A new listing where a threat actor claims to sell 12.6 million OnlyFans private lines surfaced on a cybercriminal marketplace.
The post hides key details behind forum engagement. No sample or proof has been released yet.
A closer look at the dark web listing
On May 5, Dark Web Intelligence shared a post about a dark web advertisement. A threat actor is selling what they call an “OnlyFans Private Lines Database.”
The seller markets it as a “12.6M ULP / 100% Private Lines” dataset. They promise “high quality” contact data.
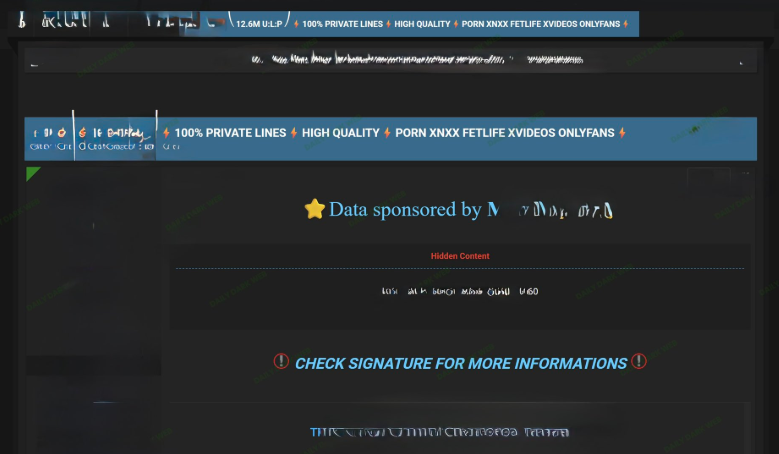
The listing hides the actual content. You must engage with the forum to see it. That is a common gating tactic. It makes the seller look more credible.
Here’s what researchers think from their assessments so far: this is likely a lead-generation or scraped dataset. Or maybe not a fresh breach, but repackaged data from an old breach. Either way, the seller did not disclose the origin. They gave no target platform and no breach method. So we have no way of finding out for sure.
Marketing language points to resold or aggregated data. “Private lines” usually refers to validated contact lists.
Why ‘private lines’ matter for cybercriminals
The term ‘private lines’ may sound alarming, but in reality, it usually just means verified phone numbers and maybe emails. This kind of data is hot cake in cybercrime marketplaces. Scammers can use it for phishing or smishing campaigns.
They can also run spam and fraud operations. If they enrich the data with passwords from other leaks, they may attempt account takeovers. So even if this dataset is recycled, such a vast amount of records (12.6 million) means a lot of targets for attackers.
A massive credential leak from february adds context
Earlier in January, a much bigger report surfaced. A massive breach exposed 149 million login credentials. Those credentials belonged to Instagram, Gmail, and OnlyFans users. Someone left them unsecured in a publicly accessible database.
The leak included 48 million Gmail accounts. 17 million Facebook and 6.5 million Instagram accounts also appeared. OnlyFans contributed roughly 100,000 credentials. Other services like Netflix, Yahoo, and Binance were also hit.
Experts believe infostealer malware collected the data. Unsecured cloud storage made it easy to index. The database stayed online for weeks. Researchers could search it directly.
That breach is not the same as today’s listing. But it shows how often credentials circulate. Attackers can combine older leaks with new “private lines” lists. That makes their campaigns much more effective.
What users should do to stay safe
Scared your data might have been affected? No panicking. But you should take action ASAP. Start by changing your passwords for any adult or subscription platforms. Let the password be unique and hard to guess for all of your accounts, avoid reusing passwords.
Then, turn on multi-factor authentication wherever you can, email, social media, and anything tied to your finances. Third, use a password manager. It stops you from reusing passwords.
Fourth, check your exposure on Have I Been Pwned. Enter your email to see if it appears in known breaches. Fifth, monitor your login history. If you spot any weird logins on devices that are not yours, that’s a red flag.
And public Wi-Fi are a total wild west out there. If you’re connecting at a coffee shop or the airport, fire up your VPN. Seriously, don’t skip this step. It basically scrambles your info so crooks can’t just snag your passwords while you’re logging in from a network not properly secured.
For more detailed steps on keeping your account secure, including privacy settings and anonymity tips, read our full guide on onlyFans privacy here.
The bigger picture: Why scraped data still sells
The dark web markets do not care if a dataset is “fresh.” They care if it works. Even scraped or recycled data can fool people. Many users still reuse passwords across sites.
A phone number from 2021 might still be active. An email from an old breach may still receive spam. That is why this 12.6M listing matters. It may not be a Hollywood-style hack.
But it gives criminals a cheap way to start phishing. And that is often enough to cause real damage. Organizations should also watch for “private lines” terminology. They should monitor for overlapping breach datasets. Strengthening MFA and user awareness blocks most of these attacks.