A dark web monitoring API has become essential as cyber threats grow more advanced and shift into hidden corners of the internet. Today, sensitive data like passwords, emails, and company databases are frequently traded in secret marketplaces and underground forums.
Manually tracking these threats is nearly impossible. That’s where a dark web monitoring API comes in. It automatically detects exposed data and alerts organizations in real time, helping them respond before serious damage occurs.
But the question is what it actually does and how it works. This article explains what a dark web monitoring API is, how it works, and why it’s critical for protecting your business in today’s digital landscape.
What is a dark web monitoring API?
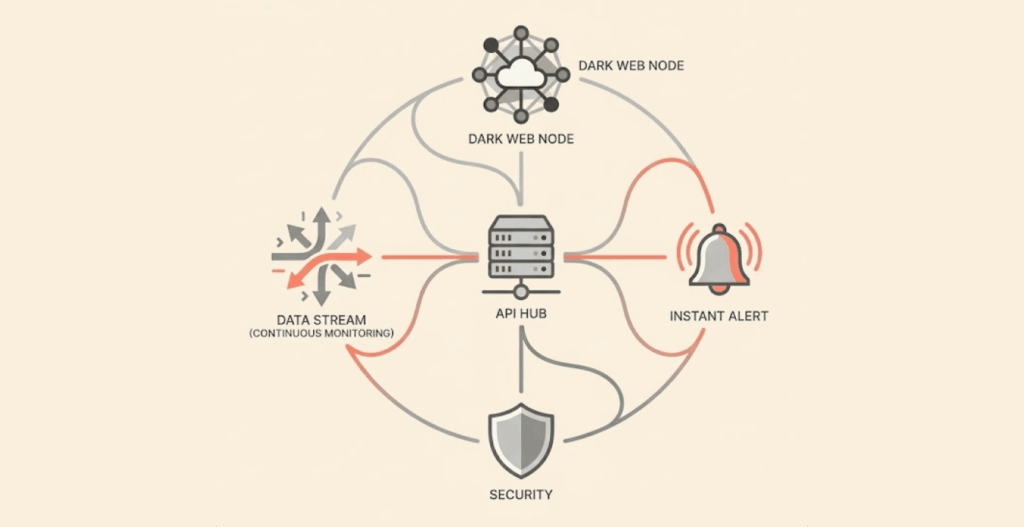
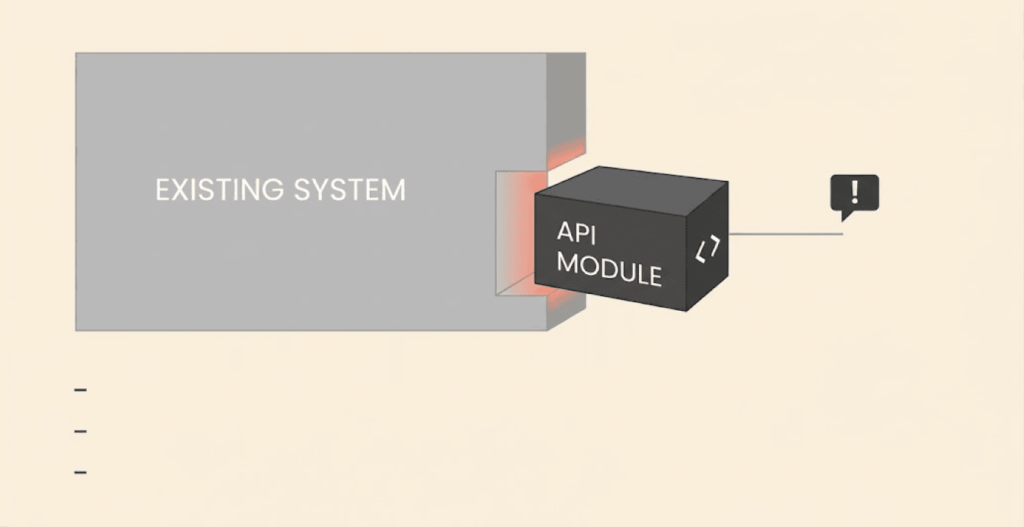
A dark web (the hidden and shady part of the internet) monitoring API is a tool that automatically scans the dark web for exposed sensitive data such as emails, passwords, or business information. Instead of manually searching hidden sites, it connects to monitoring systems that continuously track data leaks.
It works as an early warning system. When compromised data is found, the API sends alerts so users or businesses can act quickly, like securing accounts or resetting credentials.
The main advantage is automation. It can be integrated into apps, platforms, or security systems, allowing real-time monitoring without manual effort. Many APIs also provide details about where the data was found and how serious the risk is, helping organizations respond effectively and stay protected. If you have found your data on the dark web and don’t know what to do, read our guide on what to do if you see your data on the dark net.
Why should a business invest in dark web monitoring APIs

Digital threats are not dwindling; instead, they keep evolving as technology advances further on a daily basis. This continuous growth gives cyber criminals more arsenal to carry out digital thievery and exploitation.
This is why businesses and organizations need to stay on their game to get alerts on potential threats and attacks stemming from exposed data, which eventually culminate in phishing kits or Ransomware-as-a-service.
This is why dark web monitoring for business has become essential so that perpetrators of digital exploits won’t get a field day. Some of the reasons businesses should invest now in Dark Web Monitoring API include:
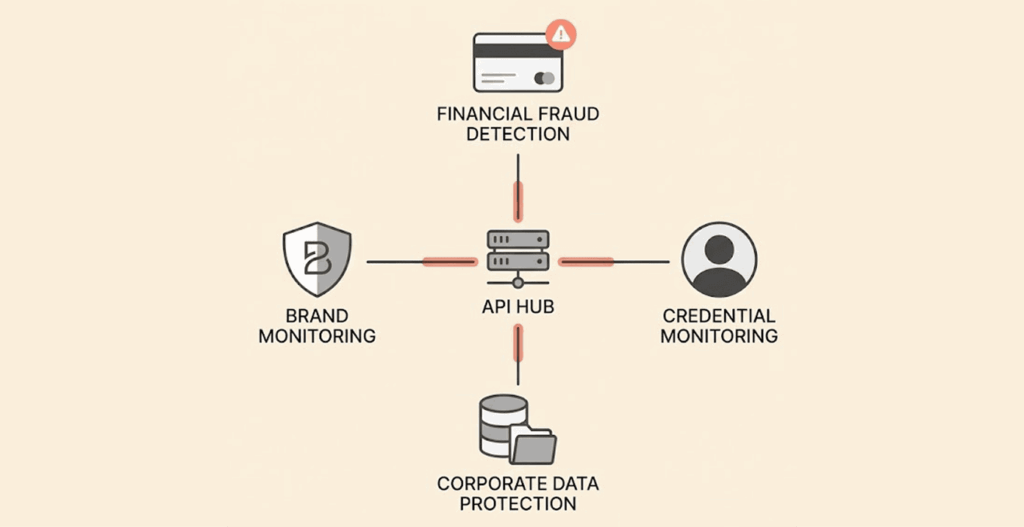
Detection of compromised data
If a dark web monitoring API is part of an organization’s security solution, it will be easy for the teams to quickly know when the company’s credentials, customer data API keys, etc., have entered the den of digital thieves.
This could take place some weeks before any attack could take place, giving them enough time to mitigate against such attempts.
Centralized monitoring
If a business includes dark web alerts in its automation tools, dashboards, and SIEMs (Security Information & Event Management), it can monitor the dark web comprehensively and also react faster in real-time.
Advanced threat intelligence
Security teams don’t have time to scan for threats manually. In fact, with dark web monitoring APIs, they can understand emerging tools, tactics, and even compromised assets.
For instance, it will be easier to get an early knowledge of new TTPs and phishing kits to prevent falling victim to them.
Here’s something most security professionals will tell you: when you’re actively monitoring dark web sources, you also need to protect your own digital footprint. Accessing these spaces without a VPN leaves you exposed. We’ve tested and ranked the top VPNs for dark web access so your research stays private and your identity stays hidden.
Reduction in operational and financial risks
If a business gains early insight that threat actors are planning an attack, it can take proactive steps to stop it before any real damage occurs. This kind of early warning can prevent serious operational disruptions and protect the company from potential financial losses.
Beyond that, stopping an attack in advance also helps avoid regulatory penalties that often follow data breaches. Compliance violations can be costly, both financially and reputationally. And it’s not just about fines; there are additional expenses to consider, such as compensating affected customers, managing public trust, and repairing compromised systems.
In short, early detection doesn’t just reduce risk; it saves businesses from a chain reaction of costly consequences.
Compliance and due diligence
There are laws governing the use of data online, and they come with many different requirements based on jurisdiction. Any business that takes dark web monitoring seriously will show its preparedness to meet both cybersecurity standards and data protection laws.
Protection of the brand and its reputation
When users’ data keeps leaking from business systems into the coffers of cybercriminals who peddle them on shady places such as dark web marketplaces, customers, investors, shareholders, and even the government will lose confidence in them.
This is why early threat detection and mitigation, which a dark web monitoring API can provide, becomes compulsory.
Key features of a strong dark web monitoring API
A robust API must have a broad coverage of the dark web sites and activities, produce timely insights into what’s happening around your business, and also come in a ready-to-integrate package.
So, when considering utilizing dark web monitoring for business, there are some features you must confirm to be sure that it meets your needs. Check them below:
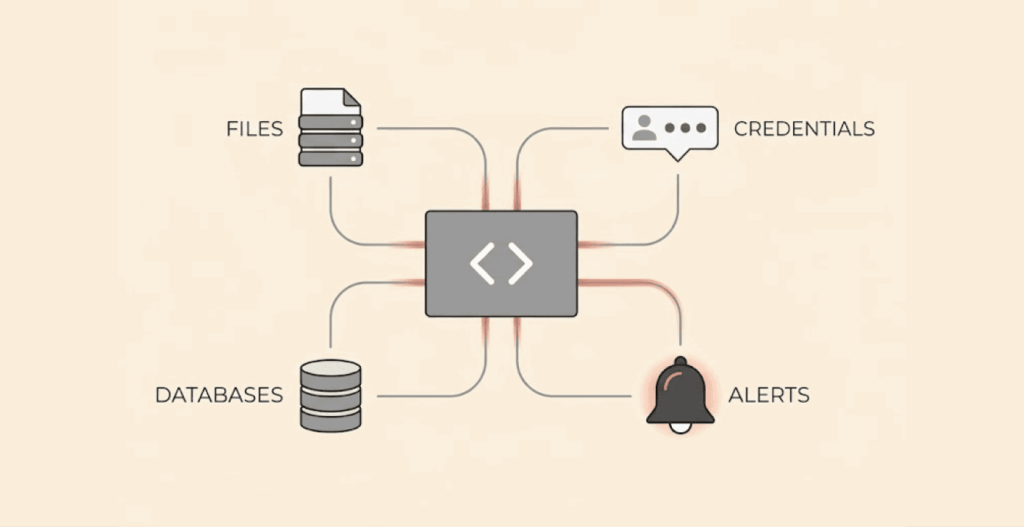
Deep source monitoring
The API must have access to all the places where your company data can appear, such as dark web marketplaces, forums (hidden internet discussion boards), Telegram channels, onion sites, Phishing Kits and Hacking tools repositories, dark web crawlers and indexers, etc.
Real-time alerts
A strong dark web monitoring API must provide notices of compromised data, mentions, and discussions of possible attacks to help a business kick-start its preventive operations against such attacks.
Seamless integration (Developer-friendly)
REST API (Representational State Transfer) design style that uses standard web protocols such as POST, GET, and HTTP, combined with structured responses, must be the standard to ensure that integration is easier and faster because most developers already understand it.
Customizable alerts & filtering
A reliable dark web monitoring API sends alerts based on data types, keywords, geography, and industries based on customizations from the security team. This will allow them to even get only notifications that are relevant to the brand.
Context-rich intelligence
Getting encompassing metadata, such as timestamps, information about the threat actor, source details, exposure level, etc., is another good feature of a strong API, as it will help the team in charge to know which threat needs urgent attention and those that are not urgent.
Secure access and authentication
If the solution offers secure API keys, SSO/SAML support, and even tokens, it will help the security department to control access and even protect the API from cybercriminals that might want to disrupt operations or steal critical company information.
Organized output and export options
It will be of immense assistance to integrate an API that will deliver detailed and well-organized outputs using formats like JSON (JavaScript Object Notation), which allows data to come in a human-readable and text-based format for simpler storage and exchange.
There’s also the CSV (Comma-Separated Values) format that makes it easy for different apps like databases and spreadsheets to exchange data seamlessly.
Real-world use cases of dark web monitoring APIs
Dark web monitoring APIs have become a necessity for companies across different industries, as it assists them in knowing what is happening in the hidden sector of the internet and also respond quickly to the threats that crop up.
Let’s check them sector-wise:
1. Banking and finance services
Dark web monitoring API helps the banks to discover when bad actors have stolen their customers’ credit card details, credentials, and other insider access to stop them from selling such on dark web marketplaces.
With real-time alerts from the API into the company’s fraud detection systems, the teams can immediately lock all compromised accounts and prevent financial theft before it actually occurs.
2. Tech and SaaS companies
Some prominent products that flow into the dark web marketplaces from tech companies are login credentials, proprietary code leaks, API keys, etc. With a dark web monitoring API, these companies can monitor such thefts and carry out quicker remediation, such as revoking the access of bad actors.
3. E-commerce and retail
Companies in the retail industry make use of this solution to discover when digital criminals have taken hold of customer accounts or when their payment information is no longer secure.
Also, they can know when criminals have designed a convincing phishing strategy that appears to be from them to steal from their customers. Alerts help teams act quickly and stop any fraud that might occur and cause their customers to lose trust in them.
4. Healthcare & medical organizations
Healthcare providers make use of Dark Web Monitoring APIs to get notices that hackers have stolen sensitive records, employee credentials, and insurance details belonging to their patients and staff.
By automating the alert of such incidents, security teams can offer faster responses, thereby complying with regulations such as HIPAA (Health Insurance Portability and Accountability Act).
5. Public sector & government agencies
Government agencies count on dark web monitoring to find out when documents, credentials, etc belonging to the public have found their way into hidden markets.
It also enables them to discover that a threat chatter is focusing on hacking into public infrastructure. Such continuous monitoring supports and boosts national & municipal cybersecurity posture.
6. Telecommunications
When it comes to the Telecom industry, the providers depend on APIs to quickly discover actions like SIM swapping or the circulation of data and credentials stolen from subscribers to certain services. This will enable them to intervene and protect accounts that belong to people in sensitive posts.
How a dark web monitoring API works behind the scenes
A dark web monitoring API follows a structure made up of different processes to give the results security teams expect. This is, of course, uncovering threats early, no matter how deep they hide. The process is as follows:
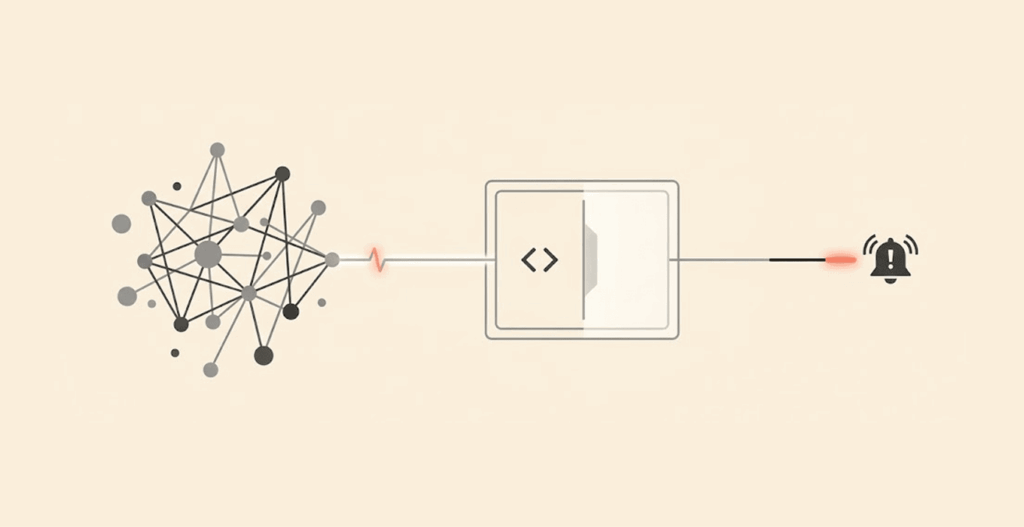
Crawling & collection of data
The API has some special crawlers (bots) that check different dark web sites which the traditional search engines do not index. These sources include but are not limited to marketplaces, channels for encrypted messaging, hidden discussion forums, and leak sites. The aim of crawling is to gather data relating to the company.
Processing
Of course, all the data gathered from diverse sources must be cleaned and arranged, decrypted if locked with encryption codes, filtered, and tagged following the customizations (keywords, geography, region) from the security teams. The aim is to thrash content that is just noise of duplicates that doesn’t relate to the company.
Matching
In this process, the threat intelligence system compares this data, already organized into credentials, domains, email addresses, brand names, and IPs that the business’s security team provided.
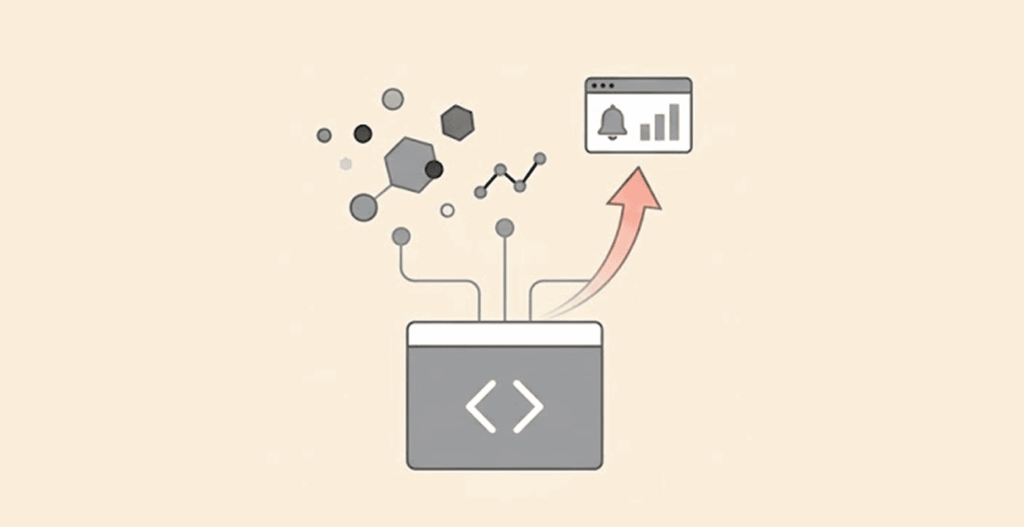
Data ingestion and enrichment
Before sending out alerts, a strong dark web monitoring API, such as PhishFort, describes its solution as one that enriches the dark web signals it collects with WHOIS, DNS, SSL, ML-based classification, and hosting, before sending it for analysis.
That aim is to reduce false positives. Other APIs like Munit.io say it enriches every threat indicator with context like source credibility, links to previous campaigns, or even first-appearance time.
Alerting
This process is to send notices in real time to the security teams through the API, integrations, and webhooks, all in the bid to hasten responses and provide remedies that will deter planned attacks by criminals.
How to integrate the dark web monitoring API into the existing setup
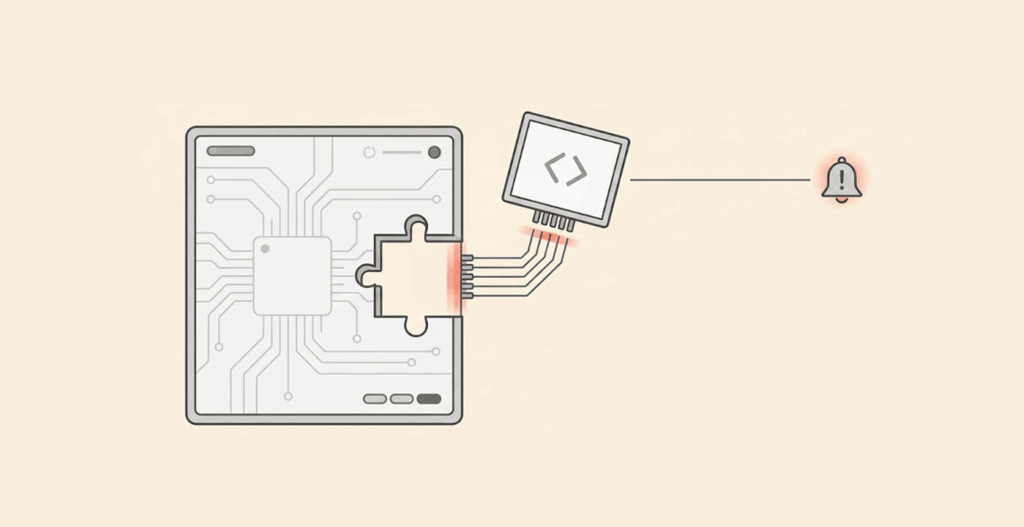
It doesn’t take much to integrate dark web insights into the setup you already have on the ground. All you need is to get the right API, and it’s a go for your team. Let’s look at some of the setups that facilitate this API:
1. Security Information and Event Management (SIEM) Tools
Some of the SIEM tools that make it easy to integrate monitoring API include IBM QRadar and Splunk Enterprise Security. The API can send alerts into the tools for correlation of internal events and logs, thereby allowing the team to detect credential leaks, attack patterns, suspicious logins, etc., as early as possible from a central dashboard.
2. Security orchestration, automation, & response (SOAR) platforms
If a company utilizes SOAR tools like Palo Alto Cortex XSOAR or Splunk SOAR (former Phantom), the alerts from the API will kickstart an automatic response immediately in the form of locking down an account, creating tickets, etc.
3. Cyber Threat Intelligence Platforms (TIPs)
Dark Web Monitoring APIs generate reliable indicators for threat intelligence hubs like Anomali or Recorded Future. Once they receive the indicators, they correlate them to more encompassing threat feeds & campaigns to help the team hunt wider and determine the reach of the exposure.
4. Custom-built security dashboards
If an organization already has an in-house security dashboard that they built with tools such as Sumo Logic or custom ELK/Kinana visualizations, the API can then send data into the already-built dashboards so that the teams will see when the data belonging to the company or its customers appears on the dark markets. They can then act fast without needing to check many systems.
Other tools that enable quick integration of dark web monitoring APIs include:
- Threat Intelligence Platforms (TIPs) Extensions. Some of the platforms that fall within this are the OpenCTI platform, the ThreatConnect platform, or another one called MISP (Malware Information Sharing Platform).
- Incident Response and Case Management Tools. Some available right now are ServiceNow Security Operations or another one, Atlassian Jira Service Management solutions.
- Tools that provide Alerts & support Collaboration are Slack, Microsoft Teams, or PagerDuty platforms.
- Tools for Identity and Access Management (IAM) are platforms like Okta, Azure AD,& Ping Identity systems, which a company can put in place to make API work better.
- Endpoint Detection and Response (EDR) and XDR. Some of these platforms to consider now include CrowdStrike Falcon or even the popular Microsoft Defender XDR.
- Cloud Security Posture Management (CSPM), which has some examples like Palo Alto Prisma Cloud or AWS Security Hub tools.
Differences between existing dark web monitoring APIs and older versions
One of the difficult things developers often battle with is how to make their products able to match the improvements in technology.
That’s why it is not always possible for tools to give you the same output. While some provide users with basic feeds, there are others that offer more in-depth insight, coverage, and enriched context.
So if you compare the older API versions, such as the dark web monitoring Google feature that has been discontinued, with the existing APIs, you’ll discover a wide gap in their output. That’s why some of the top APIs for dark web monitoring in the industry offer the following:
Easy-to-use APIs
Flexible, easy-to-integrate APIs designed to support both small and large environments, no matter whether your team is highly technical or not.
The APIs are simple to integrate into existing systems due to their design, making them a top choice for startups, small and medium businesses, and even large enterprises.
Wider coverage
Ability to monitor border sources which covers both very private communities or even closed ones.
These APIs move past the public forums and market platforms everyone knows into encrypted channels, groups that open for those invited only, and even closed forums.
The aim is to uncover what basic tools can’t even sniff out to ensure early and quick stoppage of attacks.
Prioritizes alerts by impact levels
Top monitoring APIs sieve out the noise and leave the useful findings based on how risky the threat, the sensitivity of the compromised data, and the severity of the impact will be on the company if threat actors succeed.
The aim here is to make sure that the security teams will give fast attention to those threats that shouldn’t be ignored for a minute.
AI-Powered intelligence
The latest APIs now use the benefits of AI, which is the ability to carry out analysis on big data without wasting time.
By that, no matter the amount of data or other findings gathered from many different sources, AI can turn them into useful intelligence within a very short time.
It can help the teams understand the areas that matter most by adding context like credibility, patterns, and relevance to the information.
Comparing dark web monitoring APIs
| Characteristics | API 1 | API 2 | API 3 |
| Integration Flexibility | High | Low | Medium |
| Source Coverage | High | Medium | Low |
| Enriched Context | Yes | No | Yes |
| Real-Time Alerts | Yes | No | Yes |
| Accurate/False Positives | High | Low | Medium |
| Cost Flexibility | High | Low | Medium |
How to use a top dark web monitoring API for best results
It is one thing for a business to get the best monitoring API out there, but without using it appropriately, it won’t get the results expected.
To achieve the best results, there are certain things to do, such as identifying the business risk profile and configuring API alerts to match it. The team should take the following actions:
Monitor key assets diligently
Company assets are based on the level of impact on operations when compromised. Some assets, such as company IP addresses, email domains, sensitive product or project names, and employee credentials, are deadly in the hands of threat actors. So, monitor these assets like a hawk to enable the API to generate relevant data and not noise.
Automate alerts through integration with ticketing systems
The fastest way to tackle incidents faster and more effectively is to make sure that logging and assigning them take place automatically without missing important ones. And the best way to do that is to connect alerts from the dark web to internal ticketing tools.
Differentiate dark web alerts by risk levels
Setting priorities effectively is important to put the team’s efforts to good use. Since some alerts may not be so urgent to drop everything for, filter the alerts and pick out the most urgent in terms of deadliness.
For instance, leaked credentials in the hands of cyberthieves are a ticking bomb, so handle that fast. But discussions and mentions that don’t have any immediate concern can be pushed down the list.
Identify patterns through regular review
Security teams need to review the findings of the dark web monitoring API regularly to understand more about the attack patterns prominent among thieves. Also, they could discover attack trends and tighten their security controls, which is, of course, a proactive move.
Correlating dark web data with sources
Security teams should compare what they get from the dark web with those that came from other sources, such as endpoint tools, feeds around threats, and SIEMs, so that they can understand the context of the threat better. If they can match these findings together, they can confirm threats & take better decisions free from doubts.
Is dark web monitoring against the law? Privacy and compliance concerns
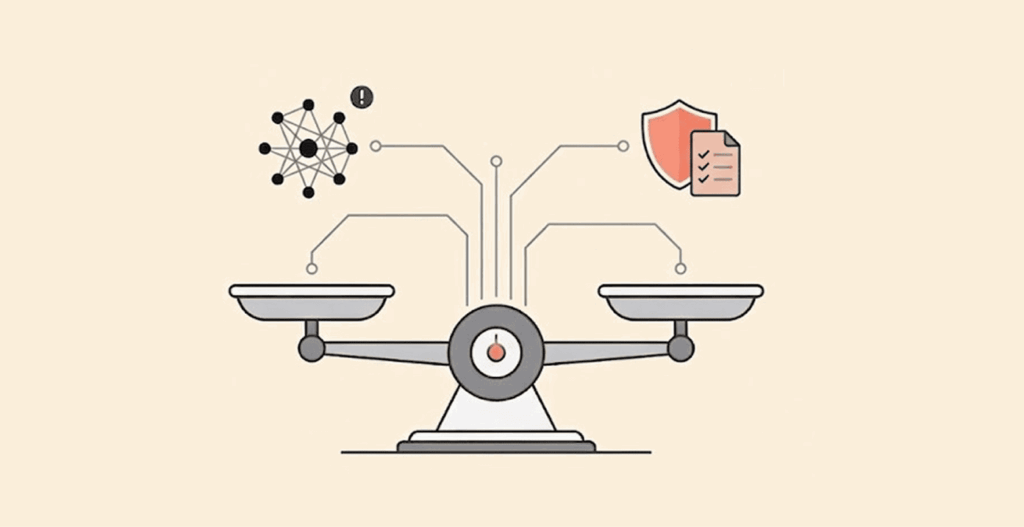
One of the biggest advantages of dark web monitoring is the depth of insight it gives security teams. However, with that power comes responsibility; there are both ethical and legal standards that businesses must follow to avoid creating new risks while trying to prevent others.
To stay on the safe side, companies using a dark web monitoring API should ensure their practices align with data protection laws such as HIPAA, GDPR, and other regional privacy regulations. These laws are designed to protect individuals’ data, and even in security-driven scenarios, organizations must handle sensitive information with care.
The good news is that most regulations do allow monitoring when it serves a legitimate security purpose. Still, teams should follow the principle of data minimization, focusing only on what truly matters. For example, monitoring brand names, corporate domains, or business-related credentials is appropriate, while unnecessary access to unrelated personal data should be avoided.
Many reputable dark web monitoring API providers also build in safeguards like encryption, anonymization, and secure data handling. This reduces the risk of misuse and helps prevent secondary exposure of sensitive information.
So, is dark web monitoring safe? Yes, but only when it is done responsibly and in compliance with applicable laws.
Transparency is another key factor. Businesses should clearly define how data is collected, processed, and used. This becomes even more important when monitoring involves customer or employee data. Access should be limited to authorized personnel, and data retention policies should be clearly defined.
It is also wise to partner with providers that follow ethical data collection practices and comply with legal standards. When combined with internal best practices, this ensures that dark web monitoring remains a secure and valuable part of a company’s cybersecurity strategy.
For organizations that lack in-house expertise, involving legal and compliance teams alongside security professionals can help ensure everything is handled correctly.
What does the future look like for dark web monitoring APIs
As security teams continue their fight against cyber crimes, there will be more need for dark web monitoring because nobody wants to become a victim of bad actors.
As more people need this tool, coupled with the higher techniques and even stronger tools the thieves are using, developers will be working without rest to outsmart them. Here are possible changes to look out for in APIs:
Deeper digging into different platforms
Even though the strong APIs dig deep into various platforms, the future will likely see deeper coverage, especially of those hidden networks, encrypted messaging platforms, invite-only forums, and chat groups that are strictly private.
More utilization of AI and machine learning
AI and machine learning are doing so much already in dark web monitoring as providers use them to make data generation more automatic. Also, AI makes analysis faster and easier, and it makes identifying threats in real-time, such as breeze. The future will see more of this ease and speed in monitoring and preventing cybercrimes.
AI and ML will accelerate the analysis of the voluminous data generated from the dark web and will easily translate the results into insights that teams will work on quickly. By eliminating the possibility of mistakes in analysis, teams can get more accurate alerts, crime patterns, trends, and risk levels within the shortest time possible.
Predictions of threats
Most alerts this time come from APIs through identifying exposures that have already occurred. The future might see the systems carry out predictive analytics to anticipate a possible attack before an exposure occurs. This means that teams will get alerts of threat signals and stop an exposure from ever taking place.
Stronger automation and pre-defined responses
One future improvement in dark web monitoring APIs will likely be more connections with automation structures like SOAR and cloud workflows to help teams lay their hands on pre-defined responses quickly. With that, actions such as tightening access or revoking credentials will happen instantly without any waiting for humans to initiate them.
Richer contextual results
Future intelligence from the dark web will not end in alerts of exposed data; there will be more context to it. How? Correlating threat sources and risk signals with dark web activities will enable the team to understand a threat better, as the alerts will have deeper information to work with instead of just the surface-level ones.
More privacy and compliance-oriented
There are laws on the ground now to protect users’ privacy and also to check companies extracting data and using it to boost operations. But the future will likely see more laws and regulations in the arena.
As a result, dark web monitoring APIs will adopt design principles that focus on a privacy-first approach to make sure their activities comply with existing regulations. This means all activities surrounding the collection of data and usage will be handled responsibly.
More adoption across industries
Right now, many businesses might struggle to incorporate advanced dark web monitoring APIs into their operations due to cost and technical considerations. But in the future, the APIs might be more friendly and cost-effective, enabling all business sizes to access and utilize them.
FAQs
The reason companies monitor the dark web is to know if information that belongs to the company, its workers, or customers has become public. This monitoring enables them to cover loopholes before cybercriminals act.
When there is a dark web alert through the monitoring API, this simply means it has found information that belongs to you or your company on a source. This doesn’t mean your operations have been attacked, but there is a risk that the security team must check out to prevent any attack.
Many countries allow top dark web monitoring service providers to operate freely because these companies act in line with laid-down rules and regulations. This means they don’t overstep nor carry out illegal actions.
Google’s dark web monitoring, which you can get through its Google One service, tells users that their private information, like passwords or emails, is floating on the dark web. This feature is mainly for individuals and doesn’t work like APIs or is advanced enough for businesses to use.
If reputable providers that abide by the dictates of the law handle dark web monitoring, then there’s no issue with it. But if the methods are not complying with legal requirements but instead overstepping, then there’s a violation.
