Amidst the growing content censorship and geo-restrictions, VPN services have gained significant popularity among internet users. However, changing online locations also means that the users should surrender their access to local content, something infeasible for many. That’s where split tunneling helps VPN users manage their browsing requirements.
But do you need split tunneling for your traffic? Is there any risk involved in this? Which VPN vendors will let you do it?
Read along to find the answers to all these questions and the information you need to do split tunneling work for you.
Our short final analysis if you’re in a rush right now
Split tunneling is not the best way to go if you are serious about anonymity, security, and privacy. But it’s an incredible feature if all you need is protection on some apps and services you use without compromising your overall speeds and loading times. If that’s you, NordVPN is the best split-tunneling VPN you can give a try!
Split tunneling: How does it work?
Split tunneling is an intelligent VPN tool that grants you much more control over your traffic. With this feature, you can choose which data goes through your regular channels, which are faster but unencrypted, and which traffic must be secured by your VPN’s encryption and IP masking capabilities.
So, how does split tunneling work? To understand this phenomenon, let’s first look at how a VPN server works at the primary level.
Your regular ISP service gives you a direct connection to the internet. All your traffic, incoming or outgoing, goes through that connection. Then, adding a VPN to the mix establishes a secure tunnel between your device and a VPN server before reaching the internet.
This way, you don’t surf the internet directly, but the VPN server does. The data transmitted from your device first passes through the VPN server that encrypts it and assigns its own IP address to your traffic. Consequently, the outside world won’t know your IP address — instead, they see the server’s IP as yours.
This encryption makes it impossible for any third party to track your activities. That’s because, without the decryption key, everything looks like white noise to them. Also, any external observer would find your online traffic transmitting through a single node in the net.
Because when you’re using a VPN, everything needs encryption on your device and then decryption on the VPN server, and all your data is routed through a single server, using a Virtual Private Network (VPN) costs you a little in terms of connection speeds. Still, it often is something you won’t notice regarding functionality.
So, until now, everything you do goes to the internet through a single connection, whether your ISP’s regular one or your VPN’s server. Here’s where split tunneling comes in: it opens two simultaneous connections to the internet. In this way, you can choose which online activities are sensitive enough to get VPN protection, while you can have the rest of your traffic for your regular ISP connection, so it doesn’t slow down your other activities.
Flavors of VPN split tunneling
The principle for deploying split tunneling is quite simple. But when it comes down to implementation, the devil is in the details, as there are several ways to achieve the same goal. Here are the most frequent types of split tunneling:
- URL-based: This mode is usually available when you use your VPN’s browser extension. This option lets you choose which URLs you want to be encrypted and which remain open.
- App-based: Here, you’d choose the applications in your device or operating system whose traffic you want to be VPN-protected. Everything else goes through your regular channel, that is, your ISP.
- Inverse (or Inversive): In this mode, your internet traffic passes through your VPN unless you specify otherwise. In simple words, with inverse split tunneling (also known as “split-exclude”), you choose which apps should not use your VPN connection.
- Device-based: This type of split tunneling is typically available with router VPN clients. It allows you to configure your router VPN to allow specific devices to bypass or use a VPN tunnel. It is similar to app-based split tunneling but works at the device level. For example, you can specify your PC always to use a VPN and/or your mobile phone to bypass encrypted traffic.
Split tunneling and security: How secure is this feature?

VPN split tunneling can’t possibly be as secure as sending all your traffic through your VPN server. However, if you set everything up correctly, know what you’re doing, and ensure that all the data that goes through your open connection is not sensitive, then split tunneling could give you the right balance between security and functionality.
And while split tunneling can’t ever be as secure as the full VPN connection, it remains better than not having any VPN protection. So, yes, split your internet usage if you must. But, be wise. Any data you need to keep private or that are too sensitive should not remain on the open connection.
But this doesn’t mean split tunneling is insecure at all. Although, some people defend the idea that split tunneling brings down the strength of the encryption in your overall connection. Yet, this notion is utterly baseless and depicts a lack of understanding of cryptography.
Split tunneling: The pros and cons
Regarding security, any measure you take comes with advantages and disadvantages. Split tunneling is no exception.
Here is a quick look at why, or why not, you should consider using split tunneling if your VPN offers it.
The advantages of split tunneling
Save bandwidth
Split tunneling will redirect traffic encrypted and potentially slow down by the VPN through a separate tunnel. This will improve transmission speeds. Since no encryption is necessary, routing traffic through a public network can improve performance.
Secure connection for remote workers
A VPN enables remote employees to access sensitive files and emails securely. At the same time, they can use the split tunneling feature to access other internet resources at higher speeds.
Work on Local-Area-Network (LAN)
The VPN encryption may prevent you from accessing your LAN. However, with the split tunneling feature, you can access local resources like printers through LAN while enjoying VPN protection.
Stream content without needing a foreign IP address
Enjoy geo-blocked content and access web services that require a local IP address. For example, you can stream content in your home country while abroad. You can also use the split tunneling feature to access websites and services that require a local IP address, like banks.
The disadvantages of split tunneling
The main reason to avoid split tunneling is security. It obviously can’t be as safe as having all your traffic routed through the VPN.
Leaving part of your internet traffic unencrypted somehow risks your privacy, leaving you vulnerable to traffic interception, online tracking, and other threats.
Nonetheless, you can significantly alleviate these issues by applying safe browsing practices and securing your device(s) secure with a robust antivirus.
The risks of split tunneling
Ironically, every security measure you can implement implies accepting some risks. But that’s the way of digital technology, and it applies to split tunneling as well. Below are some of the common risks associated with using this feature.
- Bypassing security measures: Also include proxy servers, which help keep your traffic safe.
- Completeness. If you go with split tunneling, you have to set everything up all the way or not touch it at all. If you leave any loose ends hanging, any hacker worth it is salt will have a field day with your traffic.
- Risking corporate security: If any of your staff members or colleagues at your workplace uses an insecure network, that could be the weakest link in the chain, putting the whole business system in danger.
- It empowers users against corporate or academic permissions: Your company or your school has a policy about sites workers should not access or downloads that shouldn’t occur within the network. The split tunneling connection allows users in your network to do whatever they want, as if they were not inside your network, through the VPN connection, while their traffic in the open part of the traffic will look normal.
- Corporate IT becomes blind: Your IT people won’t know if one of the company’s employees wastes his working time on forbidden sites or uses risky networks.
So, as you can see now, VPNs are all about empowering end-users. But if you are those users’ employers, how powerful do you want them to be?
When to use split tunneling
Split tunneling’s primary use case is to protect your most sensitive data without losing too much of your internet speed. If you know the data you must keep private and you’re willing to take the time to set up your connection correctly, split tunneling will be an excellent feature for your user experience.
Split tunneling can be exceedingly helpful in many scenarios; here are some of them:
- Enhancing security without compromising transfer speeds: Every internet user loves to browse at high speeds while having their online activities protected without sacrificing functionality. Not every action you perform on the internet requires the same degree of security. Online banking, email exchanges, and transferring confidential files need the utmost care. But for other activities, like browsing the web for news or other relatively trivial things, you would probably be okay with giving up the basic security fast speeds. That’s where VPN split tunneling might facilitate you.
- Connecting to your LAN (Local Area Network): Your LAN is where you perform your daily work, so you need unfettered access. But, when using VPNs, you remain outside your LAN because your local server will consider you’re not in the right physical place. Here, split tunneling helps you choose which apps should use your LAN’s resources while allowing the rest to go to the broader internet, but securely.
- Being abroad: Living overseas has always been a tricky thing. While it’s a cliché that the internet knows no borders, every website tracks users’ physical locations. Many are programmed to accept connections only from a limited zone or offer different content to users from other countries. Countries like China and Saudi Arabia are notorious for the blockages they inflict on their internet users. But even Netflix won’t show a Brazilian user the same catalog of videos it will show to a US-based client. So, while the Internet is not a real-estate business, the location remains a crucial variable in many instances. A VPN connection will show you as a user connecting from elsewhere in the world, depending on the server you choose. In that way, you can use the encrypted portion of your data flow to enjoy many activities unavailable to the rest of the users in your local network or jurisdiction. That too, without sacrificing the functionality you need from your local resources.
How to use split tunneling
Setting up split tunneling depends on the VPN you choose. Nonetheless, there is a general procedure that applies to most cases:
- Open your VPN app and sign in.
- Find the split tunneling setting in your app’s menu before you connect.
- Add all the apps you want to be protected by the VPN servers. If your provider uses inverse split tunneling, choose the ones you don’t want to cover.
- Ensure that split tunneling is enabled.
- Connect to the VPN.
Full tunnel vs. split tunnel: What is the difference?
If you are in full tunnel mode, every single byte of your incoming and outgoing traffic goes through your VPN server.
In contrast, according to your setup, the split tunnel allows some of your data to reach the internet through your regular ISP’s open connection.
It explains that complete tunnel connections are safer because they encrypt all of your traffic instead of a fraction. Yes, that extra security comes at the price of slower speeds when using a VPN, but it’s safer nonetheless.
How to choose a VPN that offers split tunneling
Here are some measures to check out when choosing a VPN with a split tunneling feature.
Browser vs. apps split tunneling
You can use a VPN through its app or a browser extension. The former encrypts all the internet communication on the device, while the latter only secures communication through the browser.
Split tunneling works the same. The split tunneling settings on an app affect the whole device, while the split tunneling settings on a browser affect only the browser.
URL/Domain exclusion vs. Per-app settings
A VPN that excludes websites and specific apps from the VPN tunnel is desirable, but not all VPNs work like this. Some VPNs let you exclude only website URLs, while others only apps.
The first option is per-app settings. It offers a list of all the apps on your device when configuring the split tunneling feature. This is where you choose which apps to bypass the VPN tunnel.
Note: Per-app split tunneling is popular on Android devices, while Windows split tunneling excludes websites and apps.
With the second option, you must manually input the website URLs you want to exclude. This method is desirable if your VPN doesn’t support restricting websites and apps, although it can be tedious. While removing a specific application directly is impossible, you can input the matching service URL. For instance, if you want to exclude the X app from the VPN tunnel, you can type ‘www.twitter.com,’ and the VPN will no longer reroute the app.
Split tunneling on some operating systems
While most VPNs offer split tunneling, your operating system will determine whether you will enjoy it. For example, split tunneling is not viable for iOS devices because of their closed-off nature. Initially, macOS allowed split tunneling, but macOS 11 (Big Sur) or newer versions don’t support it.
Therefore, even if a VPN offers split tunneling, check whether your device supports the feature.
Best VPNs for split tunneling
Many of the best VPN vendors support split tunneling connections. Here are some of those finalized after thorough tests and research.
1. NordVPN
You can manage NordVPN’s split tunneling through a Google Chrome or Mozilla Firefox browser extension. This makes it easy to pick the URLs you want to be encrypted.
2. ExpressVPN
ExpressVPN is one of the best VPNs, but it shines particularly brightly in the split tunneling arena. It’s available in Windows, macOS, and Android. You can set it up on your WiFi router as well.
The configuration is on a per-app basis. This feature keeps things very simple for most users, but if you’re working from a computer, for the most part, you could find that it’s not so helpful.
3. Surfshark
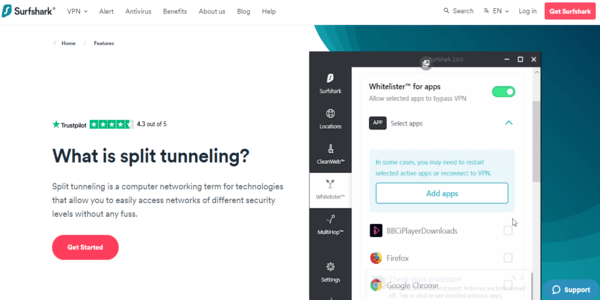
The Surfshark feature is effortless to use, and it’s versatile because it admits both per-app and per-URL setups. The one drawback with this network is that the option is available only in Windows and Android apps.
FAQs
Dynamic split tunneling is a technique that increases functionality in split tunneling by setting it up for Domain Name System. This somehow automates choosing the URLs whose traffic remains open or goes through the tunnel.
No. When you use split-tunneling to bypass certain apps or websites, you get faster connectivity as the traffic involves no encryption, hence, no ping or latency. However, in the case of apps restricted to using VPN, you might experience some latency due to the underlying encryption. Yet, if you use a robust VPN service provider, you won’t face any lags.
Turning off split tunneling works the same way as enabling it. Go to your VPN app’s settings, find the split tunneling feature, and toggle it off.
Technically yes; practically, it depends on your service provider. For example, some VPN services, such as Surfshark, allow split tunneling at the website or IP level (called “Whitelister”). Whereas NordVPN only supports split tunneling for apps and not for websites or IP addresses.
No. Every VPN protocol supports split tunneling, so there are no limitations. Nonetheless, make sure to use secure VPN protocols only (such as OpenVPN) for better privacy.
Unfortunately, split tunneling isn’t available on iOS devices with consumer VPN services. Apple calls this feature ‘per app VPN,’ but it is only available on apps managed with a mobile device management (MDM) solution. Companies use MDM solutions to manage and control employee devices. So, you need to install MDM software to use a split tunneling on iOS.
Like iOS, macOS 11 does not support split tunneling. A recent operating system update removed split tunneling, disenfranchising many VPN providers. Fortunately, some VPNs, like Private Internet Access (PIA) and Hide.me have updated their apps to support split tunneling on macOS 11.

