Many of the widely-used ride-sharing and other travel apps out there have major server-side security vulnerabilities. PrivacySavvy research team discovered a group of travel apps leaving their servers completely open and accessible, ultimately exposing private user data for anyone to see. Most of the apps are leaking data through their subdomains, and the exposed data posed a risk to many parties.
Led by Sarmad khan and Huynh Chen, in first-of-its-kind research, PrivacySavvy tested the security of over 20 of the world’s leading travel apps to understand how they manage users’ privacy and security risks. Unfortunately, most of them failed.
This lack of basic security measures in traveling apps is not only shocking but also shows a total disregard for standard security practices these apps say they carry.
Which travel applications are putting users’ data at risk?
Due to the responsible disclosure principle and NDAs, PrivacySavvy cannot reveal the names of the apps.
Also, as per our knowledge, most companies are yet to fix the reported security flaws. Revealing their names could enable malicious hackers to attack them and leverage their users’ data in no time. All PrivacySavvy wants is to make the internet a safer place for average users without putting anyone at risk in the process.
Millions of users impacted
While we cannot reveal the applications’ names, we can share with you the impact and exposed databases’ secured samples.
PrivacySavvy research team chose all the apps based upon the positive reviews and number of downloads. Apps from individual hotels, airlines, and car rental companies were not evaluated. We mostly tested public ride-sharing and booking apps.
The combined number of downloads for the apps’ in question is a whopping 105 million, as per our calculations. That number could have been even bigger, but fortunately, not all the apps we evaluated had security loopholes.
Example of sensitive data exposure
Sensitive information exposure befalls when a company, application, or other entity unwittingly exposes personal data. Sensitive data exposure is different from a data breach whereby an attacker accesses and steals data.
Private information exposure happens when a database owner fails at adequately protecting a database storing sensitive information. That can be an end result of a multitude of things such as no encryption, weak encryption, software flaws, etc.
Various types of data can get exposed in a sensitive data exposure event, including,
- Credit card numbers
- Banking account numbers
- Session tokens
- Healthcare data
- Social Security number
- Phone numbers
- Dates of birth
- Home address
- User account information such as usernames and passwords
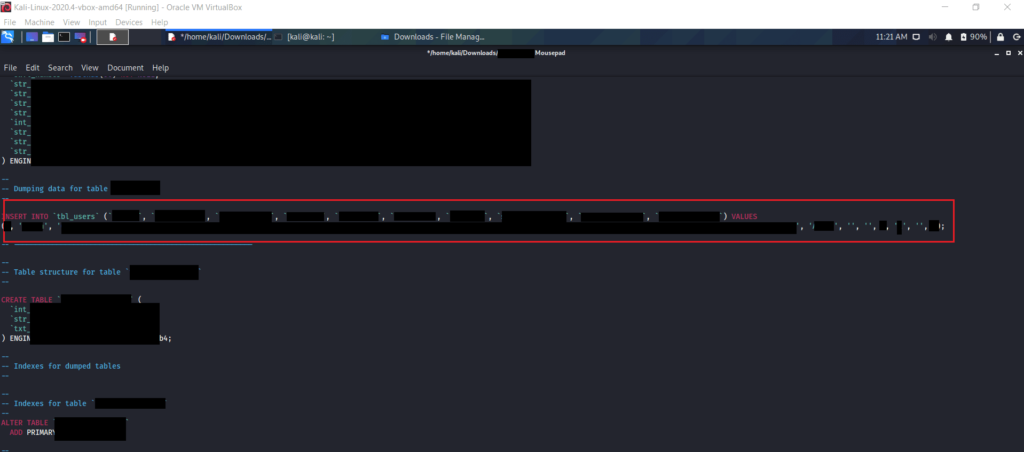
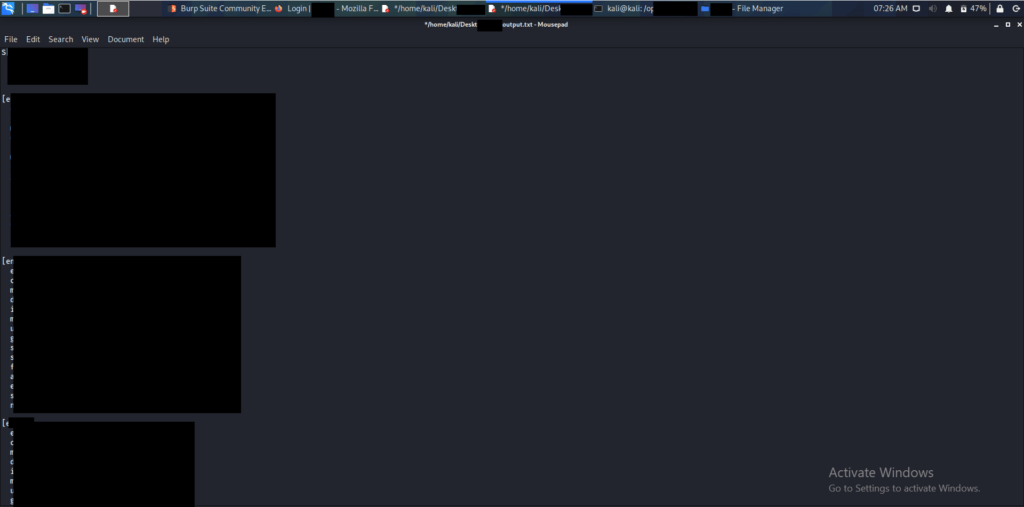
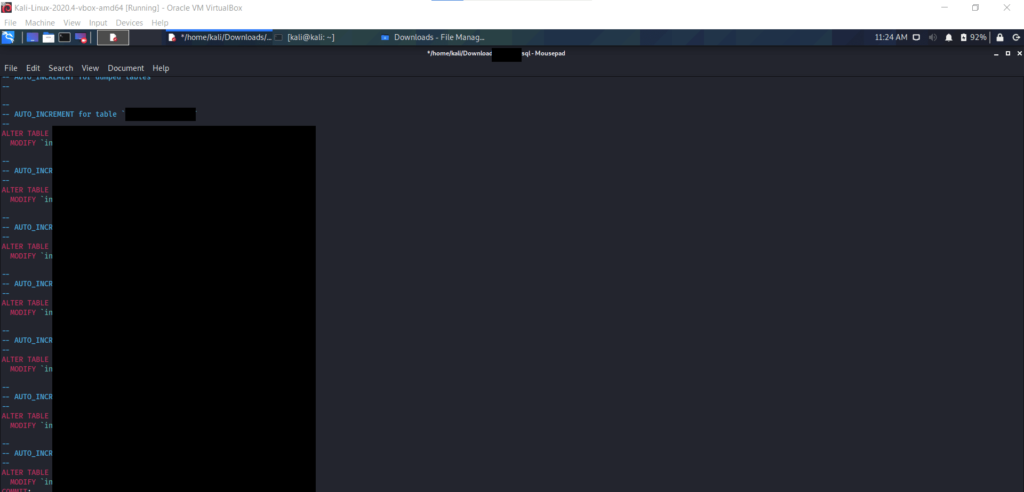
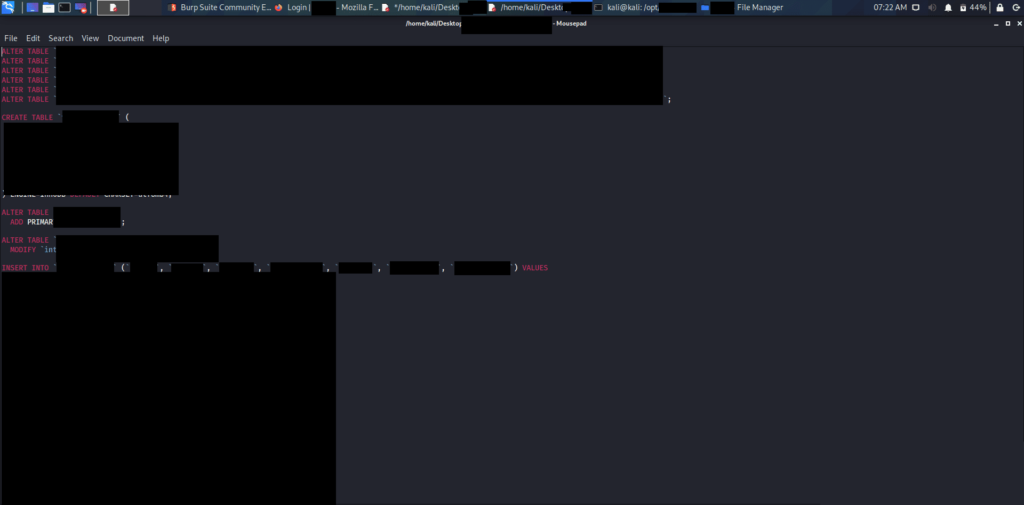
Our research team discovered such sensitive data exposing critical security vulnerabilities in multiple travel apps, mostly in their subdomains i.e. “prcing.ridesharingappname.com.” (Due to NDAs and responsible disclosure principle that we need to follow, we used that assumption domain.) Through those subdomains, an attacker can easily pull the hidden .git directory which reveals the following sensitive information.

Impact
An attacker gaining such information could perform sophisticated attacks with these SQL queries leading to SQL Injection and full compromisation of the database putting thousands of users at risk.
Advice from the experts
For the platforms
The databases’ owners can avoid any such potential sensitive data exposure by merely taking some basic security measures. Before you adopt apps or software to manage any of your business areas, make sure they follow the best practices of data security.
If your business requires you to process external data, such as a ride sharer’s or other members of the public, you must ensure this data is well protected from malicious hackers. Regardless of its size, any company can replicate such issues by:
- Deploying proper access rules.
- Securing not only the the main domain but subdomains as well.
- Never leaving a system that doesn’t demand any authentication open to the internet.
- Not making files containing sensitive data such as .git publicly available alongside making sure never to store them on production servers.
For users
Since we reported the vulnerabilities we found to all the respective companies, chances are you’d be on the safe side soon. But not all companies have acknowledged successful fixes yet. Also, you can never take security for granted these days.
If you’re concerned your data might get compromised, spare some time and contact all or any travel app (such as ride-sharing and flight booking ones) you’ve recently used to inquire about their data security practices. It’s your security, there is no harm in taking charge of it – as a user it’s best for you to question them. Your little step of questioning the apps will help make the internet a safer place for everyone as it will push those platforms to go the extra mile.
It’s also recommended that you head over to our ultimate internet privacy and security guide. It uncovers many ways via which cybercriminals can attack you and your data today and the useful steps you can take to stay safe.
How and why PrivacySavvy discovered the vulnerabilities in travel apps
The PrivacySavv research team discovered multiple ride-sharing and other travel apps to be exposing users’ data as part of a large apps mapping project as one of our 2021 resolutions. Our white-hat researchers use different security tools to test open holes in different systems (used by the general public) for weaknesses. They then thoroughly evaluate each hole for any potential data leakage.
Upon finding a data exposure, our researchers use expert techniques for verifying the databases’ identity alongside potential exposure severity. We then alert the respective database owner about the vulnerability. If possible, we also work with the affected company for quick remediation of the issue.
Our researchers were able to access the database queries of different travel apps as multiple of them were having critical vulnerabilities. Some even had completely unencrypted and unsecured databases.
The purpose of this apps mapping project is to help make the applications everyday users use safer. We, as a whole, want to make the internet a safer place for everybody.
As ethical hackers, we’re not only obliged but also committed to informing a firm or its users when we discover bugs in their online security. That is especially true in cases where the exposed data contains sensitive information of users or companies. As our name PrivacySavvy suggests, the ethics we follow also mean we carry an obligation to the public. We want to make every internet user privacy savvy, and believe everyone deserves to be aware of any potential breach of their data and the implications it could have on their interests.
About our research lab
PrivacySavvy is a rapidly growing VPN and digital security resource center. Our research lab boasts a group of whitehat security researchers that strives to help average internet users defend themselves against ever-evolving cyber threats while educating companies on protecting the users’ data.
