As the importance of securing online accounts keeps growing, more and more people keep hearing about 2-factor authentication (aka 2FA). As you are here, chances are you, too, are one of them.
In this article, we will discuss in detail about two-factor authentication and how to enable it.
Understanding 2FA
Whether you open an account on a website or app, you must input your credentials. Login credentials consist of a username or email and password.
Usually, you only need to input your login credentials to open your account. It seems insecure, right? Definitely. So why do we still practice it?
Most websites and services advise users not to share their login credentials with other people for good reasons. However, if you think about it, using even the best VPN and password manager might not be sufficient.
Therefore, to protect your account, if someone manages to gain access to your login details, you should also use a two-factor authentication process.
Arguably, it will be an inconvenience to users if websites add extra steps to the login process. If companies require authentication, everyday users might find it complicated or time-consuming.
Indeed, they won’t risk losing users for that reason.
However, if you want added protection to your accounts, you should look at 2FA. It’s a method that’s both free and easy to use. All you need to start using 2FA is only tinkering with your account settings a little.
That brings us to the question, “What is 2-factor authentication?” While it may sound complicated, it’s pretty simple to understand. You don’t need to be very technical to grasp its function.
In essence, 2FA or Two-Factor Authentication is an extra protection layer for all your accounts that you can add in different ways.
As the name suggests, Two-Factor Authentication is a security method that requires a user to provide two types of information to access an account. As a result, it enhances the security of devices, accounts, and even a smart door.
It’s more like a screening process before you can open something.
As noted earlier, websites and services do not activate it by default, so you will have to configure it on your account settings manually. Better yet, though, you can enable it by mostly merely toggling an option in your account, which is usually labeled accordingly. After activation, your login process should have an additional step.
With 2FA activated, you should receive a code either by SMS or generated from an app once you attempt to open your account. You then paste the code into the login prompt. If the code is correct, you should be able to log in successfully.
Two-factor authentication is of too much value and use. It helps secure your accounts at the very best level. With it, no one could unlock your account, even with an exposed password.
Forms of two-factor authentication (2FA)

If it’s your first time getting started with two-factor authentication, you should know that it has different types. Even though these methods approach 2FA distinctly, they all serve the same purpose.
Here are the several methods by which you can use 2FA:
1. SMS-based 2FA
A text message is the most straightforward type of this authentication.
With this type of 2fa activated, when you log in to your account with your credentials, the website will send a code to your phone number. You will then paste the code into the login form to open your account.
When you enroll your number, you need to input it into your account settings. Then, you should receive an SMS with a code to prove that you own the number. After that, you will always get a text message for every login attempt.
We came across some past reports suggesting that this method is not 100% as hackers can intercept an SMS and capture your code during our research. In addition, some websites also use your number for targeted ads or tracking, making it more unappealing for some.
2. Authenticator app 2FA
A more secure and popular type is by using an authenticator app. It locally generates codes based on a private key. Unlike SMS, where you have to wait for a code to arrive, you can view and use the latest code in the app even before logging in to your account.
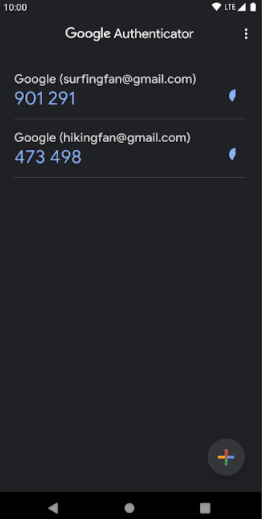
This method utilizes the Time-Based One Time Password (TOTP) technology, which generates temporary passcodes that use the current time.
If a website supports this 2FA type, you will see a QR Code. All you need to do there would be to scan the QR code (using your authenticator app) to have access to the private key.
After activation, the app will generate offline codes that you can use immediately. For example, if you log in to a website, it will prompt you to input a code. Once you launch the app, a code will be there automatically, so you can quickly paste it and open your account.
3. Security keys for 2FA
A modern implementation of two-factor authentication is security keys. These are usually small thumb-drive-like devices that you can plug into your computer. With it, you can unlock your account without using any code.
You can call it a hardware-based 2fa for your online protection.
It works by automatically sending a code based on the detected website you’re using. This 2fa form is considered more secure than other types covered above since it requires a complete website name and URL for verification, which protects against different cyber threats like phishing.
However, there are some limitations to it. For instance, only a few browsers support it—also, it’s costly, and only a few products out there work with mobile phones as of now.
Where to use 2FA
Implementing 2FA on all accounts a user owns can be quite a chore. Especially since most of them probably are registered to many websites and services.
Some might only want to secure a few of their accounts, mainly the important ones.
If you have no idea where to start, then here is a list of services types you should prioritize enabling 2F authentication on:
- Financial services. Today, most banks allow bank account management online using a mobile app or a website. Such transactions are sensitive, so it’s a no-brainer to use any extra protection you can. Therefore, you must enable two-factor authentication for all your financial accounts. The good thing, all major banks worldwide offer 2fa today.
- Email services. These are probably some of the most important accounts that you have online. Whether it’s for accounts registration, professional communication, or sharing important information, we all use emails today mostly. That is why it makes all the sense to encrypt your emails and add any available extra security layer to them. Fortunately, some email providers, such as Gmail, made it easier to set up 2FA on accounts.
- Social Media. Social has taken the world by storm. Today, more than ever, we are sharing so much stuff and communicating online on social media. With that much data, it is necessary to enable two-factor authentication on your social accounts.
2FA applications
Currently, there is a plethora of 2FA apps available. However, only a few are trustworthy (and hence widely used).
The most recognized ones include Google Authenticator, Authy, Microsoft Authenticator, Duo Mobile, and LastPass Authenticator. Although all of these perform phenomenally, Google Authenticator has been the default choice for many. For some good reasons, of course.
An advantage of dedicated authentication apps is that they work even offline. Unlike SMS, where you should have a network reception and wait for the code to arrive, codes in authentication applications are available instantly.
Another reason behind their optimum security is the lack of live data transfer during login.
However, if you lost your device where you got the app installed, you will experience difficulty accessing your account.
One thing where authenticator apps can improve is an option to back up the codes. Unfortunately, even the apps built by the tech giants such as Google, Amazon, and Apple lack that function.
We think companies should think about that. It’s a vital feature that such apps should have.
Anyone can lose their phone or reset it for various reasons. If that happens, your only option would be to turn to the service itself, where you set up 2FA for your account.
Resetting your 2FA through that route takes two days on most websites and apps (due to added security measures). Yes, some 2fa apps like Google Authenticator allow you to have code backup to another phone. But not everyone can afford two phones.
Example services that offer 2fa
As mentioned earlier in the article, many websites support 2-factor authentication. However, there are some services and platforms that require or advise users to use 2FA by default. Below you go with some of the well-known web giants that implement 2FA:
- Apple. Every time you log in to a new Apple device, you will receive a security code in your email. It will make your account usable on that device. Indeed, 2-factor authentication by Apple is an excellent example of 2FA implementation.
- Facebook. The social media giant has long been supporting 2FA. If you want to have better Facebook privacy and the best possible security, make sure to use its two-factor authentication feature.
- Instagram. Because Facebook owns Instagram, its security and reliability are just as good. It has the same 2FA strength as Facebook.
Why only passwords are not enough
Usually, a login credential consists of a username or email and password. Although you use strong and unique passwords, it’s still not enough to secure your account.
Many websites use the registered email as your username, so if someone knows it, then your account’s only protection is your password.
You may also log in to a website with your real display name in some cases, making it easier to break into your account.
Your passwords are more at risk today as hackers go to extreme extents for carrying out malicious activities. There have been numerous breaches and hacks reported in the last decade, a trend which we predict to get even aggressive as we step into 2021.
That is why security is something you might want to think about. And, despite all the advancements, passwords remain your only defense in most cases.
Passwords are vulnerable to many attacks and techniques that hackers do online. A prevalent one is a dictionary attack where hackers run scripts to guess your password alphabetically continuously.
Most of all, let’s not forget how most people have repetitive and simple passwords that are easy to hack, making them even insufficient for account security.
Arguably, most of the services and websites now indicate if your password is weak or strong when you try creating one on them. Although this is an effective action, it can only protect your information to an extent.
Some considerations
There is no such thing as total security because no matter how secure a network or account is, there’s always a threat lurking around. And, something like 2fa authentication is no exception.
However, any 2FA is better than nothing. Even though it doesn’t guarantee 100% protection, these extra login codes add an extra layer of security.
Besides, there is no guarantee that all websites and services you use do allow 2-factor authentication. So make sure to check your account settings to learn more if it supports 2FA and how you can use it.
Gaining security against inconvenience
Setting up 2fa requires you to go the extra mile and take additional steps. But since you must prioritize your accounts and data security in this ever-increasingly dangerous cyber world, any minor inconveniences should not bother you.
Instead of logging in directly with just a username and password, you can better wait for an SMS or open an app to access an account.
Yes, it might become annoying and time-consuming in the long term.
However, these inconveniences are what make your accounts more secure.
2-factor authentication vs. 2-step verification
There’s a chance that you already heard about 2-step verification. While it may seem no different from 2FA, there’s a significant distinction between the two.
To understand the difference, you need to learn about the forms of authentication available today.
Here are the three forms of generally used authentication:
- Single-factor authentication: Only requires the input of a password or PIN.
- 2-factor authentication: Requires single-factor and OTPs generated from apps or hardware devices. Examples would be an authenticator app and a security key.
- 2-step authentication: Commonly known as 2-step verification, it only requires a single-factor and a code sent to the user. Sounds familiar? That’s because this is how SMS 2FA functions.
You might wonder why SMS is a 2FA type even though it functions as a 2-step verification. Since in that case, 2FA sends code to “something you have,” which could be a phone. And then, as mobiles are the SMS receivers, we can infer that it is a 2-factor type. However, some sites, such as Google, refer to SMS OTPs as 2-step instead of 2-factor authentication.
In essence, 2-factor authentication is more secure than 2-step verification. Think of it like this: 2FA identifies the user, while 2-step verification only allows access.