A MAC address (Media Access Control address) is a series of numbers and letters (digital fingerprint) that helps networks recognize and communicate with your device. Unlike an IP address (that keeps changing), a MAC address is usually hard-coded into the device’s hardware, making it a permanent identity marker.
Knowing your MAC address can be useful for troubleshooting, setting up secure connections, and filtering devices on a Wi-Fi network. You can also enhance privacy with MAC randomization.
But the question is, how can you find it? Well, the process isn’t complicated; you only need to follow the right steps. In this guide, we’ll explain what a MAC address is, why it matters, and show you simple steps to find yours on different devices.
What is a MAC address?

The MAC (Media Access Control) address is a distinct identifier allocated to network interfaces that enables them to communicate internally within the network.
It contains 48 bits and usually appears as six pairs of hexadecimal characters, thereby creating over 281 trillion likely combinations. Operating as a hardware location marker, the MAC identification performs an essential function in networking protocols at the OSI model’s data link level.
How does a MAC address work?
The key purpose of a MAC address is to allow devices within the same local network to differentiate and interact with one another. The source and destination MAC addresses are utilized while transmitting data over this network, guaranteeing that the data reaches its intended target.
This addressing method streamlines delivering data packets throughout the network, letting devices recognize and handle information using these distinctive identifiers. Therefore, having a MAC address is essential in ensuring that effective networking communication operations run smoothly.
Types of MAC addresses
There are three primary types of MAC addresses. They include:
- Unicast MAC address: A Unicast MAC Address is an address allotted for solitary use by a Network Interface Card (NIC) and is utilized exclusively for one-to-one communication within a network.
- Broadcast MAC address: The Broadcast MAC address facilitates communication between manufacturers and users by ensuring adequate information transmission to all connected devices in a network segment.
- Multicast MAC address: Multicast MAC addresses support quick data transfer to a different device with similar interests or information needs. As a result, you can successfully communicate with multiple network devices simultaneously.
Does a device have more than one MAC address?
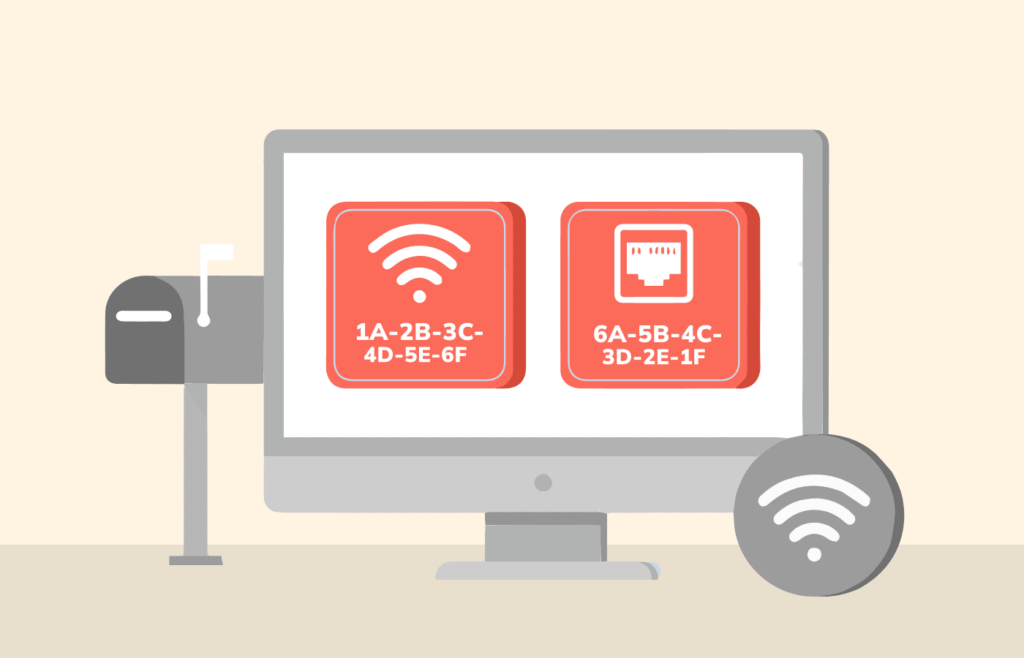
Certainly, devices can possess more than one MAC address. This commonly occurs in devices with several network interfaces, like laptops integrated with wired and wireless connections.
Every individual interface, like Wi-Fi and Ethernet, has its own distinct MAC address assigned to it. Furthermore, virtualization technologies, including Virtual Machines (VMs), might contain unique MAC addresses separate from the host device.
Aliasing or cloning enables Network Interface Cards (NICs) to support several MAC addresses. This feature is beneficial in diverse networking situations, including load balancing, network redundancy, and virtualization setups that require a unique identifier for each virtual instance.
A laptop can possess a MAC address for its wired Ethernet port and wireless adapter. Each virtual machine could receive a distinct MAC address to facilitate communication in virtualized surroundings.
It is essential to remember that despite a device having several MAC addresses, every address remains a distinctive identifier for its corresponding network interface. Consequently, the device can participate in separate communication pathways within the same network and improve overall connectivity while adjusting efficiently to different networking scenarios.
Where can I find my MAC Address?
When configuring networks, you must know the MAC address of your device. It would help if you had this identification to establish a secure network, fix connectivity issues, or set specific protocols. However, locating this unique identity may differ depending on your operating system and device type.
To simplify things for you, we have compiled precise guidelines below that outline how Windows, macOS, iOS, and Android users can effortlessly access their MAC addresses, providing comprehensive networking insights at all times.
On Windows
Two separate steps apply here to find your MAC address on Windows devices. The first steps showcase how to find your MAC address using a Windows 10 device, while the others explain how to find your MAC address using earlier Windows versions.
- Click on the Internet icon (appearing as a WiFi symbol or an Ethernet icon) in the bottom-right corner of your screen.
- Now click on the “Network and Internet settings” option.
- On the window that appears, click the “Properties” button below your network’s name.
- Scroll down to find “Properties,” where you will find a list of various network details, including your MAC address or Physical address.
For earlier Windows versions, you can find your MAC address by following these steps:
- Press the Windows key + R to open the run dialog.
- Type “cmd” and press enter to open the command prompt.
- The command to enter is “getmac /v /fo list.” Remember to include the spaces as you input the command and press enter in the new window.
- Then, on the interface that displays all your network connections, you will find numbers alongside your “Physical address.”
On macOS

- Click on the Apple logo in the top-left corner of your screen to open the Apple menu.
- Open “System Preferences” and select “Network.”
- Select whether you want to obtain the MAC address for a WiFi or Ethernet network connection.
- In the lower right corner, click the “Advanced” button.
- Go to the “Hardware” tab, and you will find your MAC address there.

On Android
- Open “Settings” on your Android device.
- Scroll down and select “About phone” or “About device.”
- Look for “Status” or “Hardware Information” in the menu.
- Find the “Wi-Fi MAC address” or “Ethernet MAC address” entry.
Note: The MAC address is usually displayed in the form of six pairs of alphanumeric characters.
On iOS
- Open “Settings” on your iOS device.
- Tap on “General.”
- Select “About.”
- Scroll down to find the “Wi-Fi Address,” your MAC address for the Wi-Fi interface.
NOTE: If you are trying to find the MAC address of your cellular data connection, it may not be readily available in your device settings. Therefore, depending on your iOS version and carrier specifications, you might have to contact your cellular provider or navigate through the device’s cellular settings for this information.
Spoofing your MAC address
Spoofing refers to modifying a network interface’s MAC address to replicate another device’s specific identifier. One may try MAC address spoofing on a device for good reasons related to privacy, security, or altering networks.
For instance, regular internet users may wish to change their MAC addresses to circumvent network restrictions and ensure online anonymity. Likewise, a threat actor may perform MAC address spoofing to carry out targeted digital attacks.

Though there are some situations where changing your device’s MAC can be valid, we must acknowledge its potential unethical application, like gaining unsanctioned entry into secure systems and involving oneself maliciously online.
To prevent misuse that could arise from false identification via MAC changes, system administrators usually implement protective measures to detect and prevent efforts to utilize these techniques carelessly.
It should go without saying that responsible conduct based on legal compliance should always direct our use of the strong safety regulations surrounding such processes in public and private institutions.
Sharing a license
Sharing your software license with others without considering your MAC address could result in unauthorized use and legal troubles. Usually, licenses are bound to a particular device’s MAC address for security purposes. Being the unique identifier for network interfaces, a MAC address ensures that a licensed software works only on authorized devices.
Sharing licenses randomly may flout service terms or licensing contracts and weaken compliance with policies concerning the rightful usage of the software. Thus, adhering to licensing conditions is imperative, as sharing them improperly can lead to ethical and lawful lapses in software utilization.
Stop trackers
With various entities relentlessly seeking access to online data, privacy has become a primary motivation for concealing one’s MAC address in the modern digital landscape.
Even though your MAC address may not directly disclose your identity, it can link your online activities together and provide details about you that websites use to create thorough user profiles. One way to maintain anonymity while browsing is by using address spoofing.
Fortunately, most websites do not routinely obtain users’ MAC addresses; they usually interact with their IP addresses instead. Individuals frequently alter their IP addresses using VPNs or other methods to increase privacy further. This alternative will help ensure safer browsing experiences without any risks associated with revealing personal information.
How are MAC and IP addresses distinct from each other?

MAC (Media Access Control) and IP (Internet Protocol) addresses are essential elements of networking that perform unique roles. The following is a breakdown of how they differ:
MAC address
Network interfaces, such as Wi-Fi adapters or network cards, are assigned hardware identifiers known as MAC addresses. These unique addresses guarantee global distinctiveness and prevent overlapping device identification. Operating at Layer 2 (the Data Link Layer in the OSI model), this addressing system enables communication among devices within a shared network segment.
MAC address format includes 48 bits, commonly expressed in six pairs of hexadecimal digits to designate devices on this segment. Manufacturers usually embed these addresses into their interfaces; however, users can also manually alter MAC addresses for various reasons despite the rarity of this practice.
IP address
IP addresses are allocated to devices in a network as logical identifiers for communication. Although they remain distinct within that particular network, IP addresses can be reproduced across numerous networks. At Layer 3, also known as the Network Layer of OSI model architecture, two formats are available: IPv4 and IPv6.
IPv4 has a total bit count of 32, and IPv6 has an extended range with a bit count of 128 – both in decimal form. Utilizing these addresses greatly assists data transmission between networks, making them crucial for efficient routing throughout the internet infrastructure.
FAQs
An IP address identifies a device’s network connection. In contrast, a MAC address indicates a device’s physical location, uniquely identifying each device on a network.
To access a MAC address list, check the network settings on your device. Then, refer to the command line (using “
” for Windows or “
” for macOS) or enter your router’s web interface. Routers typically list attached devices with their respective MAC addresses, which details network composition and assists with device management tasks.
It has 48 bits and is typically denoted as a sequence of 12 digits in hexadecimal form (ranging from 0 to 9 or A to F). These are frequently divided into groups separated by dashes or colons. To illustrate, the MAC code “001B638445E6” could be rendered either as “00:1b:63:84:45:e6” or “00-1B-63-84-45-E6.”
