The Layer Two Tunneling Protocol (L2TP) is a protocol used by both Internet Service Providers (ISPs) and Virtual Private Networks (VPNs). The prowess that L2TP can leverage for connectivity is of interest to VPNs, while ISPs can foster VPN operations with it.
L2TP is the outcome of combining two older protocols: Microsoft’s Point-to-Point Tunneling (PPTP) and Cisco’s Layer 2 Forwarding (L2F). The hybrid result, L2TP, combines the best of both worlds and improves upon them significantly. The protocol was born as the last century ended to replace earlier protocols. Technically, it’s the standard RF C26661.
Here’s what you need to know about L2TP:
- It needs to be paired with another protocol to maximize its benefits.
- It’s usually paired with IPSec, which brings security to the data load.
- The combination of L2TP and IPSec opens up a broad spectrum of possibilities regarding security features because it enables the use of AES 256-bit and the 3DES algorithm.
- L2TP’s packets feature double encapsulation, which improves their security. However, it also makes the protocol more taxing on the equipment.
- L2TP’s port of choice is 1701. But once IPSec comes into the mix, various other ports can come alive. For instance, port 500 will manage the Internet Key Exchange (IKE), 4500 for NAT, and 1701 (the original one) for L2TP traffic.
How does L2TP work?
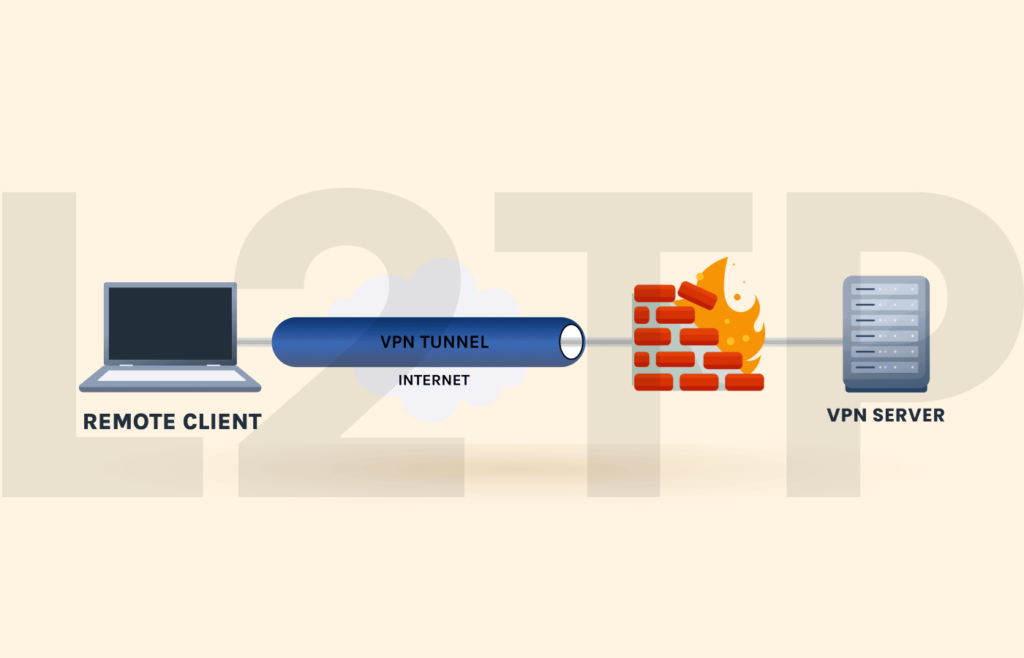
L2TP creates a tunnel between two endpoints on the internet: the L2TP Access concentrator (LAC) and the L2TP network server (LNS).
Once the connection between the two becomes active, the protocol enables an encapsulated PPP layer.
Then, the next step is initializing the PPP connection from the ISP to the LAC. When the LAC accepts it, the PPP link comes online.
Next, a new free slot becomes assigned inside the tunnel, and the request goes to the LNS.
At this point, the connection needs authentication. Once the authenticity is established, a virtual PPP interface comes alive. And now, all the link frames can travel around the tunnel freely.
The last step completes at the LNS endpoint, where the protocol processes the accepted frames and removes the L2TP encapsulation.
How are IPSec and L2TP protocols related?
Maybe you often find “IPSec” whenever you read about the L2TP protocol. Perhaps, you may frequently encounter the term “L2TP/IPSec” among connection protocols when looking for L2TP in a VPN.
IPSec (the acronym for “Internet Protocol Security”) is a separate connection protocol frequently used with L2TP.
As the name suggests, IPSec ensures “security” to the “internet protocol” by encrypting the data packets exchanged between two computers in a network. Hence, using IPSec in tandem with L2TP improves a connection’s security.
L2TP doesn’t perform at its best when the network deploys it alone. However, it becomes more robust, reliable, and efficient when running with IPSec. That’s why most VPN providers deploy the two protocols together to provide improved security to the users.
The L2TP/IPSec pairing – Looking under the hood
Since IPSec is a protocol that brings out the best in L2TP, it’s good to understand how these two protocols interact and potentiate each other. So here’s how it goes:
- The negotiation for the IPSec security association (SA) occurs. (Here, “security association” is the agreement of shared security attributes between two networks to ensure secure data exchange.) This IPSec SA negotiation typically happens via IKE over port 500.
- The protocol establishes the “Encapsulating Security Payload” (ESP) process as the transport mode. This ESP operates on top of IP (with IP protocol number 50), establishing a secure channel between two entities (such as the client and the VPN server) in a network. However, until this point, no tunneling happens.
- The IPSec protocol has completed its job at this point, so this is where L2TP comes alive. It’s in charge of creating the tunnel between both endpoints. L2TP sets the tunnel up via TCP port 1701. The negotiation for the tunnel occurs over IPSec encryption.
L2TP protocol connection speeds
Every internet user likes to have the best possible connection speeds, even when prioritizing security. So, you might wonder how fast L2TP is.
In essence, the L2TP protocol can be exceedingly fast when used alone, as it only creates a tunnel for data exchange, employing no encryption.
But we can’t use it singly for the same reason. Otherwise, doing so would render the connection vulnerable to interception by third parties and snoopers.
That is why the service providers often pair it with IPSec to introduce encryption. However, the speeds will suffer since you are almost always using two protocols in tandem. But it won’t be a noticeable impact if you have a good base speed.
For instance, if you get 100mbps or more from your ISP and have an impressive CPU, you won’t notice any of the work both protocols are doing.
L2TP Protocol pros and cons
Now that you know how fast L2TP is while ensuring almost no security on its own, you might wonder if it is worth adopting at all.
To answer this concern, let’s look at both sides of the coin.
L2TP advantages
- Provides excellent security when paired with IPSec.
- Compatible with most devices and operating systems. (You will find it available as the built-in protocol in Windows and macOS.)
- Easy to configure.
- Supports multithreading for improved performance.
- The double encapsulation feature ensures improved data verification.
Disadvantages of L2TP
- As an individual protocol, it’s fragile in terms of security.
- According to Edward Snowden, the NSA knows how to crack this protocol successfully. (Of course, we will never be able to prove Snowden’s assertion. But we do know that the protocol is weak.)
- Double encapsulation in L2TP requires more resources, which can be slightly slower than the alternatives.
- It may often encounter hindrances by NAT firewalls unless it is set up to bypass the filters.
L2TP VPN key features
An L2TP VPN has some unique features to offer you. Here they are:
- Secure connection. You can deploy AES-based or 3DES-based encryption within the L2TP tunnel. AES is the military-grade encryption algorithm that’s the standard among VPNs and intelligence agencies globally.
- Improved link stability. Once you link to your VPN’s server, you want things to keep running smoothly. L2TP makes for more stable links because the configuration goes through the UDP port 1701, port 500 for key exchange, and 4500 for NAT.
Is this getting too geeky for your taste? Don’t worry; you don’t need to understand all the technical details to enjoy the advantages of this protocol.
The thing to remember is: if your VPN offers you this option, take it. It’s excellent for security without losing too much speed.