

Nonetheless, tech giants like Google have been working hard to eliminate intrusive and malicious ads from their platforms.
According to reports, Google removed as many as 100 malicious ads every second in 2017. Of these, 66 million were trick-to-click ads, 79 million redirected people to malicious sites, and 48 million tried to persuade internet users to install a malicious program.
Internet users face multiple threats from malicious ads. The most common malvertising threats and attacks are from ads and auto-redirects. In auto-redirects, an internet user is automatically redirected to a harmful page.
Others include malware ransom attacks, phishing scams, auto file downloads, etc. That is the magnitude of malvertising problems internet users face today. So, you must watch out to protect your information from hackers. Do not take it for granted.
How does malvertising affect web users?
Malvertising is a potent cybersecurity risk that affects every internet user it comes across. When it’s about the end users – you – here’s how it impacts your online security upon clicking or viewing the ad (even when you do not click).
- Installs adware or other malware on the target device. Such attacks usually exploit browser vulnerabilities.
- Redirects the user to malicious sites.
- Barrages users with annoying or malicious ads and pop-ups by executing dangerous scripts.
Impact of Malvertising on web publishers
Malvertising is even more dangerous for web publishers, affecting their credibility among the clients and in the market, apart from inflicting financial losses. Moreover, in large-scale data breaches, publishers even risk suffering legal consequences.
Therefore, for publishers, preventing malvertising is crucial, not only for their own security but also for the safety of their customers. However, detecting malicious ads becomes complicated when they allow dynamic advertising on their sites and lose control over how and which ads the relevant ad networks publish. That’s where the malicious ads sneakily reserve a place on legit websites, ultimately targeting publishers and users.
Malvertising examples
Malvertising does not affect only shady websites. Here are some of the most famous examples:
Yahoo
In 2015, Yahoo suffered a widespread malvertising attack. Cybercriminals sneaked malicious ads on the website and attempted to install malware on users’ devices.
Moreover, they exploited Adobe Flash’s vulnerability to install fraudulent ads and ransomware. Thankfully, Malwarebytes alerted Yahoo of the fraud, and it removed the malicious ads.
The New York Times and BBC
Popular news websites, including BBC and The New York Times, were hit with a malvertising attack in 2016. When they clicked on ads, readers were redirected to malware sites with Angler exploit kit, which installed a crypto locker-style program. This type of malware encrypts the hard drive, forcing victims to pay attackers Bitcoin to unlock it.
Spotify
This music streaming platform was caught in a malvertising scandal in 2016, where some ads contained malicious codes. The ads redirected users to suspicious pop-ups or attempted to install malware.
Luckily, Spotify learned about the fraud from its users and quickly resolved the issue.
Covid-19
There was a significant drop in malvertising in the last few years, but it resurfaced stronger than ever in 2020 due to COVID-19. Cybercriminals took advantage of COVID-19 news in the media to inject COVID-19-related ads with malicious code to redirect readers to phony websites or install malware on their devices.
Malvertising vs. Adware
Adware and malvertising share a lot of similarities, but they are different.
Malvertising is used to embed malicious codes in adverts. They’re highly manipulative and create an open door for viruses, spyware, and other fraudulent applications to hijack your system.
However, adware constantly runs on a user’s device and affects how web pages function. Few are safe, but some of them are highly intrusive and dangerous.
In summary, malvertising disguises intrusive applications through ads, while malicious adware generates money directly for the cybercriminal by driving traffic.
Malvertising does not make direct money for the cybercriminal. Instead, it creates a loophole for the wrongdoer to make money through blackmail, ransomware, spyware, and other methods.
Hackers use adware to send ads to users, and the advertisement agency pays them for every ad clicked. In some instances, malvertising deploys adware to spread malicious ads to users.
How to identify malvertisements?
You might wonder how to identify the actual adverts from those appearing online. And which ones are potentially harmful? Let us teach you how to identify malvertisements.
Since cybercriminals keep developing sophisticated systems, you cannot decide at a glance if an ad is part of a malvertising campaign or legitimate. However, you can use some strategies and look for alarming signs to avoid clicking on a malvertisement. Below are some signs you need to be aware of:
- Ads with mediocre designs that suggest a professional graphic designer did not design them.
- Ads promising celebrity scandals or miraculous cures. (Anything online that sounds too good to be true is likely a lie.)
- Advertisements with spelling errors.
- Ads mismatching with your typical/recent browsing behavior or web search history.
Where do internet users encounter malvertising?

You can be exposed to malvertising on an infected website or application on the internet. That includes advertisements on videos, banners, pop-ups, web applications, and so much more.
Sometimes the website displays ads directly, and on another day, it may be third parties or ad networks. (An ad network connects advertisers and websites and deploys various ads based on users’ searches and preferences.)
Arguably, you can encounter malvertising on any website.
But you would likely see them on gambling portals, pornography sites, document-sharing websites, etc. Therefore, it is imperative to avoid such websites because they are heavy malware carriers.
How do attackers get their ads onto websites and apps?
Hackers and cybercriminals deploy malvertising on the internet in three distinctive ways. Below, we cover them all:
1. Compromising ad network
It is an efficient technique used by hackers to infect devices with malvertising.
Cybercriminals take over a network, compromising the network and spreading malicious ads on the internet through a hijacked network. This method helps wrongdoers compromise and use even legitimate websites for their interests.
2. Buying ad space
Attackers would usually buy ad space on websites with malicious intent. They pay advertisers and website owners to deploy ads that infiltrate users’ devices without them knowing.
Some website owners and advertisers may not be aware of the malicious intent of the ads. But sometimes, others may not care because they only want to make money.
3. By building an advertising agency
Cybercriminals can build their own ad network and marketing agencies to trick users and carry out attacks. However, this strategy is uncommon because it requires more funds and work.
But, powerful and well-funded cyber criminals have, in the past, formed agencies to carry out attacks.
In 2017, a criminal agency created 28 ad agencies, which they used to deploy about 1 billion malvertising ads known as the Zirconium attacks.
How malvertisers escape detection
Initially, the malvertisers design their advertisement harmlessly. The ad looks legit, with a creative end for user interaction and a legitimate landing page. Then, when the ad successfully passes through a scan, the malvertiser cleverly replaces the initial creative with the one intended for the users. At the same time, the malvertiser also links the actual malicious landing page to the ad, replacing the previously scanned harmless one.
These malicious landing pages are designed in a tricky way to bluff users. They often imitate otherwise legitimate websites in design and layout. But the pages are seldom intended to provide the offered service. Instead, the attackers aim to target users visiting the web pages with malware or steal sensitive information such as login credentials or credit card details. That’s how the malvertisers carry on successful phishing and malvertising campaigns, escaping any detection and security checks.
How does malvertising succeed in infecting site visitors?

Understanding system vulnerabilities is the first step in knowing how to prevent malvertising. Malvertising infects internet users primarily by exploiting vulnerabilities or social engineering. Let’s take a look at the key ways malvertising infects a website’s visitors:
1. Vulnerabilities
Computer malware is known to take advantage of vulnerabilities and loopholes in your system and infect it. Therefore, you should never neglect to update your plug-ins, web browsers, and device operating system.
An outdated system and application create loopholes for hackers to infect your system with malicious programs.
Setting up an auto-update on your system can save your day. The vulnerabilities caused by the following can create loopholes for cybercriminals to take advantage of:
- Outdated web browsers
- Outdated operating systems
- Older versions of web browsers
- Older versions of plug-ins and extensions
- Older version of Adobe Flash
2. Fingerprinting
Cybercriminals will often check for fingerprints on users’ devices to determine if there is any vulnerability. Then, if they detect any, they deploy tools that exploit those vulnerabilities through a series of attacks.
Browser fingerprinting is a technique that cybercriminals (and digital agencies) use to cluster a range of information about a user to identify them on the internet. The data can include system configuration, IP address, device name, operating system, browser version, and more.
3. Social engineering
Social engineering is a technique that cybercriminals use to manipulate people and make them hand over their sensitive information.
While browsing, you may have received a message that your device is infected or will soon crash. That is usually not true, but it is a trick by cybercriminals to make you panic and hand over sensitive information to them.
Once users fall into an attacker’s trap, he then uses the collected information to hack users’ accounts and devices.
The information attackers seek may vary based on their intent, but they mainly trick people into unveiling banking details, passwords, etc. Sometimes, they ask you to run other applications on your PC to resolve an issue. Then guess what? Your system will be infected after you run such applications.
Mobile malvertising
A few years ago, only computers were the prime targets for malvertising. But lately, smartphones and tablets have become the main focus of malvertisers.
The reason behind mobile devices are becoming a hotspot for malvertising is simple. It is because more people are using mobiles to access the internet today. Also, as per the reports, 60% of people click on mobile advertisements at least once every week. That pretty much tells why malvertisers are shifting their focus onto mobile users.
Recently malvertising has targeted both iPhone and Android users all around the world. Cybercriminals use malvertising to carry out intelligent phishing attacks on mobile devices. Crytojacking is also rising dramatically, where criminals hijack phones to conduct cryptocurrency mining.
And lastly, malvertising campaigns are used to deliver malware payloads on mobile devices. These attacks are carried out through ads that install infected applications on users’ systems.
How do I get rid of malvertising?

However, you can take the following internet security best practices steps as an individual to avoid malvertising. We tested all these measures by visiting websites containing malvertisements, and they worked well in keeping us safe.
1. Keep your system and applications up-to-date
An outdated operating system, web browser, plug-in, and storage devices can become a security hazard anytime. If your device is outdated, your system will be more vulnerable to ransomware, spyware, Trojans, and other malicious programs.
Carrying out the regular operating system and browser updates can significantly eliminate vulnerabilities in your device. That way, you can prevent hackers from exploiting device vulnerabilities and deploying programs that can pose security challenges to you.
2. Make a reputable antivirus your friend
3. Use a safe browser
Many web browsers out there lack the robustness to handle malvertising. Most mainstream reputable web browsers cannot protect you against malvertising 100%. But some of them have an adequate security mechanism to help keep you safe to some extent. For example, Mozilla Firefox, Google Chrome, and Microsoft Edge browsers have safety features on newer versions of their web browsers for safer browsing.
That is not the case with other widely-used web browsers.
On top of making your Firefox, Chrome, or Edge more secure, you can also consider trying some security-focused web browsers available today.
Lastly, no matter whichever browser you use, ensure that JavaScript and Flash players are set not to auto-run on your web browser. Your system can be compromised through flash players and scripts; therefore, you must understand their source before playing them (if you need to, you must).
4. Consider using a firewall (or activating your existing one)
Installing an effective firewall can significantly keep you away from malvertising trouble. The firewall should be enabled on personal devices and enterprise devices alike.
The best thing is that you do not need to spend a fortune on a firewall. Today, you can easily find free firewalls that quickly stop malfunctions like redirects, keeping you safe from landing on an unsafe website. Moreover, firewall rules can also be set to manage iframes and other tools that hackers deploy to infiltrate devices.
5. Be cautious all the time
Avoid visiting potentially harmful websites, be careful while downloading files and applications online, and avoid adding unknown plug-ins to your browser.
Unfortunately, many insecure add-ins on the internet can significantly expose you to security threats. So, install extensions developed by reputable organizations and only the ones you need.
Furthermore, you should download files from trusted sites only. Also, get mobile applications only from the official Play Store or Apple Store. You must avoid downloading applications from third-party websites.