Cyber threats are evolving faster than ever in 2026, targeting organizations through hidden vulnerabilities, misconfigurations, and increasingly sophisticated attack methods. As these risks grow, businesses can no longer rely on reactive security alone.
Cyber threat management has become a critical, continuous process, focused on identifying, analyzing, and mitigating threats before they turn into serious incidents. It goes beyond tools and checklists, helping organizations stay proactive and resilient in a constantly shifting threat landscape.
In this guide, we’ll break down what cyber threat management is, why it matters in 2026, and how you can implement it effectively with simple, practical steps.
What is cyber threat management?
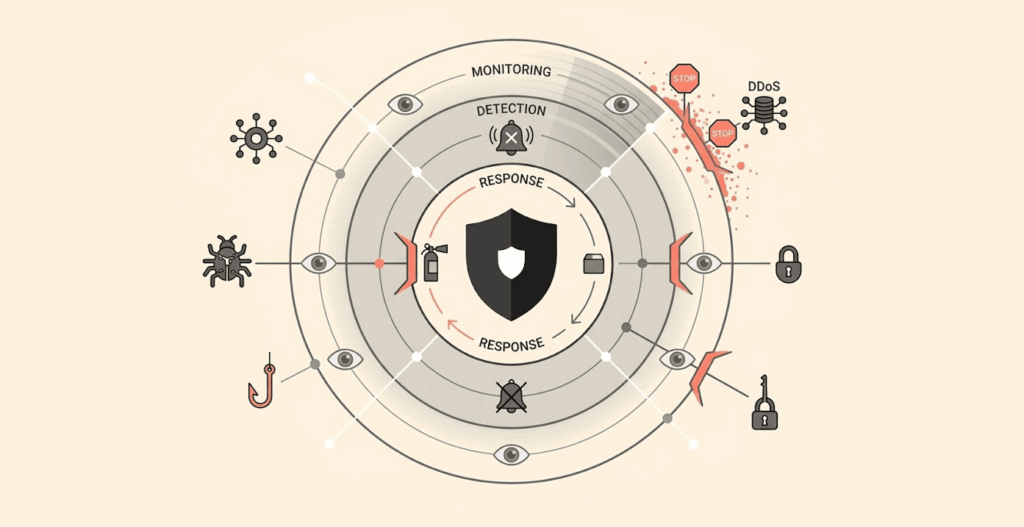
In simple terms, cyber threat management is a continuous process of detecting, evaluating, ranking, and responding to cyber threats; its purpose is to reduce the amount of risk exposure that an organization faces as well as to stop the occurrence of security breaches.
It is a planned, systematic method of assisting security teams in identifying, understanding, and preventing cyber threats from damaging an organization.
The term ongoing indicates that this process is not one in which you just ‘finish’ and then you’re done (such as installing a firewall). Threats are always evolving; your digital footprint continues to grow, and attackers change their tactics. Thus, your threat management processes must evolve as well.
As cloud computing, remote work, and the rapid growth of IoT devices expand the digital attack surface, organizations face an increasingly complex threat landscape.
Cyber threat management enables an organization to remain ahead by integrating threat detection, intelligence gathering, response, and validation into a continuous lifecycle of permanent protection and resilience.
We can think of traditional security as building a stronger wall, while threat management involves installing cameras, training guards, conducting regular patrols, and continuously testing whether anyone can climb over the wall without being detected.
Cyber threat management: Its importance in today’s world
You might be telling yourself: “We have virus protection. We have firewalls. We have someone monitoring these alerts. Should that be enough, right?”
The answer is actually no, and here are several reasons why cyber threat management is critical in today’s world.
1. A growing and evolving threat landscape
Remember when the vast majority of cyber threats were just an email from a scam prince (known as email phishing) asking for your bank account information? The old days are long gone!
These days, threats are more advanced, persistent, and purposeful than ever before. Attackers no longer just randomly send emails and hope someone responds; they research and investigate your organization, your vendors, and sometimes even your employees.
Also, attackers now take advantage of their victims’ supply chain, use application programming interfaces (APIs) to gain access, and utilize properly configured cloud storage to get into your system. Ransomware gangs resemble legitimate businesses in every way; they have human resources departments, customer service personnel, and entry-level workers, mid-level workers, and upper-level workers.
Nation-state-sponsored malicious actors can remain undetected for months at a time and map out their intended targets’ critical infrastructure.
The rapid shift from an office-only workplace to a hybrid/remote worker environment has created an even bigger mess than before. Employees can now access their companies’ data from their homes, coffee shops, restaurants, and airports.
Therefore, cyber threat management is critical for your organization and provides you with a fighting chance in the current environment.
2. Business risk is cyber risk
A critical inquiry for today’s corporations is: “What will our financial loss be as a result of a cyberattack?”
Cyber threats have evolved from being solely technical challenges to being substantial risks to the enterprise as a whole. An attack can cause harm to revenue, reputation, and consumer trust, and an outage of the business reduces operational revenue. Data loss means legal liability. Customer churn after a breach is real and expensive. And regulatory fines? They can run into the hundreds of millions.
When looking at cyber threats in this context, threat management becomes less about technical conversation and more of a boardroom discussion. It is no longer a conflict of computer nerds versus criminals but rather a matter of the organization safeguarding its future.
3. Compliance requirements
If concern over business risk doesn’t capture your attention, perhaps concern over regulatory fines will.
There are now multiple data security and privacy regulations (GDPR, HIPAA, PCI-DSS, ISO 27001, etc.) that explicitly require organizations to demonstrate their ability to detect threats, respond to incidents, and mitigate risks over time.
For organizations seeking a structured approach to compliance, the NIST Cybersecurity Framework (CSF) 2.0 provides globally recognized guidelines for security governance and risk management.
Regulatory entities want to see more than only having security controls in place; they want to see evidence that an organization is working to continuously monitor, respond to incidents, and improve.
You can secure such evidence through proper cyber threat management. It provides a defensible way to show regulators, auditors, and customers that you are committed to protecting their data.
4. Operational resilience
We define operational resilience as an organization’s ability to maintain operational capacity even during attacks such as cyberattacks.
Additionally, cyber threat management supports an organization’s resiliency through prompt detection, preparedness, and coordination with other departments.
Organizations that have developed mature cyber threat management capabilities do not panic when an incident occurs because they have clearly defined processes and roles, and have received training on the specific incidents.
They also understand who to reach out to for assistance in terms of reporting the incident and what actions should follow after the incident occurs.
As a result, organizations that can operate with resiliency will have shorter recovery times, less organizational damage, and greater overall confidence than organizations that do not develop and practice their cyber threat management plan.
Thus, the main distinction for an organization that successfully recovers post-attack versus one that struggles to recover post-attack will ultimately be relative to the operation’s level of resiliency at the time of the attack.
How cyber threat management works
Many people misunderstand cyber threat management, taking it as a stand-alone application that you purchase, install, and simply forget.
However, it is more of a layered and continually evolving process that consists of multiple major components and enabling technologies. As an example, think of it as a living process rather than as a tangible product.
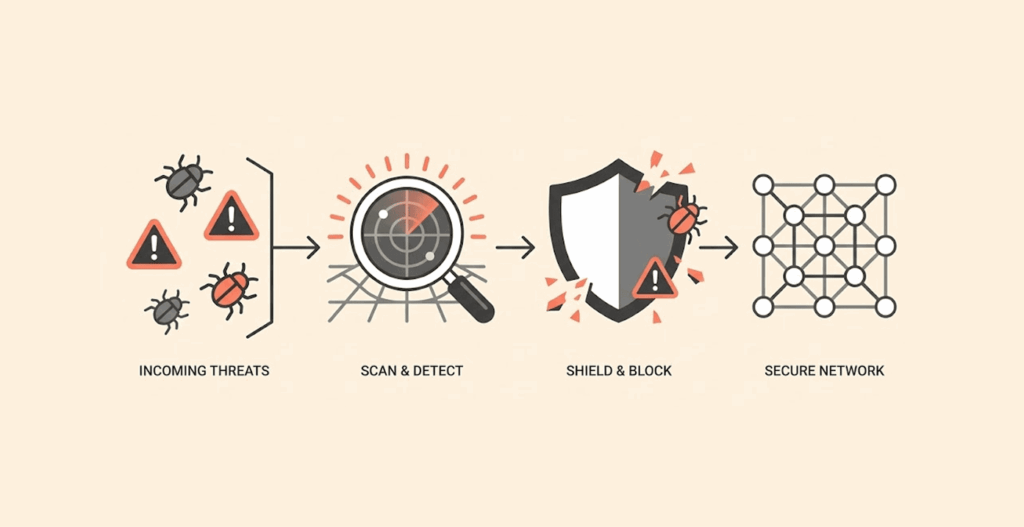
The key stages of cyber threat management:
1. Threat detecting process
To inhibit a given threat, you need to first be aware of its existence. Threat detection is the identification, in real time, of suspicious behaviors. There are various tools available for threat detection, including SIEM (Security Information and Event Management), IDS/IPS (Intrusion Detection & Prevention Systems), and Endpoint Monitoring Solutions.
The systems provide real-time alerts when they detect no-longer-normal behaviors, such as strange/unusual login from an unknown geographical area, a file performing abnormally, a spike in outbound connections at 3 am, etc.
2. Threat intelligence gathering
Detection tells you what happened; intelligence tells you why it is important. Collecting intelligence is the process of gathering data from both internal log files and external sources, such as industry threat feeds, government advisories, and the dark web (the hidden part of the internet), to gain a better understanding of the attacker’s tactics, techniques, and procedures (TTPs).
Here’s where things get personal. While scanning the dark web for threat intelligence, you might stumble across something chilling: your own company’s leaked data (or even your personal one). Yes, that happens more often than you think. So let me ask you; what would you do if you found your own information lurking in those shadowy corners? Don’t wait for a breach to figure it out. We’ve laid out clear, practical steps in our guide on what to do if your information is found on the dark web. Go read it. You’ll thank yourself later.
All that additional context turns a raw alert, such as “abnormal execution of PowerShell,” into something actionable: “This matches the behavior of a known ransomware group that targeted our vertical industry.”
3. Threat analysis and prioritization
Here’s the hard truth: Your team may never have time to review every single alert due to the large number of alerts. Therefore, threat analysis and threat prioritization will separate the “signal” from the “noise.”
The systems analyze threats using three risk-based measurements: risk (assessment of danger), likelihood (how likely is it that someone could exploit this vulnerability?), and impact (if this vulnerability were exploited, would that cause my company significant financial harm?).
Thus, a highly critical vulnerability in a public customer database would be addressed more quickly than an alert that a system triggered on a past test machine that has been decommissioned.
4. Threat mitigation
Once a system confirms a threat to be a legitimate one, mitigation will begin. Threat mitigation is actively working to neutralize a threat before it can cause damage.
There are many ways to mitigate a threat, including applying an emergency security patch, segmenting a compromised device from the network, blocking a malicious IP address, and forcing all affected accounts to reset their passwords. The goal of mitigation is to “stop the bleed”.
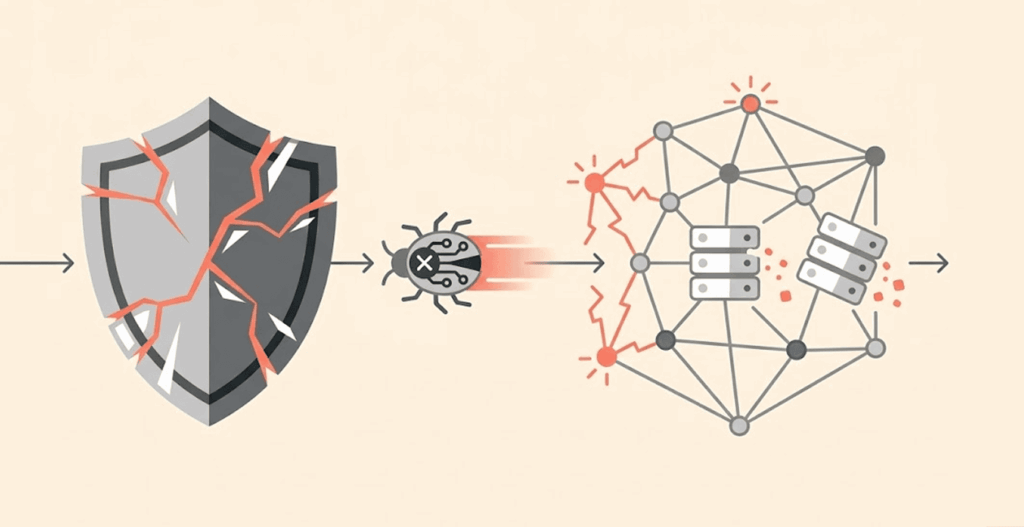
5. Response planning and incident handling
No matter how well you prepare for an incident, one will happen eventually. No security system is bulletproof. You will not find yourself panicking when an incident occurs once you have an incident response plan in place.
Creating specific procedures or playbooks for each potential event (for example: ransomware, data breach, insider threat, etc.), along with forming your incident response team, will provide the direction and responsibilities as to who should do what, along with providing you with the written procedures needed in the heat of the moment. When an incident occurs, you don’t want people asking, “What do we do?” You want them to execute a plan they already know.
6. Post-Incident analysis and improvement
Many businesses make the mistake of not conducting a post-incident review step of their plan. Skipping this step is a costly mistake. Once an incident’s resolution has been made, there must be hard questions, such as: What went wrong? What went correctly? How did the attacker gain access? Why were they not caught sooner in the prevention stages? What will be done differently in the next incident?
From the answers you received during this phase, the knowledge gained and processes improved and updated for all previous phases of incident response, detection enhancements, intelligence refining, and gap closing will occur. In this manner, the business can continue to improve.
7. Supporting technologies
All of the incident handling life cycle stages do not happen in a vacuum; they rely on a stack of technical solutions to provide the necessary support:
- SIEMs/Security Information and Event Management help to aggregate/collect and analyze event and application log data for the various parts of the environment to detect anomalies and correlate events.
- EDR/XDR (Endpoint Detection and Response/Extended Detection and Response) detects incidents at the endpoint level (desktop/laptop, server, mobile device) and extends that detection to all areas of the broader environment (e.g., email, cloud computing, and network).
- Threat Intelligence Platforms help add context to raw threat intelligence data so that analysts can better understand what attackers are doing and how that relates to their organization.
- Exposure Management Platforms can help to discover and continuously monitor your attack surface (including unknown assets).
- Breach and Attack Simulation (BAS) proactively tests your environment by simulating various real-world attack scenarios in a safe environment.
These tools don’t replace human analysts; they empower them, and handle the massive scale of data and alerts so humans can focus on the decisions that matter.
Common challenges in cyber threat management
Even organizations with the right tools and good intentions run into real, stubborn problems when trying to execute cyber threat management effectively.
These are not edge-case scenarios; they are common pain points. You can prepare for potential issues through advanced identification, rather than discovering you were unprepared.
1. Alert fatigue and resource constraints
The uncomfortable truth of modern-day security operations is that your organization can have an overwhelming feeling. Security tools generate alerts; a lot of alerts. In fact, there are thousands of alerts they can generate every day, and sometimes, even tens of thousands of alerts.
Your employees need to review, assess, and act upon each alert. To add to this, the vast majority of security teams do not have enough humans/staff to adequately assess the number of alerts issued by the various tools in place within their organization relative to the size/risk of the organization.
This will lead to alert fatigue as analysts become desensitized to alerts; the net effect is that legitimate threats will be missed, and employee burnout will create a situation where organizations will experience retention issues.
The solution to the alert fatigue and resource constraint challenge is NOT to just hire additional staff; rather, create a discipline to be sure to protect the critical assets and to issue alerts only when there is a significant threat. Secondly, teams should utilize technology and trusted partners to expand their ability to do their job without being overwhelmed by alerts.
2. Struggles with prioritization
Even with manageable amounts of alerts, teams typically struggle with the question of where they should start answering an alert. “What is the first thing we should work on?”
Not all threats are equally dangerous. A vulnerability in a development sandbox is not as dangerous as a vulnerability in a customer database.
However, if organizations fail to establish data-driven prioritization methods for their alerts, everything seems time-sensitive, i.e., teams will use the loud-dominance or last-reported-to method instead of fitting their working efforts into what truly has an impact on business.
The challenge is not a lack of technology; it is a lack of structured systems for assessing an organization’s crown jewels and understanding its threat landscape.
Once identified, organizations can establish a consistent risk assessment method to determine which risks require immediate attention and which can wait until next week.
3. Siloed data and tools
Just like people collect junk in their “junk drawer”, organizations can use multiple security products that have no connection in any way. They often result in partial and incomplete data due to fragmented views of your environment through various security tools that work independently of one another (e.g., network security, endpoint protection, and cloud security).
The separation of security tools can create gaps in your data set/the network, and therefore gaps in detection. Security analysts expend significant effort putting together disconnected clues left scattered by the various security products rather than building a complete picture of their organization’s security.
For an organization to break down these silos, they need to ensure that both its IT (integrated) and Business (aligned) functions collaborate to develop an end-to-end security solution. Security has not only become a discrete function like other operational services, but rather multiple sources of information/alerts to monitor.
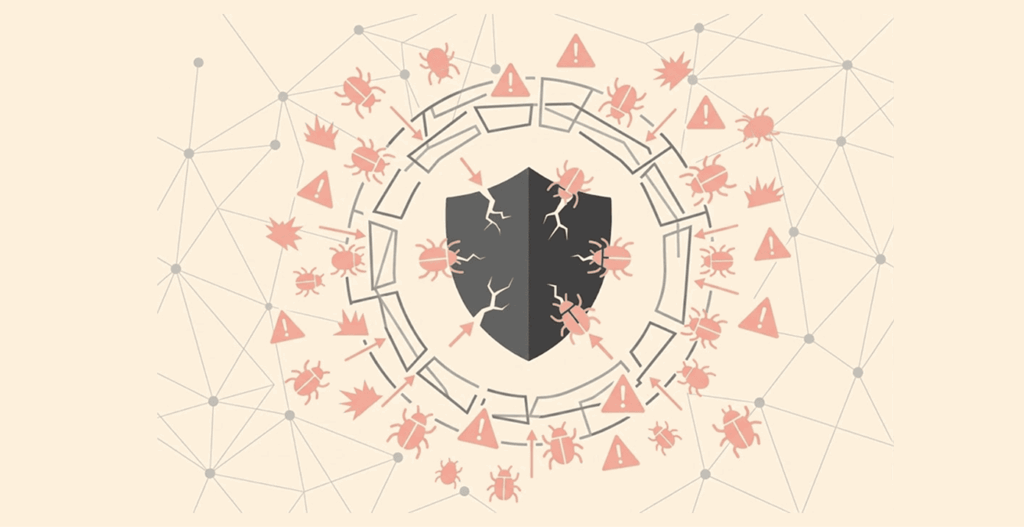
4. Evolving threat landscape
New/existing threats will continue to evolve as attackers develop new strategies and more sophisticated techniques to evade new security measures beyond the ones developed in the past.
Organizations are playing a constant game of “catch up” with dynamic threats, and having an effective/efficient security process requires organizations to have an ever-changing process to remove the expectation of knowing the future attack vectors.
The concept involves establishing processes that are self-evolving through threat intelligence, regularly testing new detection techniques, and providing feedback to continue evolving their process with the changes that continue to occur in the threat landscape.
5. Lack of validation
This might be the most painful challenge of all: most organizations don’t know if their security controls actually work until they fail.
You’ve deployed firewalls, EDR, and a SIEM, each configured in line with best practices. But has anyone actually tried to break in? Has anyone tested whether that carefully tuned detection rule triggers when it should? Has anyone verified that the patch you deployed last month didn’t get rolled back by an automatic update?
Without validation, you’re operating on faith. And faith is not a security strategy.
What are the types of threat management?

The methods and models for threat management can vary by company. Depending on your business’s security maturity, size, and industry, many different ways exist to maintain threat management.
Familiarizing yourself with threat management types allows you to establish what you already have in place and what might still require additional intervention.
1. Unified threat management (UTM)
UTM utilizes multiple security processes within one appliance or software solution. Examples include a firewall, intrusion detection and prevention, antivirus, as well as Virtual Private Network (VPN) capabilities, all included in one product.
Minor and medium-sized companies favour UTM, needing wide-ranging protection, but do not want the headache of having dozens of disparate tools to manage. The downside is that convenience sometimes results in not having the vast depth that you could achieve by using separate tools.
2. Managed detection and response (MDR)
MDR consists of an external service that provides organizations with access to external experts who monitor the entire environment and investigate threats/all alerts on behalf of the organization, following up with appropriate response action to any identified threat.
This service is suitable for organizations that do not have enough available internal staff or lack experience in their organization to run a 24/7 security operations center.
This approach provides access to external expert security resources who will also have access to threat intelligence, have state-of-the-art tools, and have many years of experience working in security operations.
3. Extended detection and response (XDR)
XDR is an emerging integrated solution that removes the silos between endpoint, network, email, and cloud detection. Also, it provides a consolidated view with related alerts tied to the automatic responses. The XDR model is not necessarily the purchase of one product, but rather stitching the telemetry you have across your entire digital estate.
4. Security information and event management (SIEM)
SIEM has existed for many years now. Its primary function is to collect and aggregate log data from all of your environments, normalizing that data in one central location, and applying correlation rules to the aggregated data in an effort to identify suspicious behavior.
More recently, the cutting-edge SIEM solutions are leveraging machine learning and user behavior analytics to identify anomalous activity that traditional rule-based detection systems are missing. SIEM is a very powerful tool, but it also needs to be finely tuned and managed by skilled analysts.
5. Security orchestration, automation, and response (SOAR)
SOAR platforms assist security teams in handling the shambles caused by alerts, investigations, and responses. They assist in automating routine tasks, coordinating actions across multiple tools through playbooks, and tracking incidents for case management purposes.
You can think of SOAR as sitting on top of your detection tools, but providing the productivity the system needs to get the most out of each tool.
6. Vulnerability management
Vulnerability Management (VM) is different from threat management but is closely related to it. VM is a program that identifies, classifies, prioritizes, and remediates weaknesses in systems before an attacker can take advantage of them.
VM modern programs are integrated with threat intel and prioritize weaknesses based on known active exploitation from the internet.
7. Next-generation intrusion prevention systems (NGIPS)
Traditional IPS systems use signatures to protect against known attacks with little ability to detect unknown attacks.
Because they use behavioral analysis, threat intelligence, and context awareness, NGIPS can detect and stop attacks that are unreleased, never-before-seen, and/or evasive.
This means you can use them to identify and stop attacks before they occur, as opposed to relying heavily on continuous updating of signatures to protect against known attacks.
8. Advanced malware protection (AMP)
Advanced malware protection (AMP) provides more than just the traditional antivirus signature-based protection by including additional defense against fileless malware, zero-day exploits, and polymorphic malware.
It uses sandbox, machine learning, and retrospective analysis to detect and block all three of these forms of malicious software from your organization.
If a file that has been identified later demonstrates malicious behavior, AMP will reverse any actions the system took based on that file across your entire enterprise. There are plenty of cloud antivirus options you can consider to secure your cloud.
9. Next-generation firewalls (NGFW)
NGFWs have similar capabilities to traditional firewalls, but offer a feature set to support application awareness and intrusion prevention/threat intelligence as well.
NGFWs not only look at ports/protocols for protection, but also read and analyze the actual data being sent through the system using many different mechanisms to identify potentially dangerous applications and block their potentially dangerous data, regardless of the port that transmitted it. We have a detailed roundup on the top free firewall software that you can read if you need.
Differentiating between a threat, risk, and vulnerability?
These three terms get thrown around interchangeably in casual security conversations. They shouldn’t be. Understanding the distinction is fundamental to thinking clearly about cyber threat management.
Threat: The bad guys
A threat is the possible occurrence of an event that could cause you harm from a source that can do so. It may come from an outside source (malicious hacker, malware, and ransomware), or from an employee’s error in configuration (e.g., putting an instance of cloud computing into production without permissions), or from an environmental source (power failures, flooding, etc.).
When you hear news about a new ransomware group targeting health care organizations, you are hearing about threats. In one sense, threats are the people and things that can cause you harm.
Vulnerabilities: The bad doors and windows
Vulnerabilities are essentially the weaknesses present in your systems, processes, and controls that an external threat could exploit.
Examples of vulnerabilities include unpatched software errors, weak password policies, open ports on a cloud portal, and even gaps in employee training with respect to security awareness. Vulnerabilities exist ‘inside’ your organization. They are the doors and windows that bad guys are waiting to find and exploit.
If you want to upgrade your password policies, read our guide on how to create strong and unique password.
Risk: The place of the outcome
This is the combination of threat, vulnerability, and consequence (impact). It is the potential for loss or harm when a threat exploits a vulnerability.
You must not only understand that there is a threat (ransomware), a vulnerability (unpatched servers), but you must also understand the scope of the potential impact should both the threat and vulnerability combine and successfully exploit the vulnerability.
Does that server hold patient records? Customer payment data? Trade secrets? The answer determines the risk level.
A simple way to remember it:
| Term | Definition | Example |
|---|---|---|
| Threat | Something that could harm you | A hacker group known for targeting banks |
| Vulnerability | A weakness you have | An unpatched vulnerability in your internet-facing banking app |
| Risk | The potential damage if a threat meets a vulnerability | Customers’ financial data was stolen, regulatory fines were imposed, and reputational damage was inflicted |
You cannot eliminate all threats. You cannot patch every vulnerability. But you can manage risk by understanding which threat-vulnerability combinations pose the greatest danger to your most critical operations. This is what cyber threat management is ultimately about.
Best approaches to effective cyber threat management
In cyber threat management, it’s one thing to understand what it is and how it works, its another thing to develop the ability to successfully perform the function.
Mature organizations always utilize the best practices that are proven to be successful to distinguish effective programs from those simply going through the motions. (Read our detailed guide and extensive tips on how to keep yourself safe from cyber attacks.)
1. Establish understandable threat visibility
It is impossible to defend against what you cannot see. Therefore, it seems to stand to reason that many organizations learn about unsecured databases, numerous clouds left on the network, or shadow IT apps, only after a breach occurs.
Comprehensive visibility to threats means having an accurate representation of the full digital footprint and not just your official company network (on-premise network), but your cloud environments, remote endpoints, mobile devices, connections to IoTs, and all 3rd party integrations.
You need to have a complete understanding of everything connected to your network: how/when they are connected; who has access to them; and what is considered normal behavior related to each of them. Without the above foundational items, everything else will be performed on assumptions and guesses.
2. Integrate threat intelligence feeds
Internal telemetry provides insight into your organization’s activities. While, threat intelligence provides insight into what is happening globally. Effective security programs combine the internal data from your systems, applications, and users with the curated external intelligence from reputable threat intelligence sources.
These may include industry-specific threat feeds, open-source intelligence (OSINT), government-specific advisories (such as CISA advisories), and other commercial threat intelligence services. (Read this article to explore the top OSINT tools for cyber investigations.)
The critical part is how well these are integrated—not simply by compiling them into one place, but also by infusing them into your security information and event management (SIEM) or security analysis platforms so you can enrich the alerts your systems generate with context from the real world.
For example, a suspicious IP address of malicious activity may carry more meaning when you evaluate its current association with an active ransomware attack.
3. Prioritize based on business impact
It is not necessary for all types of threats or for all different types of assets to have the same impact. A critical vulnerability on your customers’ ability to make a payment via your website would qualify as an emergency or serious issue, whereas a vulnerability on a marketing microsite nobody accesses any longer would not be considered to be a serious issue.
Frameworks designed according to risk allows your security team to specifically focus their efforts on those items that will have an impact upon business operations (i.e., what systems are most critical to the business from a business standpoint, what type of data resides on those systems, and how an incident will impact those systems financially).
These frameworks shifts the focus away from “how many vulnerabilities do we have?” to “which vulnerabilities should we be more worried about right now?”
4. Automate detection and response
Security teams receive countless alerts. Alarms are continually going off, with both false alerts and real alerts being lost in the chaos of false ones. There are not enough hours or people available to have an analyst investigate every alert manually.
Automation is the only way to scale security detection capabilities. Products like SOAR (Security Orchestration, Automation, & Response), XDR, or BAS are capable of performing the majority of the normal detection, triaging, and response actions without needing a human to assist them.
This doesn’t mean that they will take the place of security analysts but will enable them to spend their time focusing on the more complicated investigations and the strategic improvement of their security program through automation.
5. Test incident response regularly
Having a formal written plan in place means nothing until you are able to demonstrate that the plan works. Periodic testing of the plan is essential so you can identify any gaps that may exist in it before you have a real attack.
This periodic testing may include different types of tabletop exercises, red team and blue team simulations, and purple team exercises, that can identify gaps in your incident response plan before a real attack occurs.
Periodic testing does not need to be elaborate or time-consuming but is a most effective approach to identify potential weaknesses in your plan.
For example, holding a two-hour discussion with key individuals to work through a hypothetical ransomware crisis situation will likely uncover unclear roles, missing contacts, incorrect contact information and/or out-of-date procedures. The goal is to continually improve the incident response plan as opposed to developing a “perfect” plan.
6. Continuously validate security controls
This last practice is where most organizations fail. They purchase tools, set them up, and assume that they are actually operating properly. However, they have no way of knowing with certainty if their firewall rules actually block the most recent evasion techniques or if their EDR actually detects a brand new strain of malware.
Continuous validation takes care of this issue. Rather than hoping that the defenses are working, you actually test them with real-life attack scenarios.
Continuous validation is the real difference between traditional cyber threat management and what we are about to discuss as the next phase of evolution of cyber threat management.
FAQs
No, there are differences. Cyber threat management encompasses a wide range of security tasks, including threat identification, threat intelligence tracking, threat response, and threat validation. However, vulnerability management is limited in scope to scanning for and remediating weaknesses or lapses in systems, hardware, and software. It represents an important component of the broader cyber threat management process.
At a minimum, once per year. However, organizations with more developed incident response processes test their plans every quarter; some even conduct ongoing tabletop exercises as part of their threat validation processes. In addition to frequency, the quality of the test results is crucial to determining what gaps exist between your actual response capabilities and what your organization has identified to be the desired level of performance as defined in your playbooks.
Many tools support the various processes associated with creating and implementing an effective cyber threat management program. Although a typical organization will use a combination of several different tools, the most common tools include: SIEMs, EDR/XDRs, threat intelligence platforms, and increasingly, breach (theft) and attack simulation tools. Because of the varying sizes, industries, and infrastructures of all businesses, there is no “standard” combination of threat management tools that will work well for each organization.
Employment in CTM continues to be very strong, as the expanding global risk of cyberattacks and the shortage of skilled professionals capable of providing protection and remediation from these attacks will mean high demand for individuals in CTM positions. Examples of positions available in CTM include: SOC manager, security analyst, and incident response analyst; threat hunting analyst, and threat intelligence analyst. A market analysis of data collected from various sources indicates that the majority of CTM positions pay well and are very stable.
