The internet consists of three types of web: Surface web, deep web, and the dark web. Both the surface web and the deep web (some part) are accessible through typical browsers, such as Firefox and Chrome. Nevertheless, the dark web is that shady part of the web that is only accessible through a special browser like the Tor browser.
This hidden part of the web carries several illegal activities, including drug and weapon dealing, pornography, private data, and more.
However, if you are thinking the dark web is only for illicit activities, you are wrong; not only do cybercriminals use this darker side of the internet, but also whistleblowers, journalists, and everyday internet users (who take their privacy seriously) use the dark web to get useful information and stay anonymous.
But the question is, how can you access it safely and anonymously (of course, for legitimate reasons)? This article explores a step-by-step guide accessing accessing the dark web safely and anonymously for legitimate purposes. Let’s explore.
DISCLAIMER: This article is only for informational purposes, and we only intend to educate users about potential threats and how to remain safe while accessing the dark web. The dark web and deep web host both legitimate privacy tools and illegal activities. Below are some concerns you must know about the dark and deep web:
- Accessing dark web forums may expose you to illegal content, malware, scams, and law enforcement scrutiny.
- Engaging in or promoting cybercrime is illegal and punishable by law.
- We do not endorse or encourage accessing these forums unless for legitimate security research.
- Always prioritize your security (use VPN such as NordVPN and antivirus of your choice with Tor browser) and avoid sharing personal information.
Ready?
We’ll first cover the basics. Things like what the dark web is and how it differs from the deep web (before diving into its legitimate uses and serious risks). If you already understand the fundamentals and want to get straight to the safety instructions, you can jump directly to our step-by-step guide on browsing the dark web covered later.
What is the dark web, anyway?
The dark web is a hidden part of the internet that requires a special browser like the Tor browser to access it. Normal search engines like Google and DuckDuckGo don’t index this part of the web due to its illegal nature. Hence, you can’t find it on normal search engines.
Due to its hidden nature, the dark web is also famous for the names underground internet and black web. However, don’t fret yourself about this frightening concept, than the actual meaning of the dark web.
The dark web isn’t only about illegal activities; its primary purpose is to provide maximum anonymity by making your connection private online through encrypted servers. Sure, the dark web is known for its criminal underworld, but that’s not the whole picture. The darknet is a private place where nobody can intercept, monitor, or steal anything online from you.
What is the difference between the dark, deep, and surface web?
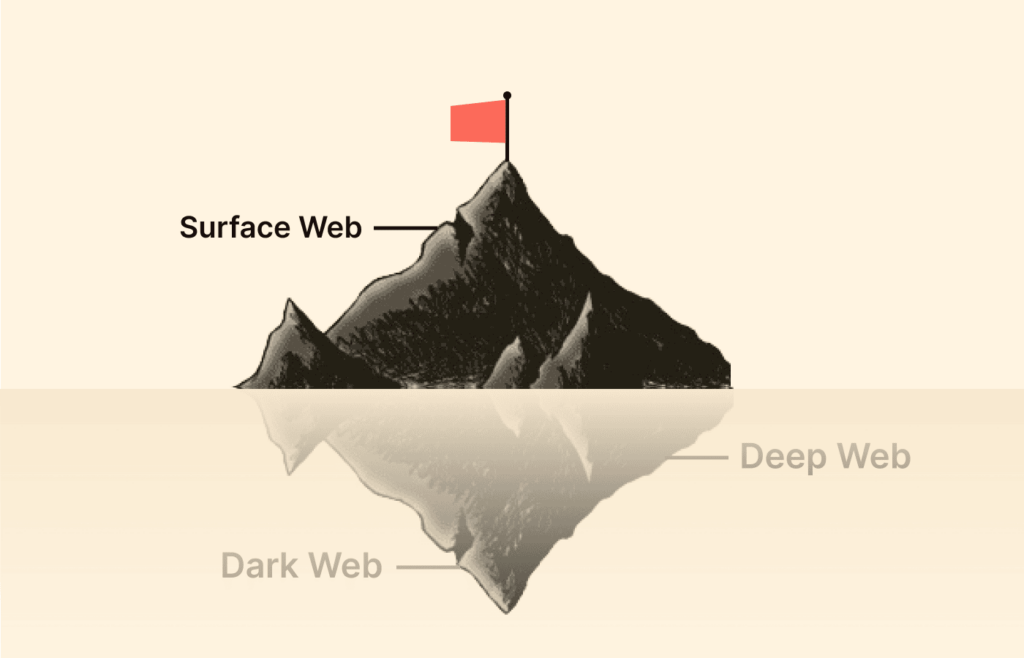
The internet is an extensive network of millions of servers, databases, and web pages that run continuously.
However, it’s more than what meets the eye. Think of it as an iceberg, with only a tiny part visible above the surface. If you dig deeper, you’ll discover the mysterious world of the deep web and, for the brave ones, the foreboding dark web.
The open web or surface web
This is what most of us know as the ‘visible web’—the part you can freely access using everyday search engines like Google, Bing, or Yahoo. It includes websites, databases, and other online resources indexed by search engines and is easily discoverable by users.
The open web makes up less than 4-5% of the internet, which is just the tip of the iceberg of the entire internet.
The deep web
This is below the surface web and accounts for about 90% of all websites. It includes all web pages not indexed by search engines. This portion includes academic journals, private databases, and other content hidden from the public for various reasons.
The deep web includes both legal and illegal content, including the portion known as the dark web. While many people use the terms deep web and dark web interchangeably, a large part of the deep web is safe and legal. Some of the largest components of the deep web include;
- Intranets: These are internal networks businesses, governments, and Learning institutions use to communicate and manage aspects privately.
- Databases: They can be privately or publicly protected and only searchable within the database.
If you are curious about accessing the deep web, you are likely already using it daily through pending website redesigns, blog posts under review, and pages accessed during online banking. Just because a page is hidden doesn’t mean it’s dangerous. There are plenty of harmless reasons sites stay out of sight, and they won’t put you or your computer at risk.
Some of the files hidden from the open web include;
- Legal files
- HIPAA-sensitive information like medical documentation
- Private enterprise databases
- Email and social messaging accounts
- Financial accounts like banking and retirement
While much of the content on the deep web is harmless, users can accidentally access dangerous content by navigating through tangential pathways, leading them to piracy sites, radical forums, or violent content. For this reason, users should be cautious when using their browsers.
You’ll find the more dangerous content and activity at the dark end of the deep web. This is where Tor websites are located, deemed the ‘dark web,’ and can only be accessed by an anonymous browser.
The dark web
A small part of the deep web is unindexed and requires a specialized browser to access. It is often associated with illegal activity and is known for trading sites where users can purchase illicit goods or services. The dark web has several anonymity layers, making it difficult to access. These layers include;
- It cannot be accessed through traditional browsers
- Lack of indexing by surface web search engines
- A randomized network infrastructure that creates virtual traffic tunnels
Let’s be honest, the dark web is infamous for its criminal marketplaces, where you can find almost anything illegal for sale. However, some legal parties also use the dark web. Read along to find out about that.
Why do the darknet and deep web exist? Legitimate uses
The deep and dark webs seem like illegal places you should not visit. But why do they exist in the first place? It is worth noting that the dark web is not always illegal, as many activities take place on the dark web that are within the law.
Talking about the fundamentals, the dark web and the darknet guarantee privacy and anonymity. The dark web is designed to protect private information, keeping sensitive data out of the public eye.
Given the dark web and the dark net’s anonymity principle, individuals can express themselves on unpopular issues but within the law. Talk about whistleblowers, bloggers, and many others.
The anonymity of the Darknet is mainly attractive for 2 groups: In the first group, some users require the security of the deep web for day-to-day communication. They exchange sensitive information and data, and, at times, have to risk their lives or those of their informant if they don’t share data under the safety of the deep web.
Such people can be opposition figures from dictatorship-led countries, politically oppressed individuals, whistleblowers, or journalists.
- To use the internet anonymously: It might surprise you, but the darknet hosts plenty of websites you’d recognize. They’re just like the ones you use on the surface web.
- Buy items that are difficult to get otherwise: Some common pain relievers and sleeping pills available in the EU are illegal in various Middle East and Asia countries. The dark web comes to the rescue in such cases.
- Swap data in countries that censor the internet: Many countries, such as Qatar, China, Cuba, Russia, and Turkey, censor internet content promoting political dissent.
- Revealing the abuse of authority: The dark web allows political activists and media persons to report stories that may cause them problems with governments or dictatorial regimes.
Understanding the risks: Why you need this guide
Let’s be clear: a huge portion of dark web content is highly illegal. No matter what precautions you take, you are ultimately responsible for the risks you take by venturing into it.
- Malware: The dark web contains malicious files and links that can steal your data or compromise your device.
- Visits to extreme content: You can encounter extremely inappropriate content such as radical terrorism forums, child pornography, and abusive content.
- Scams: Almost everyone on the dark web is trying to make a quick buck.
- Illegal marketplaces: The dark web marketplace has no limits. This is where people sell all types of goods and services like malware, stolen information, counterfeit documents, weapons, drugs, hacking services, etc.
- Government monitoring: There is a significant risk that the government can target you for visiting a dark website, as many Tor-based sites have been taken over by police authorities worldwide.
How to access the dark web safely: A step-by-step guide
Whatever your reasons for entering the dark web are, you must follow some crucial steps to ensure your safety so that you can access it in an entirely safe and anonymous way. Below you go with the steps to take:
Step 1: Install and connect to a VPN
A VPN hides your internet activity from your Internet Service Provider (ISP). Since using Tor can itself draw suspicion, a VPN masks the fact that you’re using it. It also adds a crucial layer of encryption before your traffic even enters the Tor network.
How to use a VPN:
- Choose a reputable VPN with a strict no-logs policy and obfuscation features. NordVPN is a reliable choice for this purpose. (For a detailed breakdown of the top services, check out our guide on the 5 best VPNs for the dark web if you want.)
- Download and install the VPN app on your device.
- Open the app, log in.
- Connect to a server in your preferred location. Your VPN must be active before you open the Tor Browser.
Step 2: Download and configure the Tor browser
The Tor browser is your gateway to .onion sites. It anonymizes your traffic by routing it through multiple volunteer-run servers around the world (known as onion routing), encrypting it at each step of the way.
How to download and use the Tor browser:
- With your VPN connected, go to the official Tor Project website (https://www.torproject.org). Never download Tor from a third-party site, as these are often bundled with malware. If you’re looking for a more detailed, step-by-step walkthrough, we have a complete guide on how to install Tor on different devices.
- Download the correct version for your operating system (Windows, Mac, Linux).
- Install it, then open the Tor Browser.
- When prompted, click “Connect.” Do not change the default settings for your first use. Here’s a golden rule: never download Tor from a third-party site. These versions are frequently bundled with malware that can compromise your security.
Step 3: Adopt “operational security”
One thing is for sure: the dark web is full of individuals that you don’t want to come across. Therefore, all you need to do is take security precautions.
- Browse with a VPN over Tor: VPN over Tor is when you connect your device to a VPN and start browsing on the Tor browser. It gives you an extra layer of security.
- Install TAILS (optional but recommended): When accessing the dark web, the last thing you want is to leave traces behind. The best way to clear the traces is by installing the Amnesic Incognito Live System (TAILS).
- Take extra security precautions: Before you fire up the Tor browser, take a moment to close all other apps, stop any unnecessary background services, and cover your webcam with a piece of tape (or paper).
- Know where you’ll visit: The best thing to do is get your hands on some good darknet directories to find secure pages. The dark web itself has a lot of dark web site directories to help you point out where you need to go.
- Go only with cryptocurrencies for transactions: Therefore, if you’re to purchase anything, ensure that you never use anything apart from a cryptocurrency.
- Close everything once done: For optimum safety, make sure you completely close all browser windows and any related tabs or applications once you’re done browsing the darknet.
How to remain safe while using the dark web – Essential tips
If you decide to roam into the world of the dark web, consider following the tips below to stay safe:
- Use a VPN: A VPN masks your IP address and hides your online activities. VPN like NordVPN comes with double encryption (double-VPN), which gives you an extra level of security for maximum anonymity.
- Use a premium antivirus: Antivirus tools like TotalAV protect you and your device from sketchy downloads and viruses.
- Install the Tor browser: Change your Tor settings to maximum privacy. Disable ActiveX, JavaScript, and Flash plugins, though some dark web sites won’t work properly.
- Be wary of downloads. Downloading things on the dark web is dangerous—you can download the wrong file.
- Don’t make any purchases: We don’t recommend buying anything from the dark web. Most of the transactions are risky and scams, even if they seem real. You can lose money or expose yourself to the dangers of hackers.
What does the dark web feature

Now, you might be wondering, what’s on the dark web?
Privacy and anonymity are the core values of the dark web, and it hosts both harmless activities and illegal content.
While some dark web websites may contain such content as complex riddles or some eBooks, one thing will always remain: the dark web is for dark material.
It means that the dark web contains illegal and disturbing content. Some of the foul stuff that you can find on the dark web includes:
Illicit substances
On the dark web, you’re expected to find illegal and prescription drugs (including Marijuana). Also, some toxic chemicals are peddled on the dark web that may cause severe damage to the targets.
Stolen information and fake IDs
Whenever a data breach occurs, the information will likely end up on the dark web for sale.
The information can be of any kind, either social security numbers or even bank card numbers (the bank/credit card information is usually sold in bulk).
Moreover, you can purchase things like hacked Netflix accounts, login credentials, and more on the dark web.
Interestingly, darknet sites also offer stolen documents and passports from around the globe. For example, you could find a passport from a UK citizen there for under a million dollars.
Dangerous and disturbing services and items
Many things you think are dangerous for a second can be found on the dark web.
One can buy anything on the dark web at the right price, including stuff like counterfeit goods, mercenaries for hire, child pornography, and body parts. Also, human trafficking businesses are run on the dark web.
Basically, you can get your hands on anything on the dark web, including some things you’d better not imagine.
Mostly on the dark web, financial transactions happen via cryptocurrencies such as Bitcoin, making it possible for parties to do business anonymously.
Uranium
In a world where almost everything can be bought, it is no surprise that uranium ore can be processed into weapons that can also be obtained from the Darknet.
Weapons
As you might have guessed by now, almost everything that criminals are after can be found on the Darknet.
Among other things, some darknet sites offer explosives.
Alongside C4 plastic explosives, one can purchase rocket launchers and numerous other weapons on the Darknet without much trouble.
Hitman
People can contact assassins on the dark web who are ready to kill for money. However, researchers believe most of them could only be scams.
Deadly Poison
Not too long ago, the case of a young man becoming wealthy by producing and selling ricin hit the headlines in the United States.
Ricin is a protein obtained from a milkweed plant that kills human cells quickly and is lethal even in tiny amounts. Almost all such deadly poisons are said to be available for sale on the dark web.
In 2015, a computer programmer named Mohammed Ali was jailed for eight years after he tried to buy ricin poison from the Darknet. The guy reportedly got inspired by the hit US TV series Breaking Bad.
The story hints at why taking dark web safety measures is essential, even if you are jumping into the dark side of the internet only because of some curiosity.
Fake university certificates
For a long time, the Darknet has been famous for fake university and college certificates.
Malware and viruses
You can find almost every kind of computer virus and malware on the dark web, which is why it’s a primary source for spreading these digital threats.
Scams
There are reports of illegal services on the dark web, ranging from paid assassinations to the trafficking of sex and weapons. However, some of these alleged services, such as professional ‘hitmen,’ may be scams designed to defraud willing customers.
While some threats on the dark web are well-known, others may use its notorious reputation to trick users into paying large sums of money. Additionally, some users on the dark web may attempt phishing scams to steal personal information and extort victims.
Government monitoring
There is a significant risk that the government can target you for visiting a dark website, as many Tor-based sites have been taken over by police authorities worldwide. Even if a person does not make any purchases on illegal marketplaces like the Silk Road, custom software used by law officials can analyze activity and identify user identities.
This can lead to incrimination for other activities later in life. In some countries, exploring new political ideologies can be considered an imprisonable offense, and those who visit restricted websites could be placed on a watchlist or targeted for jail sentences. China, for example, uses the “Great Firewall” to restrict access to popular sites and prevent citizens from evading government restrictions.
Unverified content and Hoaxes
Reports of hitmen for hire and crowdfunded assassinations on the dark web are believed to be hoaxes. The indie game Sad Satan was claimed to have been found via the dark web, but inconsistencies in the reporting cast doubt on the story. Ross Ulbricht, the creator of Silk Road, was arrested on suspicion of hiring a hitman to kill six people, but the charges were later dropped.
The urban legend of ‘Red Rooms’ that features live murders has been debunked as a hoax. Some websites monitor and analyze the dark web for threat intelligence.
Social network
The Dark Web has a social media platform called the Dark Web Social Network (DWSN), which is similar to regular social networking sites. Users can create customizable profiles, have friends, and participate in forum discussions.
Traditional social media platforms such as Facebook have also created versions that work with the dark web to provide services across all dimensions of the World Wide Web. However, unlike Facebook, the DWSN requires users to remain anonymous and not reveal personal information to protect their privacy.
Terrorism
Terrorist groups have used the dark web since its inception due to its anonymity and lack of regulation. The dark web provides these groups with chat platforms to inspire terrorist attacks and ‘How-to’ guides to teach people how to become terrorists and hide their identities.
Bitcoin allows for anonymous donations, making it easier for terrorists to fund their activities and purchase weaponry. Some fraudulent websites even pose as fronts for terrorist organizations like ISIL. With the current technology, cyber terrorists can exploit their weaknesses to carry out attacks.
Illegal pornography
The most prevalent dark web content is child pornography, about 80% of its web traffic, despite being challenging to find. Other porn-related content found on the dark web includes revenge porn and sexualized torture, and the killing of animals.
Law enforcement agencies frequently target sites that distribute child pornography. For Example, In May 2021, authorities in Germany brought down Boystown, a child pornography network with more than 400,000 registered users. In the operation, police dismantled multiple pedophile chat sites, detaining four suspects. Among them was a Paraguayan man they believe was the network’s ringleader.
In a major 2015 operation, the FBI took down Playpen, the dark net’s largest child pornography site at the time, which had over 200,000 members. The founder is serving a 30-year prison sentence after his 2017 conviction.
Financing and fraud
Due to its anonymity, carding, fraud, and counterfeiting businesses are thriving on the dark web. Carding refers to the theft and illegal use of credit card information, and the dark web offers a platform for criminals to sell and buy such information.
Fraudulent activities on the dark web include phishing scams, fake identity sales, and the sale of fake products. Counterfeiting businesses create fake versions of popular products and sell them on the dark web.
The dark web’s anonymity makes it difficult for law enforcement to track down these criminal activities, leading to a rise in their prevalence.
Hacking services and groups
The dark web is rife with cybercriminals who offer their services either as individuals or as part of a group. These groups include Mazafaka, Trojanforge, Hack Forum, xDedic, and dark0de. Some of these cybercriminals are known to track and blackmail pedophiles. Moreover, hackers who offer their services over the dark web have also targeted financial institutions and banks.
Not all dark web services are genuine, and many scam “.onion” sites offer downloads infected with backdoors and Trojan horses. Being cautious while browsing the dark web is essential, as significant risks are involved.
Bitcoin services
Dark web marketplaces often rely on Bitcoin, a cryptocurrency known for its anonymity and flexibility. It allows users to hide their identity and intentions, making it a popular choice for those engaged in illegal activities.
To further obscure transactions, Bitcoin users can employ digital currency exchanger services to convert their Bitcoin into online game currency, which can later be converted back into fiat currency. Services such as Tumblers are also available on the dark web to help hide transactions. However, Bitcoin’s relevance in the digital world has also made it a scam target.
Cybercriminal groups like DDOS have carried out over 140 cyberattacks on companies since Bitcoin’s emergence in 2014. The attacks have led to the formation of other cybercriminal groups and Cyber Extortion. According to recent research, Bitcoin tumblers are increasingly used for money laundering.
The legality of accessing the dark web

The dark web sounds fascinating, with a thrill of the unknown and unexplored. Similar to the deep blue sea, most dangers are hidden.
Fortunately, it’s not a criminal offense if you simply search the dark web, but if you use it to carry out illegal activities, you get in trouble.
As much as the Darknet contains even the “good” stuff, it’s not a place you need to stumble about blindly without proper dark web safety.
In a nutshell, the deep web is not illegal as it’s a network for privacy and security-conscious people.
However, it’s illegal if you venture into the dark web to commit unlawful actions such as downloading child porn, buying fake documents, drugs, credit cards, and more.
The dark web has several convenient uses, which are not all basic. People who live under a government that deeply supervises or censors internet traffic eventually get attracted to the dark web.
Why? I hear you ask because it allows them to see news from the rest of the world or even order supplies that they cannot get in their country.
Journalists and whistleblowers also use the dark web to communicate without revealing their location or private contact information.
To give you a better idea, here are a few constructive uses of the dark web:
For using the internet anonymously
You will no doubt be surprised to learn that the Darknet hosts many websites similar to those you will find on the surface web (the visible/common internet we use).
Such sites include blogs, gaming sites, social media, and super-encrypted email platforms.
Buy items that are difficult to get otherwise
Some common pain relievers and sleeping pills available in the EU are illegal in various Middle Eastern and Asia countries. The dark web comes to the rescue in such cases.
Many turn to the dark to grab such medications with their private and secure networks.
Purchase legal goods secretly
DarkWeb “marketplaces” guarantee confidentiality and anti-surveillance for your online purchases that you simply won’t find on any other websites.
Swap data in countries that censor the internet
Many countries, such as Qatar, China, Cuba, Russia, and Turkey, censor internet content promoting political dissent. The Darknet offers a place of free expression where not even a chunk of these limitations exists.
Revealing the abuse of authority
The dark web allows political activists and media persons to report stories that may cause them problems with governments or dictatorial regimes, seeking to infringe on a person’s right to confidentiality.
Is it illegal to use Tor?

No, Tor is not strictly illegal to use. It is designed to provide online anonymity and privacy to its users. Journalists, activists, and individuals concerned about online privacy and security often use it.
Many people use Tor to avoid surveillance by government agencies, ISPs, or other entities monitoring online activities. Similarly, people in countries with strict internet access and usage regulations must use Tor clients or virtual private networks (VPNs) to access some public websites.
However, while using Tor itself is not illegal, some illegal activities can occur through the network, such as the distribution of child pornography or the sale of illegal drugs. It’s important to note that engaging in illegal activities is still illegal, even through the Tor network.
Also, it is worth noting that using Tor may draw attention from authorities if they suspect you are engaging in illegal activities or if your online behavior raises suspicion. Generally, it’s important to use Tor responsibly and in accordance with local laws and regulations.
Are dark websites illegal to use and visit?

The dark web is a controversial internet portion often associated with ‘Secret activities.’ While accessing it is not illegal, it may suggest that a person is attempting to carry out an activity that they cannot do publicly.
Anonymity on the dark web may be attractive to government critics and victims of harm who want to keep their identities private. However, criminals and malicious hackers also use the dark web to hide their illegal activities.
Although browsing the dark web is not illegal, it contains unsavory activities that can expose you to danger. Remember that any website engaging in illegal activities such as drug trafficking, weapons sales, hacking, and human trafficking violates international laws and, therefore, is illegal.
Getting onto the dark web using mobile devices
How to access the Dark Web on Android
You can access the dark web using your Android device by following a few steps. It is highly advisable to take all the necessary security measures discussed in this article to protect yourself. Follow these steps to access the dark web on Android:
- Subscribe, download, and install a reliable VPN like NordVPN.
- Download and install the official Tor app from the Google Play Store.
- Login to the VPN client and connect to a server of your choice.
- Open the Tor browser and start exploring the dark web.
How to access the Dark Web on an iPhone
The Apple Store does not have an official Tor app. However, several unofficial Tor apps get the job done. Follow these steps to access the dark web with your iPhone:
- Subscribe to a reliable VPN like NordVPN.
- Download and install a secure dark web browser for iOS.
- Log in to the VPN client and connect to a server of your choice.
- Launch the Tor browser and start exploring the dark web.
Watch out; your ISP could see you using the Tor

The internet providers and websites can still see that you’re using Tor, as Tor node IPs are public.
While a website can’t identify you or an ISP can’t decrypt your internet traffic; still, they can still see you using Tor, which can draw some unwanted attention and raise suspicions.
Tor Bridges or a VPN will help you to use Tor privately, as your ISP (Internet Service Provider) will not see that you’re connected to a Tor node.
So, if you aspire to use Tor privately, you can use VPN or Tor gateways (Tor nodes that are not publicly indexed).
Setting up Tor Bridges is merely extra work; you would need IT knowledge, too.
So it is always better to just subscribe to a VPN like NordVPN and use it with Tor (remember to connect to your VPN first and then turn Tor on).
What can my ISP see?
Your Internet service provider, or ISP, is your gateway to the Internet. Everything you do online goes through your ISP.
It means that unless you use a VPN that encrypts your internet traffic, they always receive all information about you and your digital life.
Your Internet Service Provider will see everything when your online data is not encrypted. Your ISP sees what websites you visit, what you do on social networks, your emails, etc.
Sometimes, they even know more than you would like about private matters, such as your health or finances.
With all this data, your ISP could create a very accurate profile of you and link it to your IP address. This is one of the reasons why it is always good to hide your IP address.
Subsequently, most countries have laws on data retention. These laws mark how long ISPs must save the data they collect.
Such legislation differs by country: in some places, the period is six months; in others, it is at least one year.
During that period, on top of the risk of accidental disclosure and theft, governments and the police could ask ISPs to share data.
If that happens, you can guess what happens to your data then. It is likely to differ by each provider and, again, by country. In most regions, laws prohibit your Internet Provider from selling your data to third parties. Furthermore, end-to-end encryption—like the kind securing your WhatsApp messages—makes that data unreadable to your ISP in the first place.
If you live in the EU and want to know what data your provider has collected about you, the GDPR gives you the right to request a full report.
Your data can end up landing anywhere
Ever since platforms like WikiLeaks and informants such as Edward Snowden revealed NSA PRISM Program and that several authorized institutions frequently spy on citizens worldwide, privacy has become an even hotter topic.
In this digital age, your data could be anywhere on the internet, meaning it could already be at the three internet levels (surface web, deep web, and dark web).
The chances are that you already have a presence on the clear web (the surface web), be it a LinkedIn profile, social media, Facebook, or any community involvement.
Also, your data is more likely on the deep internet in one way or the other. But you have to keep your fingers crossed that it remains there and hope the party holding your data (the school or hospital records department) keeps it according to the GDPR standards.
The cloud is another channel that has fueled the growth of the deep web. For instance, if a cloud storage firm like Dropbox gets its files on the Amazon web server, your data is already placed on the deep web.
It should not be a privacy issue unless the company gets hacked or your data is exposed accidentally.
Keep in mind, at any given time. You could be followed online by different groups and things such as:
- Internet service providers (ISP)
- Operating systems
- Your network administrator (Wi-Fi)
- Internet browser
- Apps
- Hackers
- Websites
- Governments
Can I get rid of my information from the dark net?
Removing your sensitive personal information from the dark web once it has been exposed is virtually impossible. This (practically) irreversible process highlights the importance of taking preventive measures by utilizing a service that monitors your data for potential breaches.
Consider changing your usernames and passwords as an additional security measure.
What can I do if my personal information is on the dark web?
If your personal information has been leaked on the dark web, your risk of identity theft and financial fraud significantly increases. This is why many people prefer an identity theft protection service and a financial and credit fraud protection solution.
By doing so, early signs of fraud can be detected in near-real time, such as new inquiries on your credit file, like new credit cards or bank loans.
Popular dark web criminal cases
Deep down, the tip of the iceberg is where over 90% of the internet content is. As much as the dark web is supposed to promote free speech alongside bypassing censorship, many shady activities occur there.
Many high-profile stories have shown up due to the press focusing on the dark web, and in recent years, several criminal cases have been thrown into the spotlight. Some of them include:
The Playpen Case
The child pornography site Playpen is one of the famous scenarios that resulted from the dark web. The site had only been up and running for about seven months, but surprisingly, it gained over 215,000 users.
Then, a law enforcement agency (still unidentified) provided information to the FBI that later accessed the site’s host server.
The FBI didn’t shut the site down either, but hosted it for about two weeks, during which they captured over 1,300 IP addresses of site visitors, which led to over 900 users being arrested, including the creator of the site, Steven Chase.
Silk Road
Silk Road was a black web marketplace that Ross Ulbricht created between 2011 and 2013. It was known for facilitating the sale of illegal drugs, goods, and services using Bitcoin cryptocurrency. He ended up with over 1.2 billion dollars worth of deals involving firearms, drugs, counterfeit cash, hacker tools, and hits.
Following its popularity, the marketplace attracted GBI, IRS, and other government agencies’ attention, leading to Ross’ arrest in 2013 and later life imprisonment for his role in operating Silk Road.
AlphaBay
Shortly after authorities shut down Silk Road, AlphaBay emerged as the dark web’s new leading marketplace.
In 2017, authorities shuttered AlphaBay because its founder, Alexandre Cazes, failed to cover his tracks. He communicated with his personal email, used the same pseudonym publicly, and left his crypto wallets unencrypted.
A series of security missteps had led them closer to the extent that even when the cops busted into him, he was logged into the site as “admin.” Days after the arrest, he was found dead in his cell, allegedly dying by suicide.
The Ashley Madison Case
A hacker group and the impact team in 2015 busted the dating site Ashley Madison, whereby the hackers threatened to release the users’ personal information unless the site and its sister site, Established Men, were closed.
After the company failed to meet their one-month deadline, the Impact Team made good on their threat. They moved to the dark web and started leaking the stolen user data.
Over 32 million IP addresses of members were released, including that of the site’s CEO, with hackers claiming that the site had fulfilled its primary purpose and that they were forcing members to pay to get their accounts deleted from the site.
We have discussed the most scandalous dark web cases in this article in detail.
FAQs
The primary purpose of the dark web is anonymous and private communication. Also, it contains several illegal goods, stolen data, credit cards, and more.
The dark web wasn’t the invention of a single individual but from efforts to build secure, anonymous communication. Its foundation is the Onion Router (Tor) project, developed in the 1990s with funding from the U.S. Naval Research Laboratory to protect sensitive government communications. Later released as open-source, Tor became accessible to the public, enabling anonymous browsing for activists, journalists, and everyday users—while also giving rise to today’s dark web.
