The dark web has evolved into a complex underground marketplace where cybercriminals buy and sell tools designed to exploit vulnerabilities and launch attacks. What once required advanced technical skills is now accessible to almost anyone willing to pay, thanks to the growing availability of ready-made malicious tools.
From ransomware kits to phishing-as-a-service platforms, these tools come with price tags that are often lower than expected, but the damage they cause can be massive. Businesses, individuals, and even governments continue to face growing threats as these tools become more affordable and easier to use.
This guide breaks down the real cost of malicious tools on the dark web in 2026, giving you a clear picture of what cybercriminals are paying, and what organizations stand to lose if they’re not prepared.
What is the dark web cybercrime marketplace?
The dark web often feels like an underground version of an online marketplace, except instead of everyday products, it trades in stolen data, hacking tools, and illegal services.
You can’t access these platforms through regular browsers or search engines. They require specialized tools like Tor, and once inside, the setup is surprisingly organized. These marketplaces feature detailed listings, seller reviews, customer support, and even bulk discounts, much like legitimate eCommerce platforms.
Transactions are also structured. According to HP Wolf Security, around 85% of dark web deals use escrow systems, where a third party holds payment until both sides complete the transaction. This builds trust in an otherwise risky environment.
Pricing follows basic supply and demand. Factors like freshness, effectiveness, and exclusivity determine value. For example, a zero-day exploit targeting widely used software can cost far more than outdated password dumps.
So, what exactly is being sold, and at what price? Let’s break it down.
Phishing kits and fake website tools
Let’s start at level-1, because this is where things get alarming fast.
Basic phishing kits lying around on the dark web are often free. Fake website page layouts start at around $50, whereas scam templates (the most stripped-down options for impersonating a brand) go for as low as $25. What about cookie grabber pages that steal active login sessions? Those can cost as much as $400 or higher.
The implication of this is that someone can literally start a phishing operation today at essentially no cost.
Scammers like to impersonate major platforms like Amazon, PayPal, Shopify, banking sites, and even Netflix. Kits for fake shop pages come with HTML-based customization, which makes the resulting page look so legit you’d hardly suspect it’s not. And sellers often advertise ease of setup as a selling point.
Not only are these tools cheap, but they also work. Researchers at Stanford University found that nearly 84 percent of people who scammers target with fake shopping websites actually engage with it, and almost half of them end up losing money.
Further, according to 2024 data, phishing panels (centralized platforms scammers use in managing phishing campaigns) cost $1,000 on average for a one-time purchase, plus a weekly subscription averaging $170.
Spoofers, which manipulate communications to make it look like it’s from reputable entities like banks or support teams, cost an average of ~$87. As for full scam pages? They go for an average of $50 per instance.
Moreover, a determined attacker doesn’t need much to get started. Just a few hundred dollars upfront, and they can run a multi-week phishing campaign targeting online shoppers. This low entry barrier is precisely why phishing is still the go-to move for cybercriminals, regardless of the target industry.
Malware: From cheap infostealers to expensive ransomware
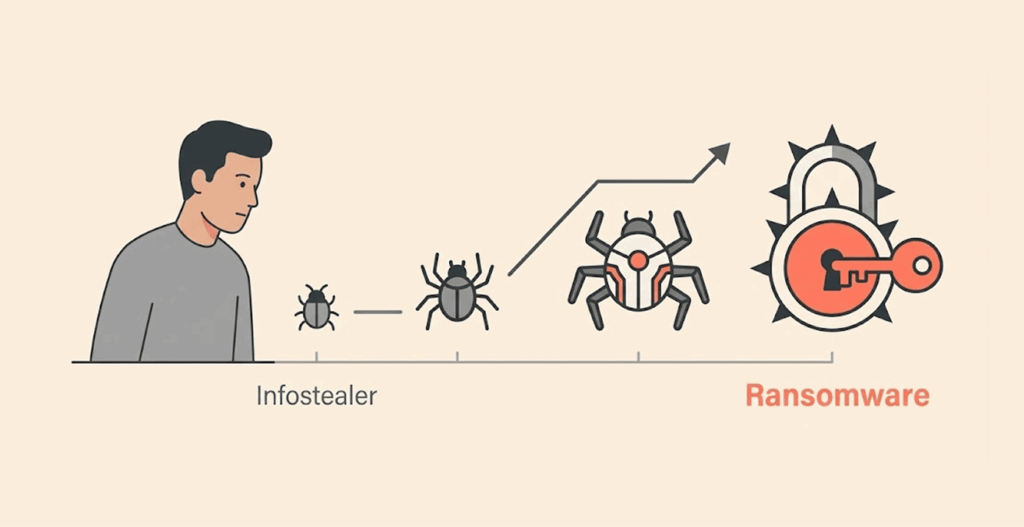
When it comes to the cost of malware on the dark web, the price range is very wide. From a few dollars for basic tools to hundreds of thousands for the most advanced exploits.
First, the information stealers
Folks in threat research circles often call these infostealers. They’re one of the most widely traded malware categories on dark web markets. Their job is to slip in quietly and quickly harvest information, passwords you’ve saved, browser cookies, crypto wallet credentials, and other sensitive data from infected devices.They’re designed to be fast and stealthy so as not to trigger any warning on the victim’s machine.
Dark web monitoring data shows that infostealers account for approximately 19% of all malware listings on the dark web. They have a median price of about 400 USD, the most popular families being Raccoon Stealer, which operates on a subscription model. Other stealers like BlackGuard sell on an on-time purchase basis, while cracked versions sometimes circulate on the dark web for free.
These tools package the data they collect as a “log,” which threat actors sell on secondary markets like the Russian Market for as little as $10 to $50 per victim. The life cycle from infection until the data gets to the dark web can take just hours. That’s faster than most companies’ threat detection systems can respond.
Ransomware and Ransomware-as-a -Service (RaaS)
One of the highest-priced items in the dark web cybercrime markets. Also, it’s the most commercially mature category of criminal products on the market today.
A recent study examining dark web markets found that ransomware is the most expensive category of malicious software, with amedian price around $7,500. Premium variants and custom-built ones can reach as high as $320,000. (You might want to read more eye-opening facts and stats about ransomware.)
However, the Ransomware-as-a-Service model is an even more significant development. It has reduced this cost and skill entry barrier to a large extent. Under this model, criminal groups develop and maintain the ransomware infrastructure, then rent it out to others who carry out the actual attacks.
Then there’s a more recent model, where the operators license the malware to affiliates who do the attack without necessarily having any technical skills, and they get to keep up to 70 to 90% of any ransom received. The operators, on the other hand, take a small cut for providing the tools, decryption keys, and, in some cases, victim negotiation support.
Entry into established RaaS programs usually requires a $5,000 investment and a verifiable dark web reputation. RaaS offers a stunningly large ROI, which is what makes it so persistent. A typical ransomware campaign can cost roughly $20,000 in total to set up, including infrastructure, VPN service, malware, and delivery tools. (If you need, we have curated a list of the best VPN services for the dark web.)
With one successful hit, the cybercriminals can net $100,000 to $130,000, a five-times return on investment. With that, they can recover the entire setup cost and still have a hefty balance. For most legitimate businesses, such a margin calls for celebration.
Ransomware attacks can cost big damages for businesses. Take, for example, CDK Global’s ransomware incident in 2024 that knocked the company’s servers offline for two weeks.
According to reports, CDK paid a ransom of $25 million to get things back online. But that’s not the only cost. They also recorded over $600 million in dealer losses. So the actual financial loss was way bigger than what the hackers took home.
Crypters, loaders, and obfuscation tools
These malicious tools work in the background, and their job is to help malware dodge detection and make sure it stays active long enough to cause damage.
Exploits (codes that take advantage of certain software vulnerabilities) have the highest average prices, often listed at about $5,345. Loaders, which are responsible for delivering and executing malware, are next in line, selling for $3,566 on average.
The subscription, based stealers sell for a lesser price, typically at an average price of about $1,024, showing how competitive and high-volume the market is.
On the service side, code signing signatures that make malware appear to be from a legitimate software publisher average 2,420 US dollars. Services that disable antivirus programs cost around 1,500 USD. Malware encryption services whose job is to scramble malicious code to avoid signature detection are sold for an average price of over 480 US dollars.
Then crypters and code obfuscators, obfuscation software, have a median price of about $70, and they make up approximately 17 percent of dark web malware listings. For just $70, an attacker can make known malware almost invisible to standard defenses, which is really troubling. If you want, you can discover some other interesting facts and stats about the dark web in our article here.
Zero-day exploits the dark web’s premium listings
This category sits at the high end of the price of cybercrime tools in dark web markets. But first of all, what’s a zero-day? A zero-day is a software flaw that the vendor doesn’t yet know about and therefore hasn’t patched it.
Since there’s no fix available yet, a working zero-day exploit can grant attackers access to systems that have done everything right defense-wise. Such exploits are rare, valuable, and very expensive.
The price of dark web listings for zero-day vulnerabilities varies widely depending on the targeted software, the exclusivity, and the exploit reliability. Premium zero-days can be valued from $10,000 to $200,000, according to stats. A zero-day in widely deployed enterprise software, one that hundreds of corporate networks are using, is priced at the very top of that range.
In July, 2025, a threat actor listed a WinRAR zero-day exploit for $80,000 on a prominent Russian-language dark web forum (an encrypted and hidden online discussion platform). WinRAR’s large global user base and the exploit’s verified reliability were what made the price that high. In underground markets, reliability and reach are variables worth paying for.
Top-tier tools like zero-days are often sold through auctions rather than fixed-price listings. Escrow services take care of payment security and often charge 4% commission on the transaction. Then who buys zero-days at such exorbitant prices? Usually, nation-state actors, sophisticated criminal organizations, and corporate espionage operations are the ones with enough funds to afford it.
Entry-level attackers can’t cough out such an amount for one attack. But the fact that this market even exists in the first place, openly accessible to anyone with crypto and Tor, is concerning.
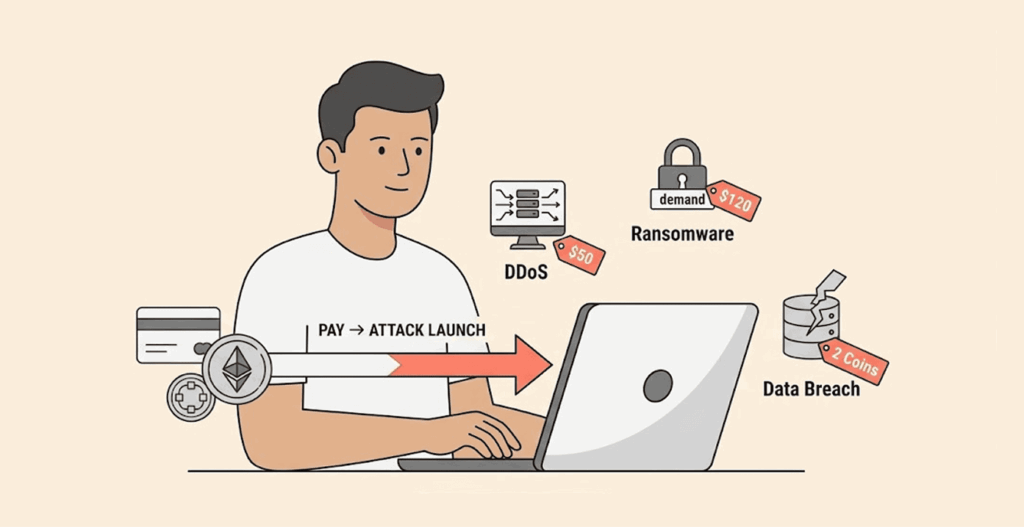
DDoS attacks and hacking-for-hire
Here’s a price that stops most people dead on their tracks – you can pay someone to know a website offline for as little as $20. Distributed denial-of-service (DDoS for short) attacks, which bombard a website or server with traffic until it collapses, are also available for hire for as little as a $20 subscription, according to our dark web market research.
Want to know another fact? So, stress test tools, originally meant for network testing, are misused for DDoS attacks, and are typically available for $10 on average for a subscription. Need for destructive power?
With just $200, you can run 24 hours of sustained attack that generates 20,000 to 50,000 requests per second against a site with DDoS protection. That’s less than what most people spend on a weekend dinner out.
The hacker-for-hire market operates alongside these tool listings. According to a recent dark web pricing research, social media account compromises, Facebook, Twitter, Instagram, etc, are available from $45 to $75. Social proof manipulation is equally accessible, with 1,000 Instagram followers going for $6. The big money seems to be from Twitter accounts, where you have 1,000 retweets going for $25.
Stolen credentials and personal data
Stolen data is arguably the most traded commodity in the dark web cybercriminal marketplace. Criminals use it to carry out identity theft, payment fraud, account takeovers, and corporate spying.
Here’s the current price range of some stolen credentials based on dark web monitoring research:
| Data type | Typical price range |
|---|---|
| Credit card details (standard with CVV) | $10–$40 ($110 to $120 for cards with more that $5k limit) |
| Bank login credentials | $200–$1,000+ (depending on how much is in the account) |
| Crypto exchange account, like Kraken | Up to $1,170 |
| Social Security numbers | $1–$6 |
| Hacked PayPal | ~$100 |
| Remote Desktop Protocol (A.K.A RDP) access | As low as $5 |
| Full identity package (“fullz”) | $20 to $100 up |
| Active session cookies (per batch) | Varies; widely listed |
| Facebook account | $45 to $50 |
| Gmail | $60 to $65 |
| Medical records | $500 up |
| US passport scan | Roughly $100+ |
(Based on dark web data pricing 2025 report)
That RDP credential figure is worth taking note of. It’s the point of entry into an organization’s network, more like a key to the front door of a house, and it sells for the price of a cup of coffee? That’s something you should be worried about.
Attackers who buy this kind of data don’t even need to start writing complex code or looking for loopholes to break in. They simply walk in like any other employee, no questions asked.
Buying valid login credentials for merely $10 to $50 makes the whole venture simpler, cheaper, and just as effective as complex exploits. That’s why credential-based attacks now account for approximately 16 percent of all breaches, according to IBM’s Cost of a Data Breach Report.
Furthermore, active session cookies are very dangerous because they let attackers access your account without needing a password and without triggering 2FA. This makes them one of the in-demand items in dark web forums.
Fake documents and identity fraud tools
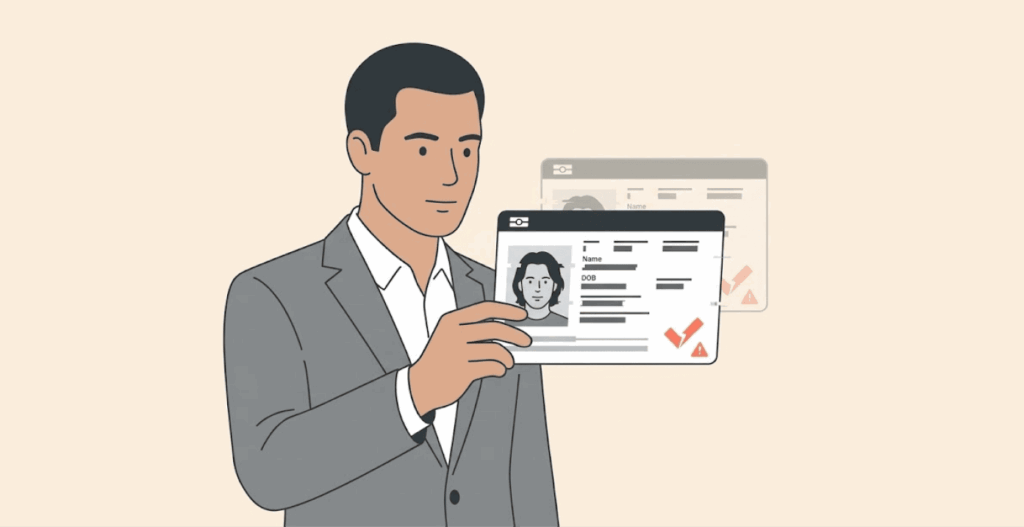
Digital tools aren’t the only things for sale on the dark web. There’s also a booming market for forged physical and digital identity documents.
Scanned copies of US driver’s licenses are also for sale there for around $70-$165. Other countries’ passports are a valuable asset on the dark web as well. European passports, the Netherlands, Spain, and France, make appearances there regularly.
Full identity packages, what most people in the underground markets call “fullz,” bundle a person’s name, address, SSN, and banking details all in a single purchase. Scammers use these to open fraudulent accounts, apply for credit lines, or to launder money through legit-looking transactions.
As you’re reading this guide right now, your personal information might already be floating around the dark web in one listing or another. We’ll talk more about how you can find out if your personal info is on the dark web in the sections below.
The rise of Cyber-as-a-Service (CaaS)
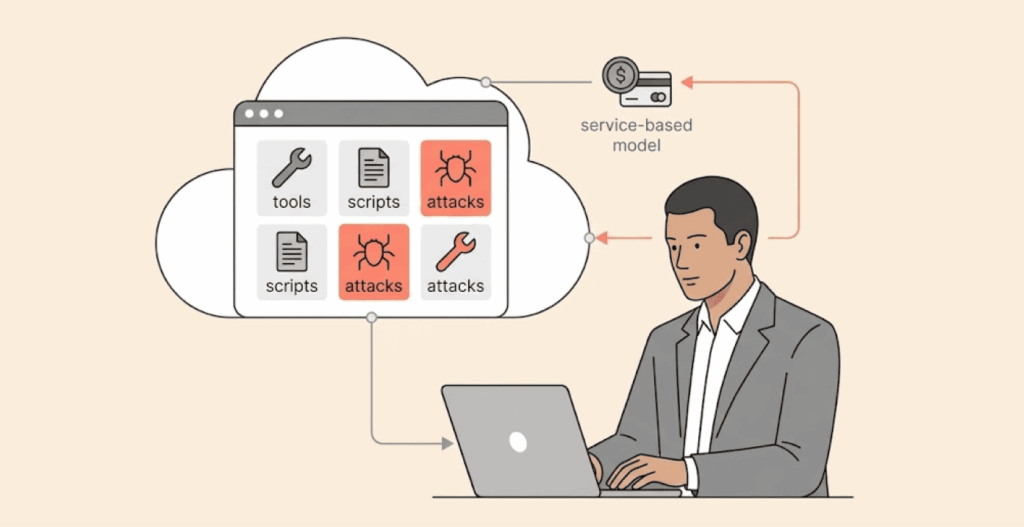
One of the things that has changed big time about the dark web economy over the years is the professionalization of cybercrime. It’s not just a hangout for elite hackers anymore.
These days, you don’t need to know the first thing about coding or hacking or have any real tech skills. You just rent a fancy setup from a skilled attacker, complete with tech support, how-to guides, and even regular updates, like how you subscribe to a legit service like Netflix or Amazon’s AWS.
Everything is detailed and looks genuine, except it’s all a bunch of criminal stuff. There are product reviews, version numbers, feature lists, and even bulk-buy discount codes, which are almost hilarious until you remember the damage these services cause in the real world.
And the menu? Astoundingly extensive. Under the CaaS umbrella, you’d find Ransomware-as-a-Service, Phishing-as-a-Service, DDoS-as-a-Service, Malware-as-a-Service, you name it. There’s payment by subscription plan or revenue sharing. Sometimes, if you get in on a ransomware gig, the people running the show will even help you handle negotiations with your victims.
The real kicker is the way this model separates technical skills from criminal capability. With a hundred bucks, literally anyone can just point and click their way to a ransomware attack or a phishing spree. There’s no skill gap anymore. What’s left are just the ethical and legal speed bumps, and, let’s be real, those clearly aren’t deterring as many folks as you might hope.
How AI is reshaping the dark web economy
Artificial Intelligence has totally changed the economics of cybercrime. And these changes favor attackers, at least in the near term. AI is already generating super convincing phishing emails by the thousands, faking voice calls that fool company execs, and churning out fake websites that look almost exactly like the real thing.
Just to put numbers on it, NordVPN’s threat intel team blocked 92% of shady domains in only eight months. We’re talking about everything from bogus online shops to investment scams and sites that try to hijack login sessions.
Take last year’s Black Friday craze, fake eBay sites surged 525%, and Amazon fakes weren’t far behind at 232%. Why? Because now any half-decent scammer with AI tools can create polished websites very fast and at very little cost. The barrier to entry is gone. Before now, you had to have skills or spend real cash, but not anymore.
On the pricing side, AI is creating a split market. Commodity attacks (like credential dumps, generic phishing emails, template-based scams) are very cheap now because AI automates the grunt work, making production costs lower.
But on the flip side, that custom, AI-enhanced fraud that uses targeted research, personalized messaging, and mimics behaviors goes for premium prices. You pay more, but get high-quality, convincing results.
It all adds up to this: if you’re hoping to spot phishing emails by typos, you’re going to fall into their trap; that era is over. AI drafts these scams so well that they’re so identical to real company emails. It deceives even people who know all the basics.
What does a full cyberattack actually cost to launch?
We’ve covered individual cybercrime tools and the categories, but what does a complete attack actually cost in the real world when you add everything up?
According to a study examining the dark web market, executing a popular ransomware phishing costs novice cybercriminals nothing less than $20,000. This amount covers everything needed to run a functional criminal operation, including renting dedicated servers, subscribing to VPN and anonymizing services, acquiring malware or RaaS access, and setting up delivery infrastructure.
For this $20,000 initial investment, one successful ransomware attack against a mid-sized business can yield around $100,00 to $130,000 in net profit. That’s a five-to-one return, better than most venture capital portfolios. That explains why new ransomware groups keep popping up every time law enforcement shuts one down.
Operators with higher skills investing in better tooling (like zero-days, AI-generated phishing content, sophisticated lateral movement tools) can spend much more money. Despite the high $20,000 entry point, there is still a massive economic advantage for attackers, making it difficult for law enforcement to stop the expansion of the cybercrime dark web marketplaces.
How to protect yourself from these threats
These prices of cybercrime tools should be an eye-opener for everyone. One thing to learn from this is that no one is exempt from these threats. Cybercrime is everywhere now, and you should start taking your own security seriously. The best defenses cost nothing; by observing a few OpSec habits, you can keep out of harm’s way. (We have rounded up the top cybersecurity tips to stay safe online.)
1. Strong, unique passwords and a password manager can save you a lot of headaches
Credential stuffing succeeds because people often reuse one password for almost all their accounts. One site gets breached, and attackers are armed with the key to every other account where you’ve used that password.
If memorising multiple passwords stresses you out, get a password manager (Bitwarden is free. 1Password and Dashlane are decent and affordable options). It helps you generate very strong passwords for every account automatically and stores them for you.
2. Multi-factor authentication (MFA) matters a lot
MFA is one of the most effective ways to prevent credential theft. Should someone manage to get their hands on your login credentials, maybe a dark web listing, they still can’t access your account because they have to pass second-factor verification.
Wherever possible, use app-based authentication (think Authy or Google Authenticator) rather than SMS verification. The reason? SMS codes are easy to steal; with the help of SIM-swapping, someone can easily bypass that step.
3. Avoid too good to be true deals, especially during shopping seasons
Research shows that the majority of consumers (about 68%) find it hard to differentiate between spoof sites and legit ones. Don’t be too fast to enter your credit card info on any site.
First, double-check the URL, check if it has any typos, and also check if the link in your browser has the little padlock for HTTPS, which is a sign the site is secure. When you’re unsure, just type in the site yourself instead of clicking some random email link.
4. Update all software, don’t sleep on updates
Many exploits floating around for sale on the dark web target known and already patched security holes. They’re banking on the reality that millions of users fail to get the updated version and just continue to use the unpatched one for months, even years.
So patch your operating system, update your browser (better use secure browsers we put together in this list or any other of your choice), and don’t skip app updates. Current updates aren’t just for fancy; they close the door through which known attack vectors can enter. That alone knocks out a ton of the malware they throw your way.
5. Sign up for dark web monitoring
Services like HaveIBeenPwned are free and take like two seconds to check. If you can spare a few bucks, then go for the likes of NordVPN’s Dark Web Monitor or 1Password’s Watchtower.
They’ll keep an eye out for your information in dark web data dumps. When your email or password pops up in a breach, you get an alert early so that before scammers have the chance to get into your accounts, you change the password and sign out everywhere.
6. Wipe out cookies regularly and review active sessions
Attackers sometimes just hijack your session cookie to bypass your password and MFA completely. Clearing cookies limits the validity window of a stolen session. Most browsers even let you set cookies to clear as soon as you close the browser or page. It takes just 30 seconds to set up and shuts the door on a major attack vector.
7. Don’t just download anything you find floating around online
Stealer malware is dirt cheap, so basically anyone can get in on credential harvesting these days. Avoid downloading your apps from unofficial sources, cracked software repositories, or some random website you stumbled upon through a Google search.
Doing so is tantamount to buying sushi by the roadside from the trunk of someone’s car. If you wouldn’t trust a physical product from an unverifiable street vendor, why take the risk with your app downloads?
FAQs
Cybercrime tools come at every price point, and that’s what makes them so dangerous. Basic phishing kits can be free, scam templates start at $25, and RDP access can cost as little as $5. Mid-tier tools like MaaS run $100–$200/month, while full ransomware kits average $7,500. At the top end, zero-days can fetch $10K–$200K, and complete ransomware operations cost around $20K, small investments with potentially massive returns.
Yes, buying cybercrime tools is illegal worldwide. Laws like the Computer Fraud and Abuse Act and the Computer Misuse Act hold both buyers and sellers accountable, and authorities actively track, shut down, and prosecute offenders.
Crypto payments are preferred for almost all dark web transactions. Bitcoin is still the main pick, but many now prefer Monero because it’s harder to trace. The majority of popular markets on the dark web use escrow services, in which cryptocurrency payments are held until the buyer receives the materials before the money is released to the seller. Typical trust-but-verify scenario. Escrow fees run about 4% of the transaction amount.
It all comes down to supply and demand. Constant data breaches flood the dark web with stolen info, driving prices down for basic credentials. What stays expensive is fresh, high-value access, like active sessions, funded bank accounts, corporate logins, or crypto wallets. In short, the newer and more valuable the access, the higher the price.
Catching dark web criminals isn’t easy, but it happens. Major takedowns like Silk Road shutdown, AlphaBay takedown, Hydra Market shutdown, and Genesis Market takedown prove it. Authorities track blockchain activity, run undercover ops, and exploit simple mistakes, because even with tools like Tor and Monero, anonymity is never perfect.