Chinese state-sponsored hackers have found a new way to hide their tracks. They’re hijacking everyday devices in your home and office to mask their malicious activities. The UK’s National Cyber Security Centre just sounded the alarm alongside nine other countries.
This isn’t just another cyber threat warning. It represents a fundamental shift in how Chinese hacking operations work. These groups have moved away from individually purchased infrastructure. Now they rely on vast networks of compromised devices that belong to ordinary people and businesses.
Hijacked home devices power massive spy networks
The NCSC-UK released a joint advisory with agencies from the United States, Australia, Canada, Germany, Japan, the Netherlands, New Zealand, Spain, and Sweden. The warning makes it clear that the majority of Chinese hacking groups have switched tactics.
These threat actors now control enormous botnets consisting primarily of small office and home office routers. Video recorders, internet-powered cameras, and NAS (network-attached storage) equipment also make up these networks.
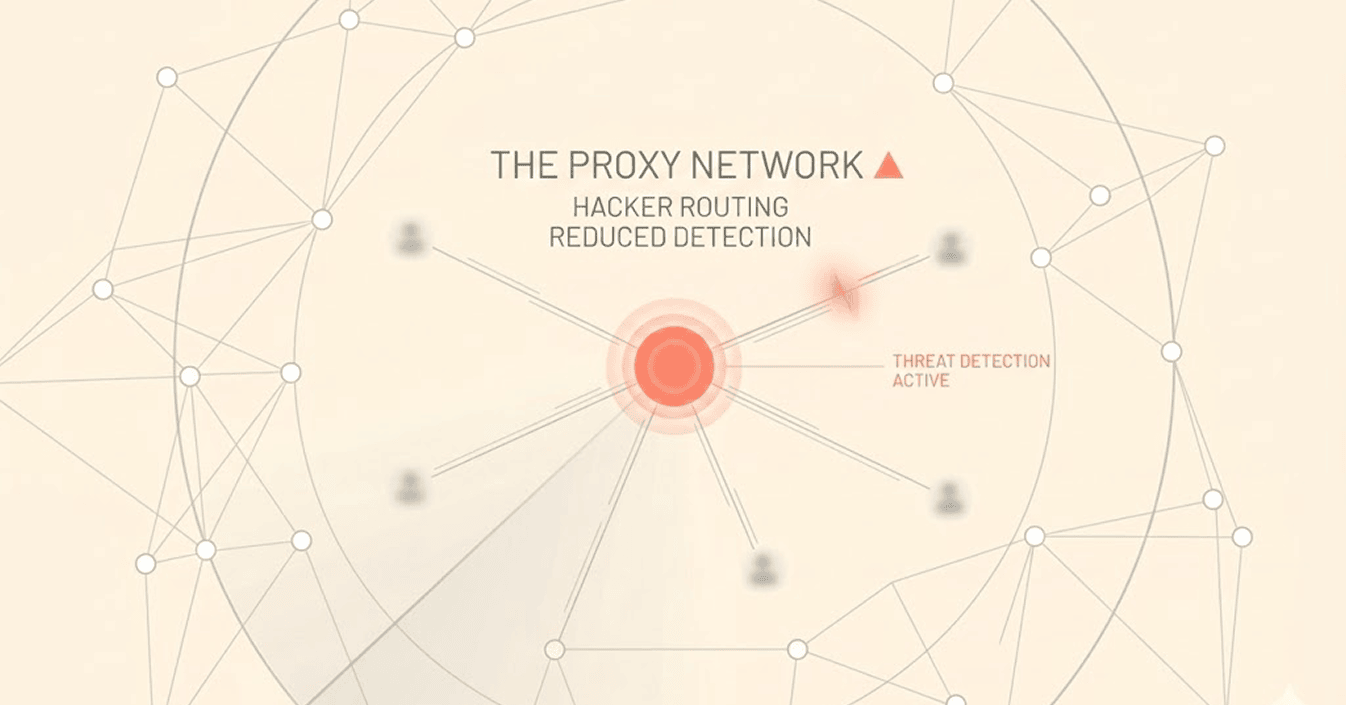
The hackers use these major botnets to route their traffic through chains of compromised devices. They enter the network at one point, pass through multiple intermediate nodes, and exit near their intended target. This technique makes geographic detection nearly impossible.
“The NCSC believes that the majority of China-nexus threat actors are utilizing these networks, that multiple covert networks have been created and are being constantly updated, and that a single covert network could be in use by multiple actors,” the joint advisory states.
These networks consist mainly of compromised Small Office Home Office (SOHO) routers, as well as Internet of Things (IoT) and smart devices.
FBI disrupts massive chinese botnet operations
One particularly large Chinese botnet called Raptor Train infected more than 260,000 devices worldwide in 2024. The FBI linked this network to malicious activity attributed to the Chinese state-sponsored Flax Typhoon hacking group. Researchers also connected it to Chinese company Integrity Technology Group (which authorities sanctioned in January 2025).
In September 2024, the FBI wrecked the Raptor Train thanks to the assistance from “Black Lotus Labs” researchers. Investigators linked the botnet to events targeting entities in multiple sectors. These included the military, government, higher education, telecommunications, defense industrial base, and IT sectors. The attacks focused primarily on organizations in the U.S. and Taiwan.
A distinct network, KV-Botnet, served the Chinese state-supported Volt Typhoon bad actors. This botnet comprised primarily vulnerable Netgear and Cisco routers that were outdated and no longer received security patches.
In January 2024, the FBI wrecked KV-Botnet by cleansing off malware from compromised routers. However, the Volt Typhoon gradually began to revive in November 2024 after an initial failed attempt in February.
NCSC-UK’s Operations Director, Paul Chichester, addressed the severity of this threat. “Botnet operations represent a significant threat to the UK by exploiting vulnerabilities in everyday internet-connected devices with the potential to carry out large-scale cyber attacks,” Chichester explained.
How organizations can protect themselves
According to involved western intelligence groups, traditional defenses based on blocking static lists of malicious IPs are losing strength. These botnets continuously add new compromised nodes, making fixed blocklists obsolete almost immediately.
The risks extend beyond state-sponsored attacks, the dark web data dump of Russian ticketing giant Kassy.ru shows that commercial platforms are equally vulnerable to breaches that expose customer data, highlighting the need for robust security measures regardless of whether the threat is state-sponsored or criminal.
The agencies recommend network defenders at small, medium, and large organizations take several specific steps. They should implement multifactor authentication across all systems. Organizations need to map their network edge devices to understand their attack surface.
Defenders should leverage dynamic threat feeds with indicators for covert networks. Organizations should adopt IP allowlists rather than blocklists. Zero-trust managements offer better protection in this environment. Machine certificate verification adds another layer of security.
The shift to botnet-based infrastructure shows how sophisticated Chinese hacking operations have become. These groups no longer rely on easily identifiable servers or IP addresses. Instead, they hide behind millions of compromised consumer devices. The devices look legitimate because they are legitimate (just hijacked). This makes detection incredibly difficult using traditional methods.